200-301 Practice Questions
Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1
Last Update 4 days ago
Total Questions : 1240
Dive into our fully updated and stable 200-301 practice test platform, featuring all the latest CCNA exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-301. Use this test to pinpoint which areas you need to focus your study on.
Which WLC management connection type is vulnerable to man-in-the-middIe attacks?
Refer to the exhibit.
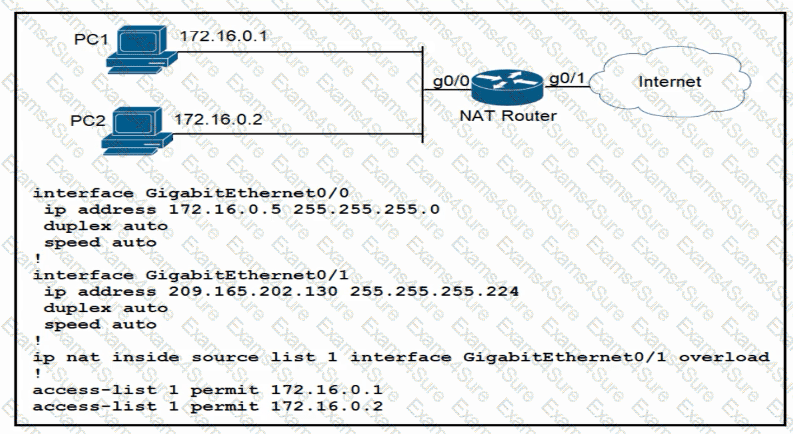
How should the configuration be updated to allow PC1 and PC2 access to the Internet?
Refer to the exhibit.
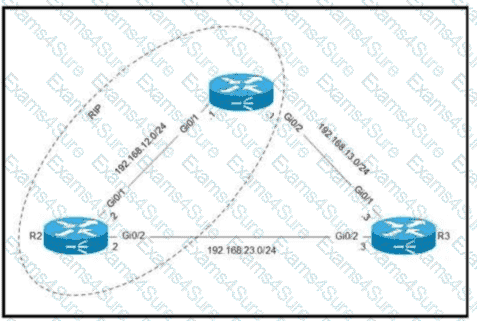
Routers R1 and R2 are configured with RIP as the dynamic routing protocol. A network engineer must configure R1 with a floating static route to serve as a backup route to network 192.168.23.0. Which command must the engineer configure on R1?
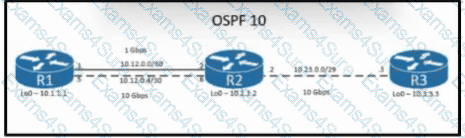
Refer to the exhibit. The loopback IP of R3 has been learned via the two interfaces on R1. R1 is configured with a reference bandwidth of 10 Gbps. Based on the metric calculations, which next hop IP would be used for outgoing routing?
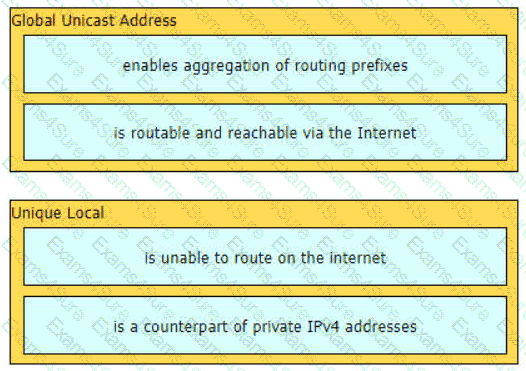
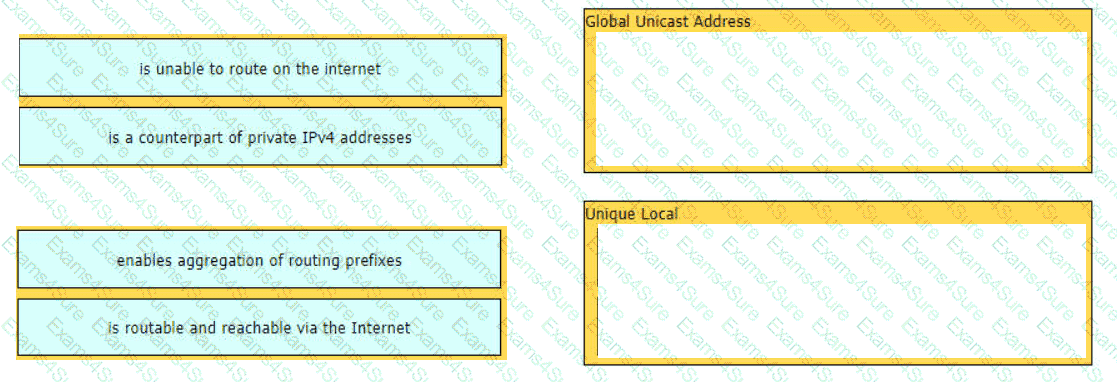
Drag and drop the characteristic from the left onto the IPv6 address type on the right.
What are two capabilities provided by VRRP within a LAN network? (Choose two.)
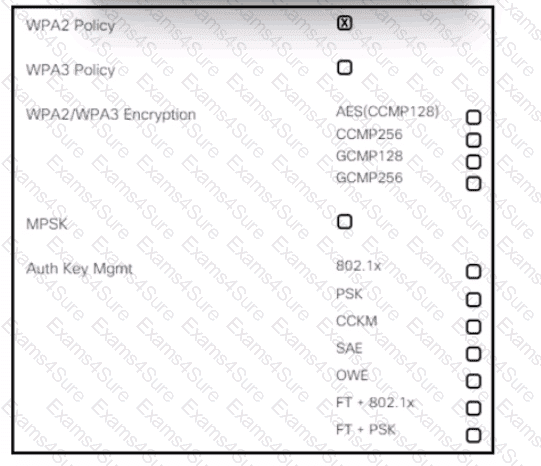
Refer to the exhibit. An engineer is creating a secure pre-shared key based SSID using WPA2 for a wirelesss network running on 2.4 GHz and 5 GHz. Which two tasks must the engineer perform to complete the process? (Choose two.)
What is an advantage of using SDN versus traditional networking when it comes to security?
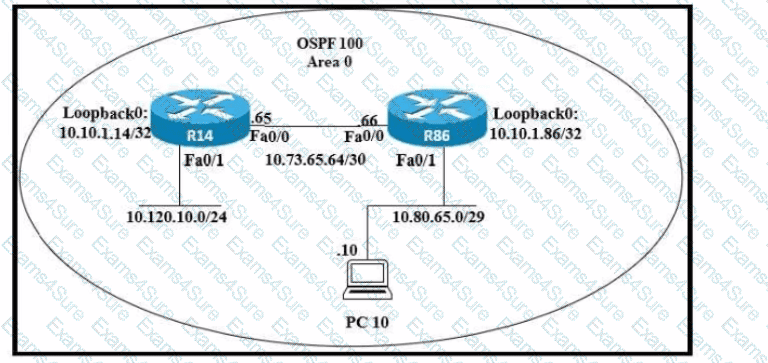
Refer to the exhibit. An engineer just installed network 10.120.10.0/24. Which configuration must be applied to the R14 router to add the new network to its OSPF routing table?
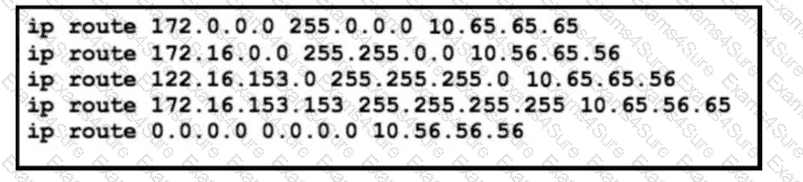
Refer to the exhibit. The static routes were implemented on the border router. What is the next hop IP addressss for a ping sent to 172.16.153.154 froin the border router?
Which QoS queuing method discards or marks packets that exceed the desired bit rate of traffic flow?
A client experiences slow throughput from a server that is directly connected to the core switch in a data center. A network engineer finds minimal latency on connections to the server, but data transfers are unreliable, and the output of the show Interfaces counters errors command shows a high FCS-Err count on the interface that is connected to the server. What is the cause of the throughput issue?
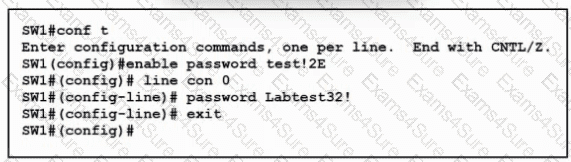
Refer to the exhibit. A VTY password has been set to Labtest32! for remote access. Which commands are required to allow only SSH access and to hide passwords in the running configuration?