
SY0-701 Practice Questions
CompTIA Security+ Exam 2026
Last Update 1 day ago
Total Questions : 840
Dive into our fully updated and stable SY0-701 practice test platform, featuring all the latest CompTIA Security+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA Security+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about SY0-701. Use this test to pinpoint which areas you need to focus your study on.
Which of the following describes when a user installs an unauthorized application by bypassing the authorized application store and installing a binary file?
An administrator needs to perform server hardening before deployment. Which of the following steps should the administrator take? (Select two).
A security administrator recently reset local passwords and the following values were recorded in the system:
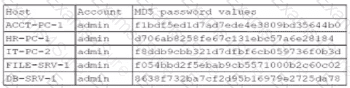
Which of the following in the security administrator most likely protecting against?
Which of the following actions must an organization take to comply with a person ' s request for the right to be forgotten?
A security engineer needs to quickly identify a signature from a known malicious file. Which of the following analysis methods would the security engineer most likely use?
An IT manager is increasing the security capabilities of an organization after a data classification initiative determined that sensitive data could be exfiltrated from the environment. Which of the following solutions would mitigate the risk?
An organization is implementing a COPE mobile device management policy. Which of the following should the organization include in the COPE policy? (Select two).
Which of the following should be deployed on an externally facing web server in order to establish an encrypted connection?
Which of the following actions best addresses a vulnerability found on a company ' s web server?
Which of the following considerations is the most important for an organization to evaluate as it establishes and maintains a data privacy program?
Which of the following should a security administrator adhere to when setting up a new set of firewall rules?
An accounting employee recently used software that was not approved by the company. Which of the following risks does this most likely represent?
Which of the following security controls is a company implementing by deploying HIPS? (Select two)
Which of the following risk management strategies should an enterprise adopt first if a legacy application is critical to business operations and there are preventative controls that are not yet implemented?
A customer has a contract with a CSP and wants to identify which controls should be implemented in the IaaS enclave. Which of the following is most likely to contain this information?



