200-301 Practice Questions
Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1
Last Update 4 days ago
Total Questions : 1240
Dive into our fully updated and stable 200-301 practice test platform, featuring all the latest CCNA exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-301. Use this test to pinpoint which areas you need to focus your study on.
Refer to the exhibit.
If R1 receives a packet destined to 172.161.1, to which IP address does it send the packet?
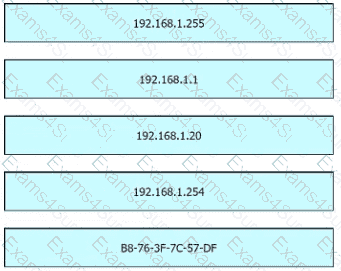
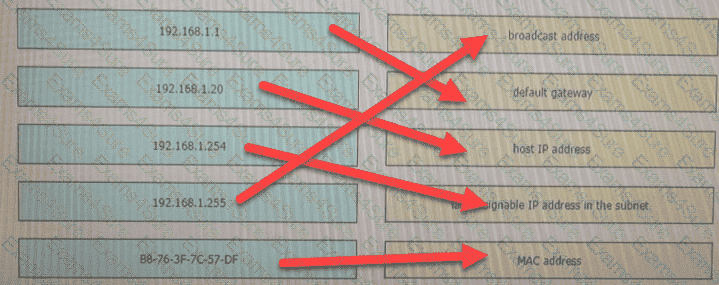
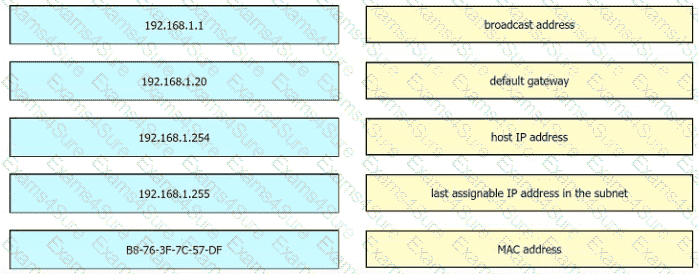
Refer to the exhibit.
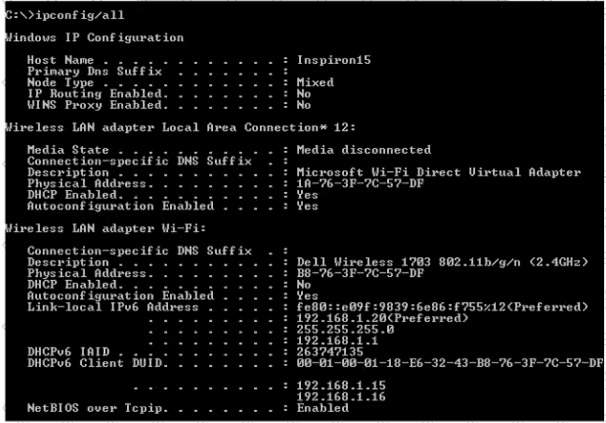
An engineer is tasked with verifying network configuration parameters on a client workstation to report back to the team lead. Drag and drop the node identifiers from the left onto the network parameters on the right.
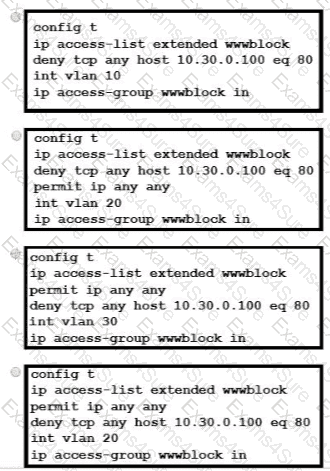
Refer to the exhibit.
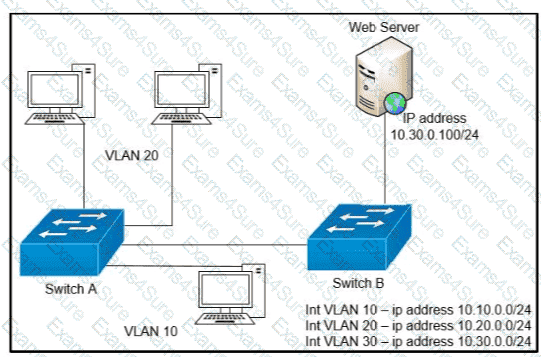
A network engineer must block access for all computers on VLAN 20 to the web server via HTTP All other computers must be able to access the web server Which configuration when applied to switch A accomplishes this task?
What is the difference in data transmission delivery and reliability between TCP and UDP?
Refer to the exhibit.
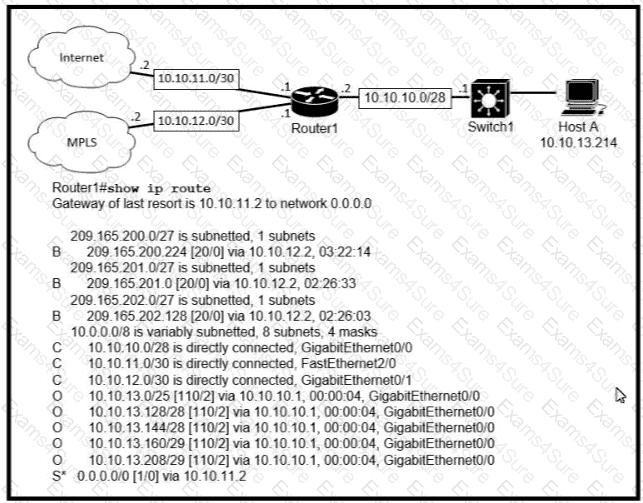
Which prefix does Router 1 use for traffic to Host A?
Which port type supports the spanning-tree portfast command without additional configuration?
Which security element uses a combination of one-time passwords, a login name, and a personal smartphone?
An engineer must update the configuration on two PCs in two different subnets to communicate locally with each other. One PC is configured with IP addressss 192.168.25.128/25 and the other with 192.168.25.100/25. Which network mask must the engineer configure on both PCs to enable the communication?
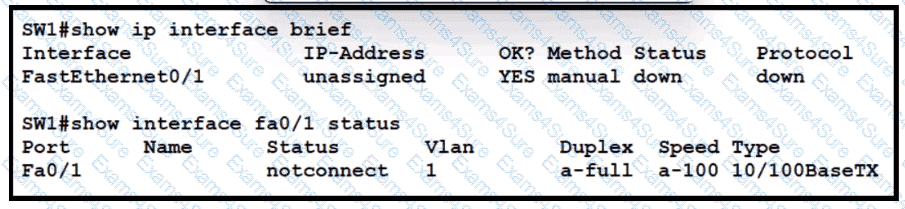
Exhibit.
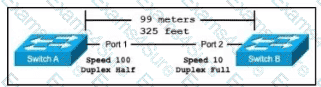
The switches are connected via a Cat5 Ethernet cable that was successfully tested. The Interfaces are configured as access ports and are both in a ' down " status. What is the cause of this issue?
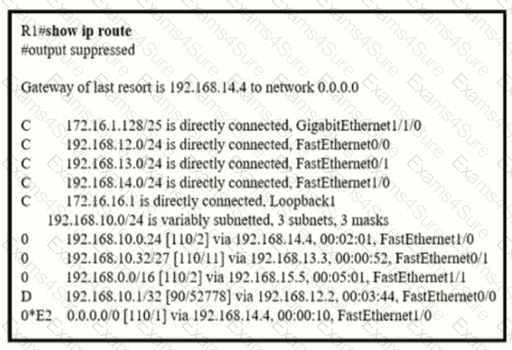
Refer to the exhibit.
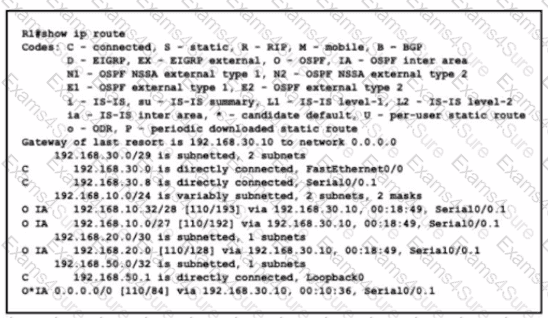
What is the metric for the route to the 192.168.10.33 host?
An engineer must configure an OSPF neighbor relationship between router R1 and R3 The authentication configuration has been configured and the connecting interfaces are in the same 192.168 1.0/30 sublet. What are the next two steps to complete the configuration? (Choose two.)
An on-site service desk technician must verify the IP addressss and DNS server information on a users Windows computer. Which command must the technician enter at the command prompt on the user ' s computer?
Which characteristic differentiates the concept of authentication from authorization and accounting?
Which statement correctly compares traditional networks and controller-based networks?
Which two features are provided by Ansible in network automation? (Choose two.)
Refer to the exhibit.
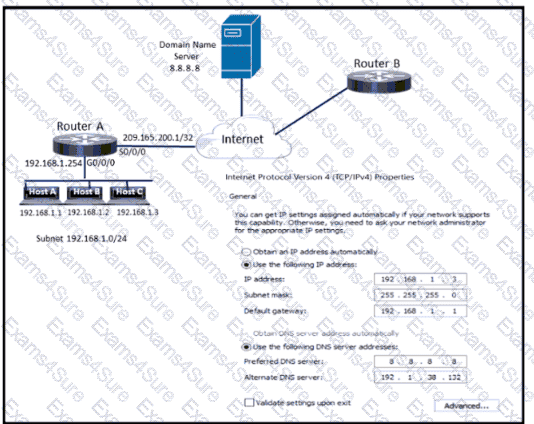
Which configuration parameter is preventing host C from reaching the internet?