350-401 Practice Questions
Implementing Cisco Enterprise Network Core Technologies (350-401 ENCOR)
Last Update 5 hours ago
Total Questions : 432
Dive into our fully updated and stable 350-401 practice test platform, featuring all the latest CCNP Enterprise exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNP Enterprise practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 350-401. Use this test to pinpoint which areas you need to focus your study on.
Which feature is needed to maintain the IP address of a client when an inter-controller Layer 3 roam is performed between two WLCs that are using different mobility groups?
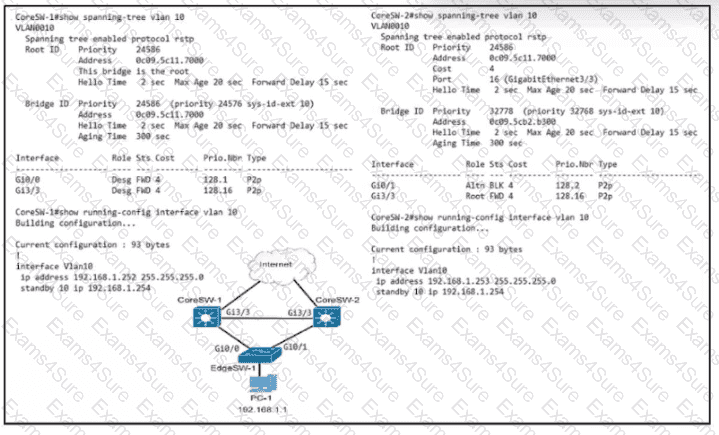
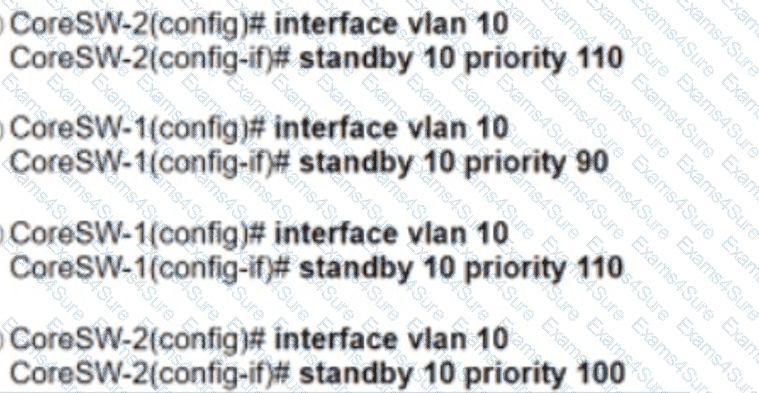
Refer to the exhibit. Which configuration causes the traffic from PC-1 to the internet to use the link between CoreSW-1 and CoreSW-2 when both switches are up?
In a Cisco SD-Access solution, which component offers the Anycast Gateway service?
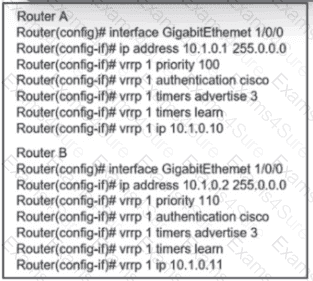
Refer to the exhibit. An engineer must adjust the configuration so that Router A becomes the active router. Which commands should be applied to router A? (Choose two)
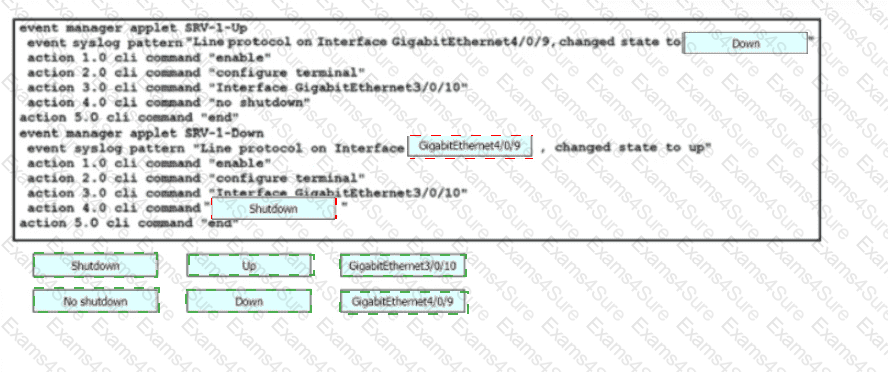
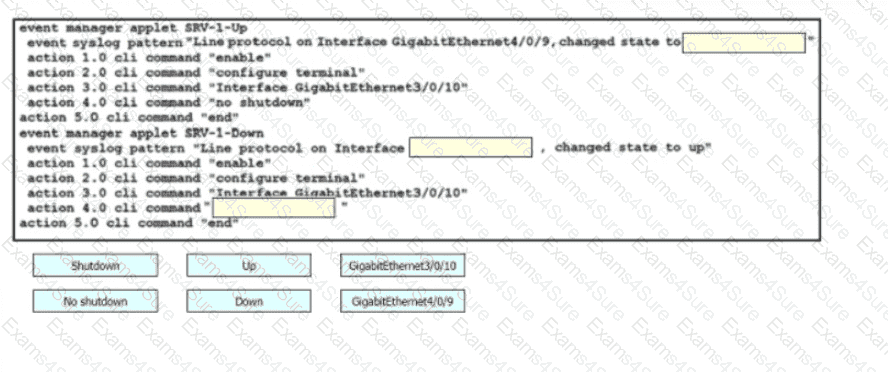
Drag and drop the snippets onto the blanks within the code to construct a script that brings up the failover Ethernet port if the primary port goes down and also shuts down the failover port when the primary returns to service. Not all options are used.
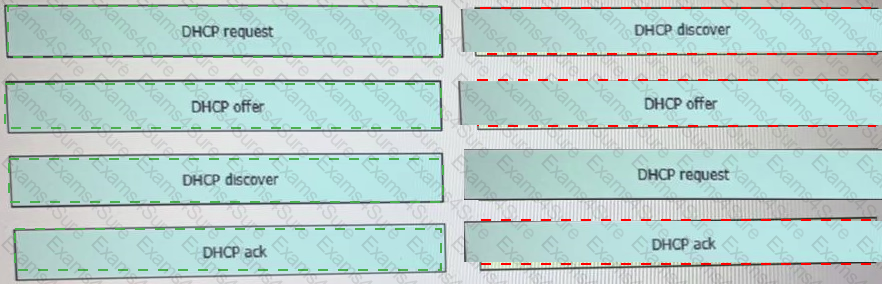
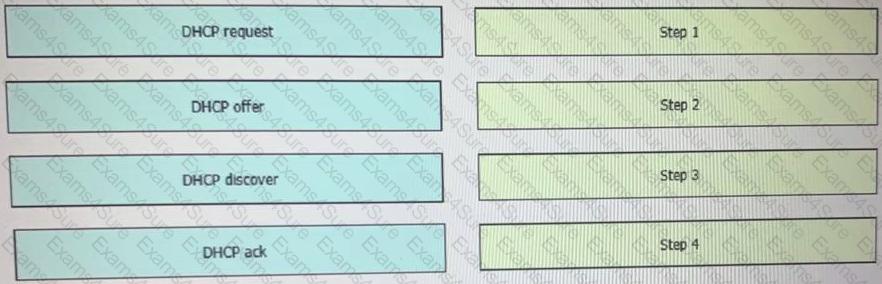
Drag and drop the DHCP messages that are exchanged between a client and an AP into the order they are exchanged on the right.
Which technique is used to protect end user devices and data from unknown file behavior?