200-301 Practice Questions
Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1
Last Update 4 days ago
Total Questions : 1240
Dive into our fully updated and stable 200-301 practice test platform, featuring all the latest CCNA exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-301. Use this test to pinpoint which areas you need to focus your study on.
Which function generally performed by a traditional network device is replaced by a software-defined controller?
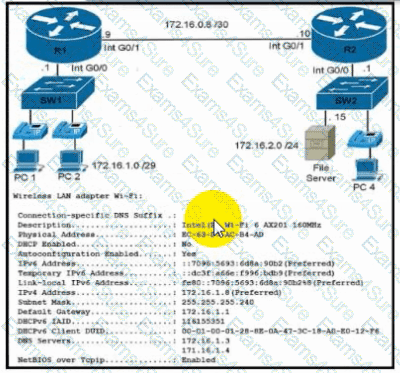
Refer to the exhibit. During initial configuration testing, the Windows workstation PC1 cannot connect with the 172.16.2.0/24 network.
Which set of actions corrects the configuration?
Which IP addressss is used when an administrator must open a web-based management session with a lightweight AP?
Which mechanism allows WPA3 to provide a higher degree of security than its predecessors?
Refer to the exhibit.
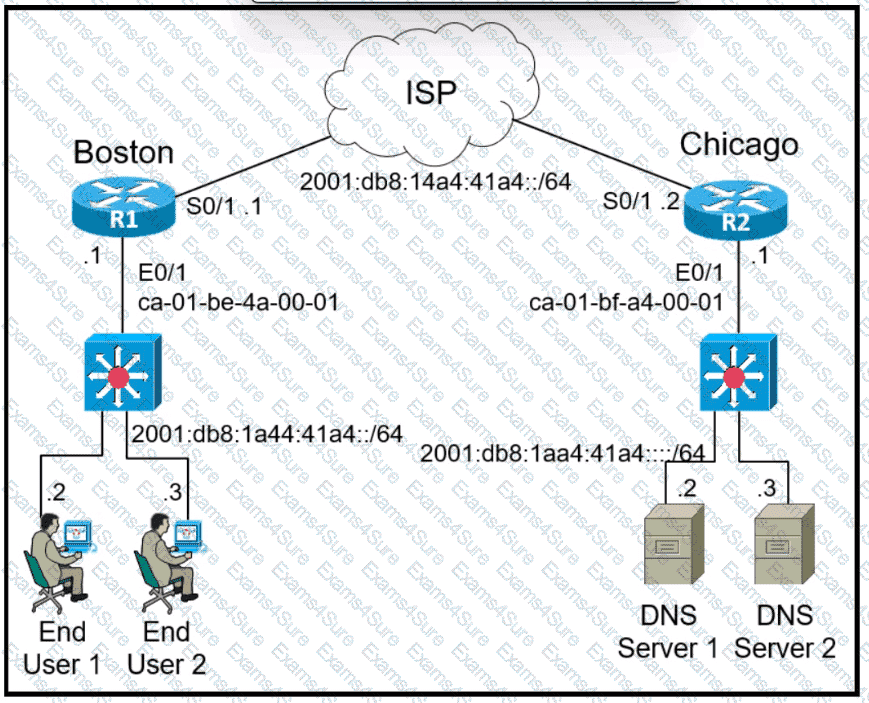
Refer to the exhibit. The IPv6 address for the LAN segment on router R1 must be configured using the EUI-64 format. When configured which ipv6 address is produced by the router?
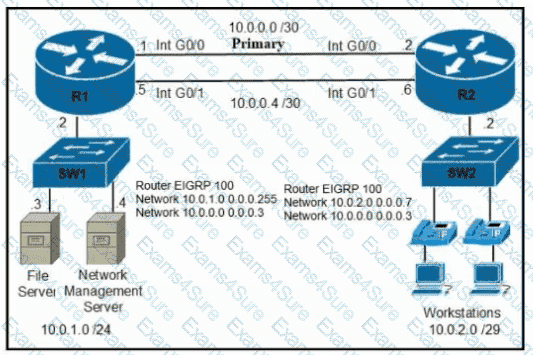
Refer to the exhibit. A secondary route is required on router R1 to pass traffic to the LAN network on R2 if the primary link fails. Which command must be entered to configure the router?
Which group of channels in the 802.11b/g/n/ax 2.4 GHz frequency bands are non-overlapping channels?
A manager asks a network engineer to recommend a cloud service model so that employees do not spend time installing, managing, and updating software that is only used occasionally. Which cloud service model does the engineer recommend?
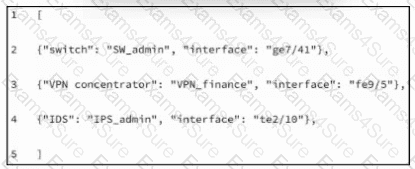
Refer to the exhibit. What is represented in line 2 within this JSDN schema?
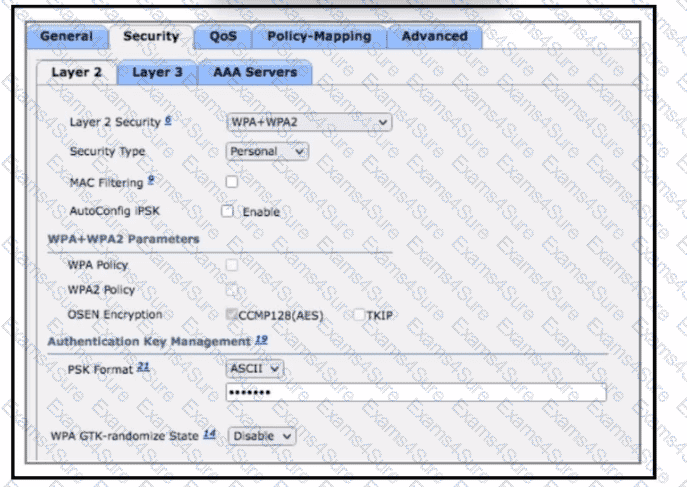
Refer to the exhibit. Company A wants to use a RADIUS server to service all user and device authentication attempts with a more secure and granular authentication approach. Not all client devices support dot1x authentication. Which two configuration changes must be made to accomplish the task? (Choose two.)
Refer to the exhibit.
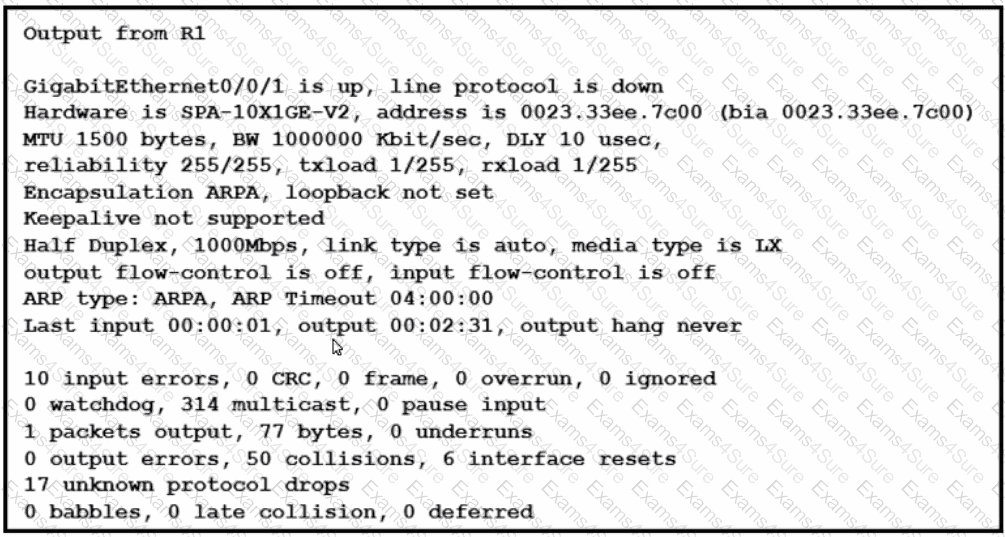
What is the issue with the interface GigabitEthernet0/0/1?
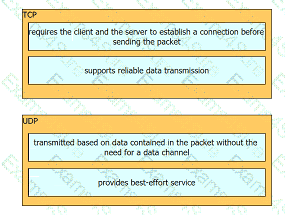
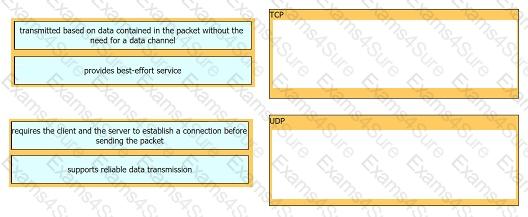
Drag and drop the TCP or UDP details from the left onto their corresponding protocols on the right.
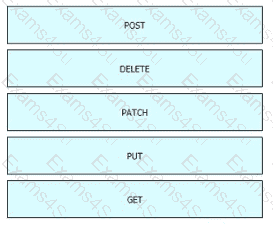
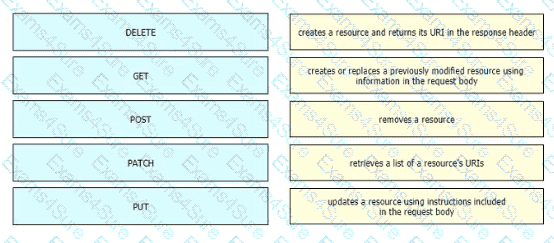
Drag and drop the HTTP methods used with REST-Based APIs from the left onto the descriptions on the right.
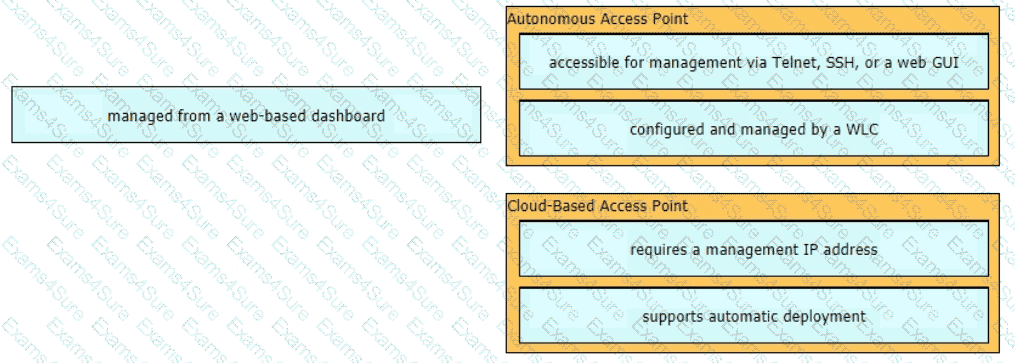
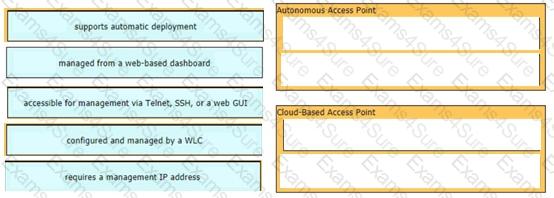
Drag and drop the facts about wireless architectures from the left onto the types of access point on the right. Not all options are used.
Which command do you enter so that a switch configured with Rapid PVST + listens and learns for a specific time period?
Which type of network attack overwhelms the target server by sending multiple packets to a port until the half-open TCP resources of the target are exhausted?
Which Layer 2 switch function encapsulates packets for different VLANs so that the packets traverse the same port and maintain traffic separation between the VLANs?
Refer to the exhibit.
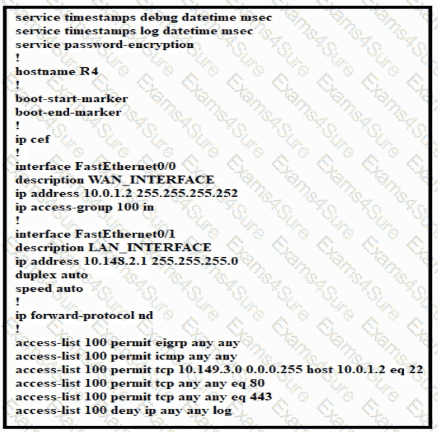
Which configuration enables DHCP addressing for hosts connected to interface FastEthernet0/1 on router R4?