200-301 Practice Questions
Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1
Last Update 4 days ago
Total Questions : 1240
Dive into our fully updated and stable 200-301 practice test platform, featuring all the latest CCNA exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-301. Use this test to pinpoint which areas you need to focus your study on.
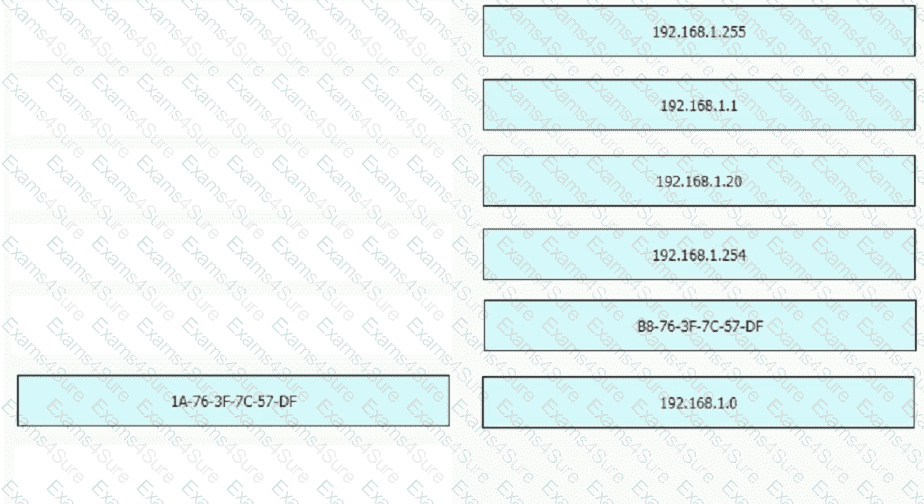
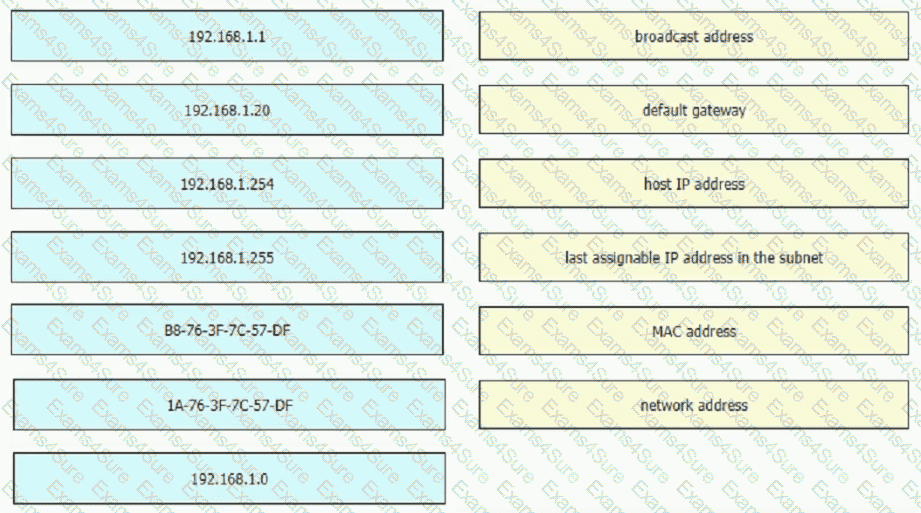
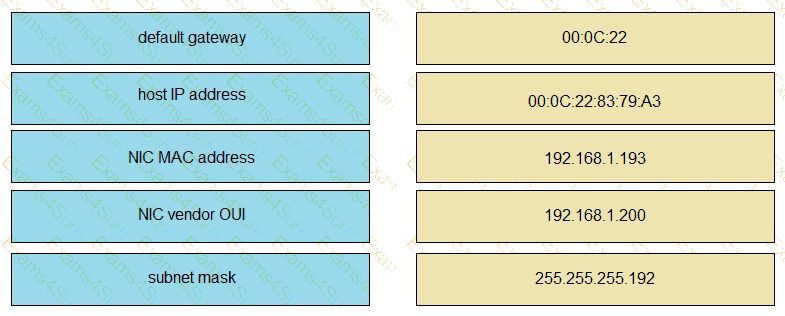
Refer to the exhibit.
An engineer is required to verify that the network parameters are valid for the user wireless LAN connectivity on a /24 subnet. Drag and drop the values from the left onto the network parameters on the right. Not all values are used.
What are two recommendations for protecting network ports from being exploited when located in an office space outside of an IT closer? (Choose two.)
Which protocol does an access point use to draw power from a connected switch?
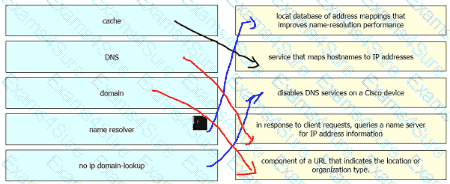
Drag and drop the DNS lookup components from the left onto the functions on the right.

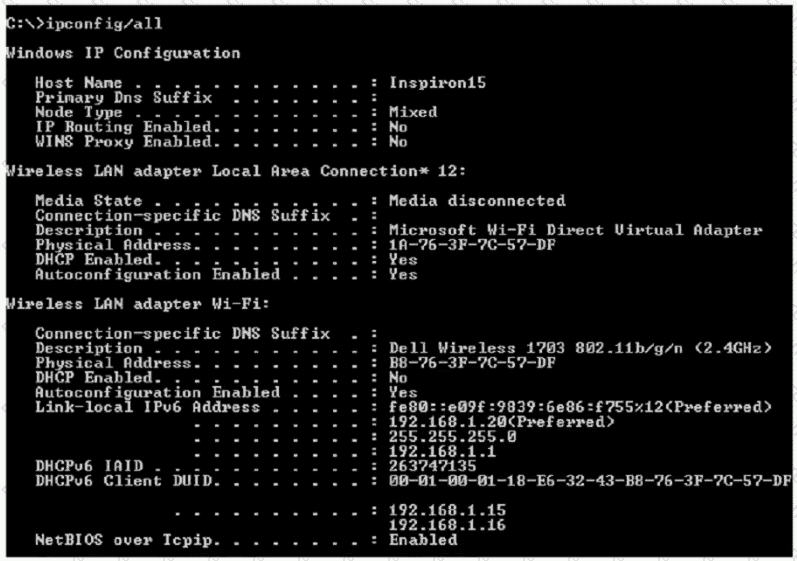
Refer to the exhibit.
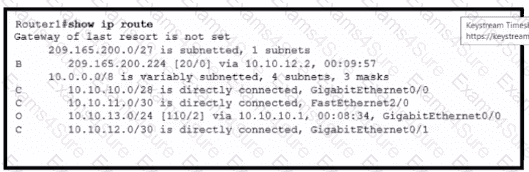
Which action is taken by the router when a packet is sourced from 10.10.10.2 and destined for 10.10.10.16?
Which two primary drivers support the need for network automation? (Choose two.)
Refer to the exhibit.
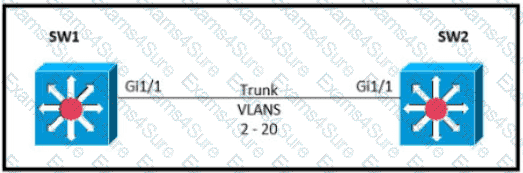
Which command must be executed for Gi1.1 on SW1 to become a trunk port if Gi1/1 on SW2 is configured in desirable or trunk mode?
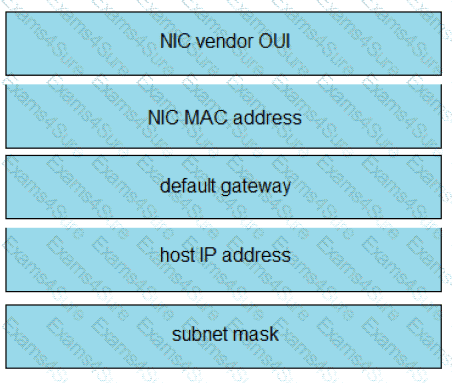
Refer to the exhibit.
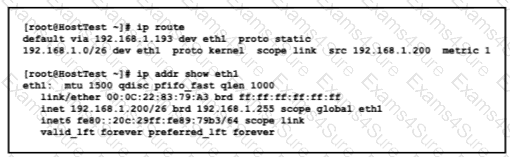
Drag and drop the networking parameters from the left onto the correct values on the right.
In QoS, which prioritization method is appropriate for interactive voice and video?
A Cisco IP phone receive untagged data traffic from an attached P
C.
Which action is taken by the phone?Refer to the exhibit.
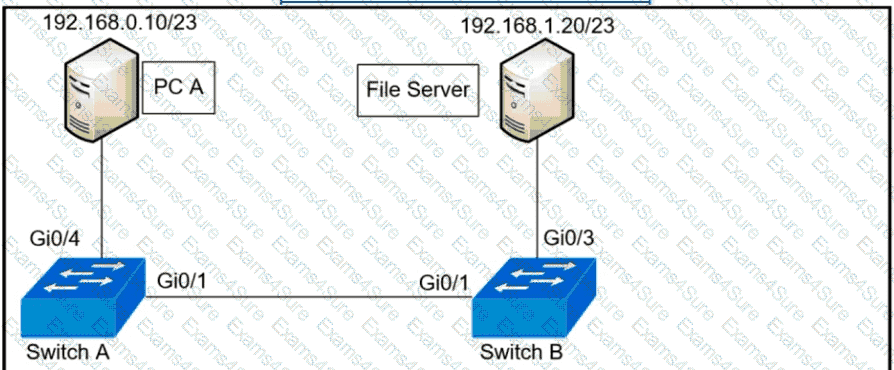
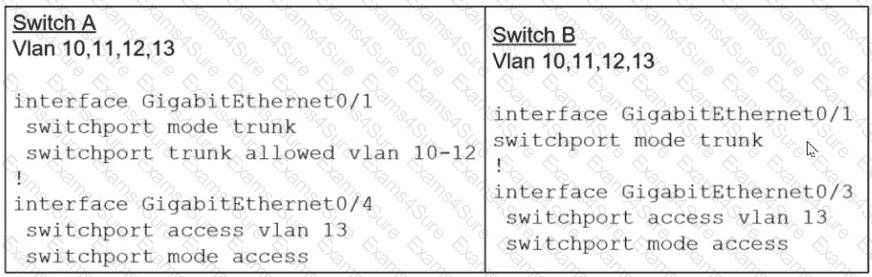
A network administrator assumes a task to complete the connectivity between PC A and the File Server. Switch A and Switch B have been partially configured with VLAN 10, 11, 12, and 13. What is the next step in the configuration?
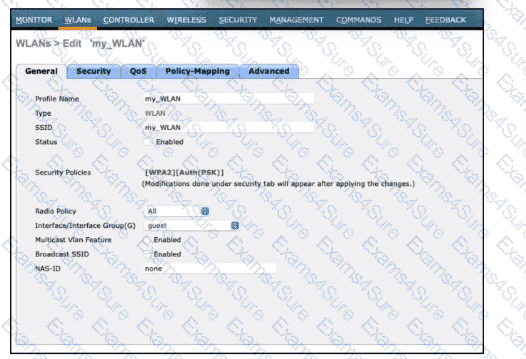
Refer to the exhibit. The My_WLAN wirelesss LAN was configured with WPA2 Layer 2 PSK security. Which additional configuration must the administrator perform to allow users to connect to this WKAN on a different subnet called Data?
What is the purpose of configuring different levels of syslog for different devices on the network?
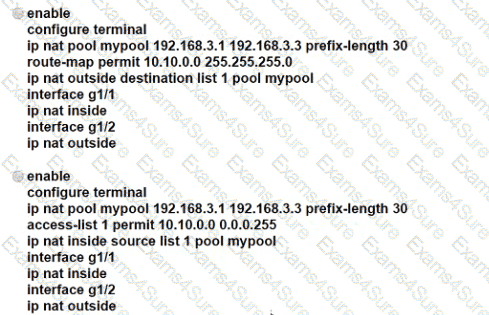
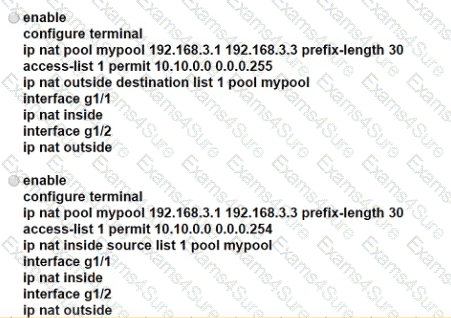
An engineer is configuring NAT to translate the source subnet of 10.10.0.0/24 to any of three addresses 192.168.30.1, 192.168.3.2, 192.168.3.3 Which configuration should be used?
How does CAPWAP communicate between an access point in local mode and a WLC?
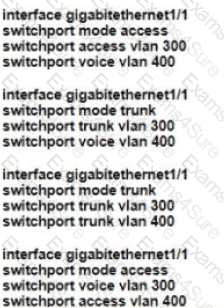
Refer to the exhibit.
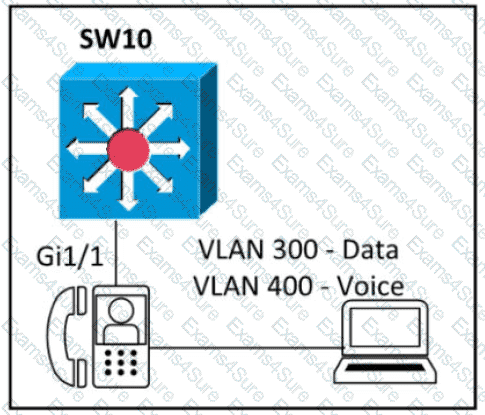
An engineer must configure GigabitEthernet1/1 to accommodate voice and data traffic Which configuration accomplishes this task?
Refer to the exhibit.
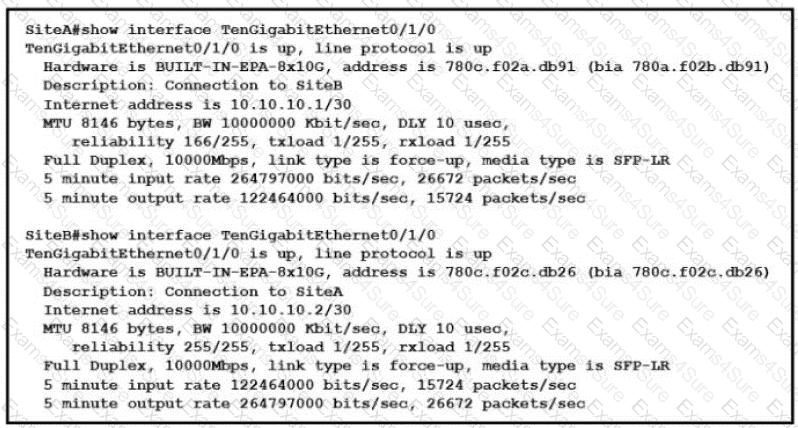
Shortly after SiteA was connected to SiteB over a new single-mode fiber path users at SiteA report intermittent connectivity issues with applications hosted at SiteB What is the cause of the intermittent connectivity issue?
Refer to the exhibit.
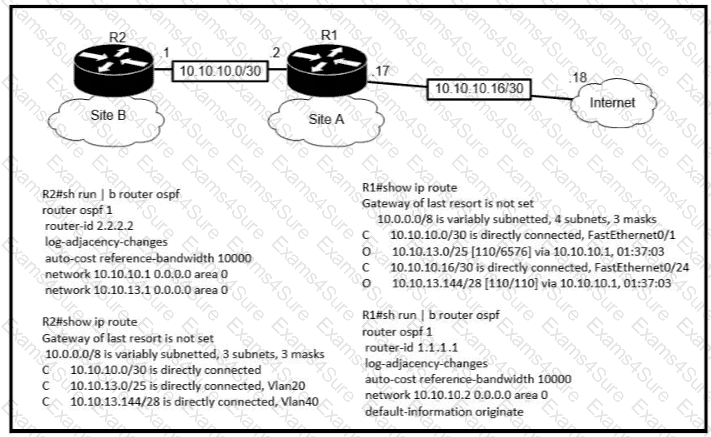
An engineer is bringing up a new circuit to the MPLS provider on the Gi0/1 interface of Router1 The new circuit uses eBGP and teams the route to VLAN25 from the BGP path What s the expected behavior for the traffic flow for route 10.10.13.0/25?
An organization developed new security policies and decided to print the policies and distribute them to all personnel so that employees review and apply the policies. Which element of a security program is the organization implementing?