200-301 Practice Questions
Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1
Last Update 4 days ago
Total Questions : 1240
Dive into our fully updated and stable 200-301 practice test platform, featuring all the latest CCNA exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-301. Use this test to pinpoint which areas you need to focus your study on.
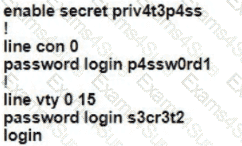
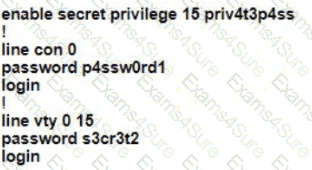
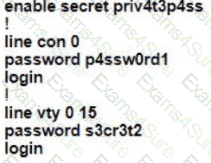
A Cisco engineer is configuring a factory-default router with these three passwords:
• The user EXEC password for console access is p4ssw0rd1
• The user EXEC password for Telnet access is s3cr3t2
• The password for privileged EXEC mode is pr1v4t3p4ss Which command sequence must the engineer configured
A)
B)
C)
D)

Refer to the exhibit.
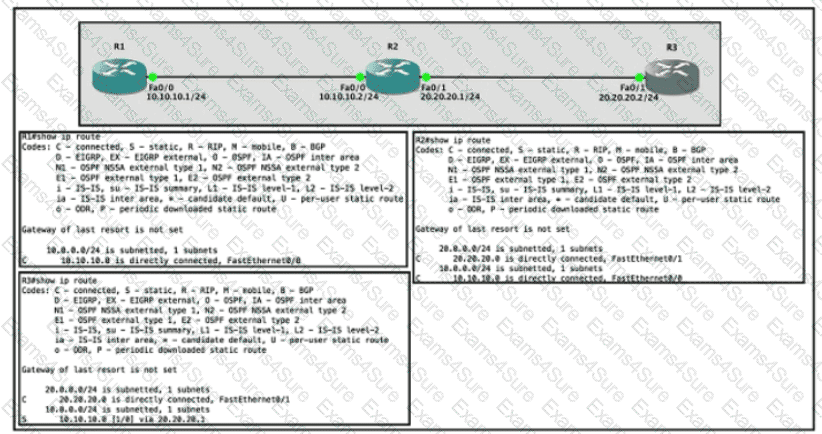
Router R1 Fa0/0 is unable ping router R3 Fa0/1.
Which action must be taken in router R1 to help resolve the configuration issue?

Refer to the exhibit. Each router must be configured with the last usable IP address in the subnet. Which configuration fulfills this requirement?

Which two wireless security standards use Counter Mode with Cipher Block Chaining Message Authentication Code Protocol for encryption and data integrity ' ? (Choose two.)
Refer to the exhibit.
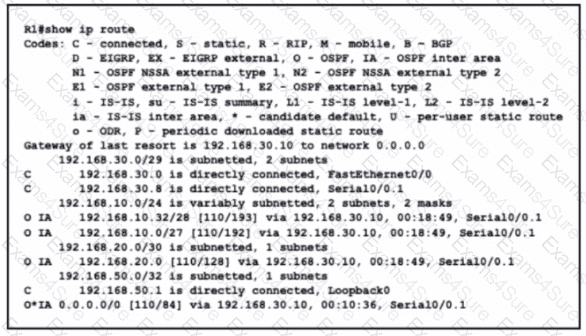
What is the metric of the route to the 192.168.10.33/28 subnet?
An engineer configures interface Gi1/0 on the company PE router to connect to an ISP Neighbor Discovery is disabled
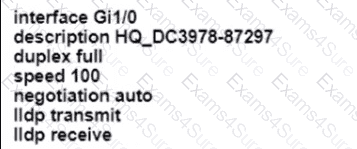
Which action is necessary to complete the configuration if the ISP uses third-party network devices?
Refer to the exhibit.
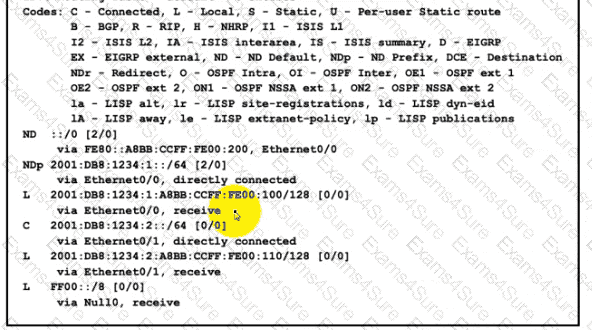
The administrator must configure a floating static default route that points to 2001:db8:1234:2::1 and replaces the current default route only if it fails. Which command must the engineer configure on the CPE?
When a site-to-site VPN is used, which protocol is responsible for the transport of user data?
An office has 8 floors with approximately 30-40 users per floor What command must be configured on the router Switched Virtual Interface to use address space efficiently?
Refer to the exhibit.
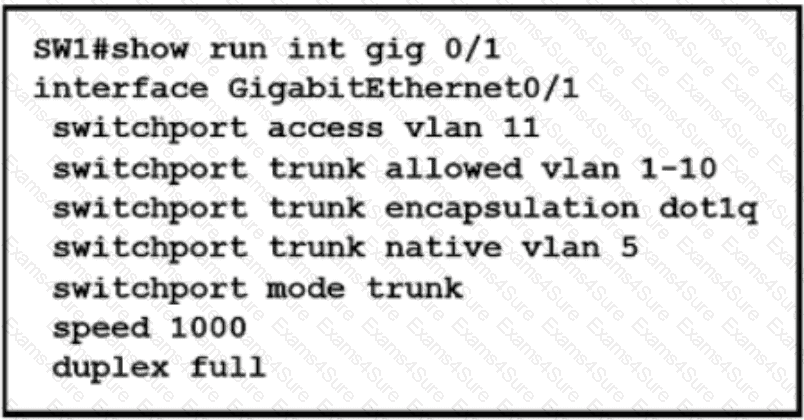
Which action is expected from SW1 when the untagged frame is received on the GigabitEthernet0/1 interface?
Which communication interaction takes place when a southbound API Is used?
Which result occurs when PortFast is enabled on an interface that is connected to another switch?
What are two reasons for an engineer to configure a floating static route? (Choose two)
Refer to the exhibit.
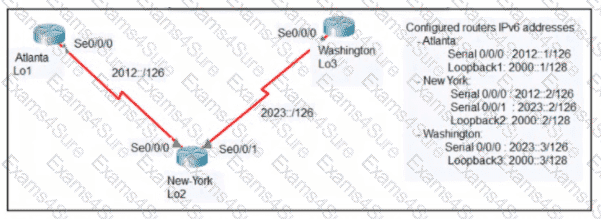
An engineer configured the New York router with static routes that point to the Atlanta and Washington sites. When command must be configured on the Atlanta and Washington routers so that both sites are able to reach the loopback2 interface on the New York router?
What are two differences between optical-fiber cabling and copper cabling? (Choose two)
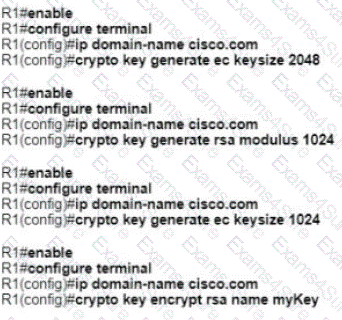
A network administrator must to configure SSH for remote access to router R1 The requirement is to use a public and private key pair to encrypt management traffic to and from the connecting client.
Which configuration, when applied, meets the requirements?