200-301 Practice Questions
Implementing and Administering Cisco Solutions (200-301 CCNA) v1.1
Last Update 4 days ago
Total Questions : 1240
Dive into our fully updated and stable 200-301 practice test platform, featuring all the latest CCNA exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 200-301. Use this test to pinpoint which areas you need to focus your study on.
Refer to the exhibit.
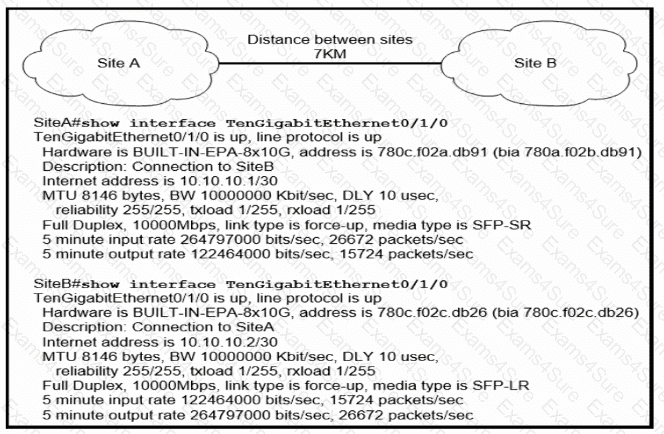
Site A was recently connected to site B over a new single-mode fiber path. Users at site A report Intermittent connectivity Issues with applications hosted at site
B.
What is the reason for the problem?Refer to the exhibit.
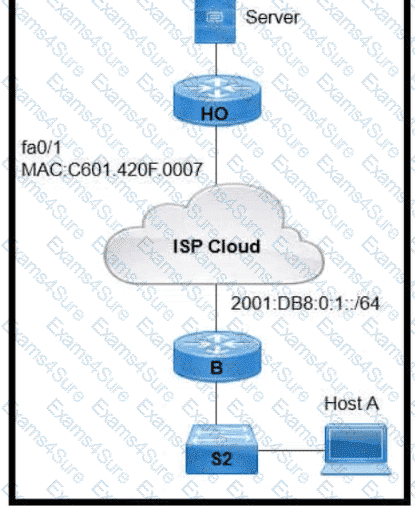
An engineer is configuring the HO router. Which IPv6 address configuration must be applied to the router Fa0/1 interface for the router to assign a unique 64-brt IPv6 address to Itself?
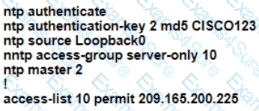
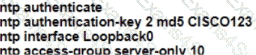
R1 as an NTP server must have:
• NTP authentication enabled
• NTP packets sourced from Interface loopback 0
• NTP stratum 2
• NTP packets only permitted to client IP 209.165.200.225
How should R1 be configured?
A)
B)
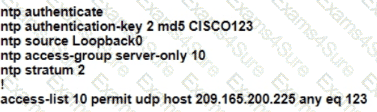
C)
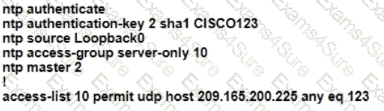
D)
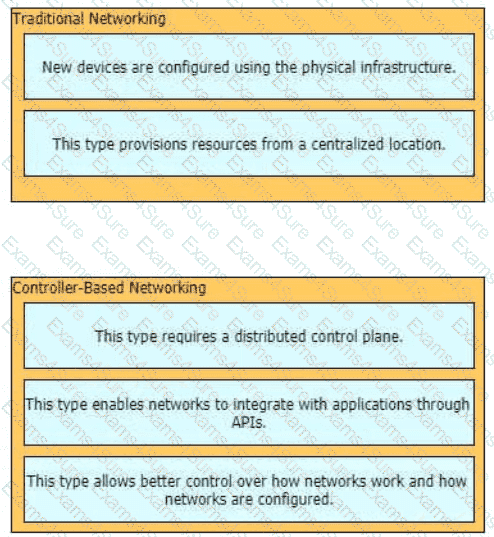
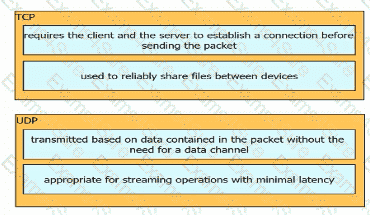
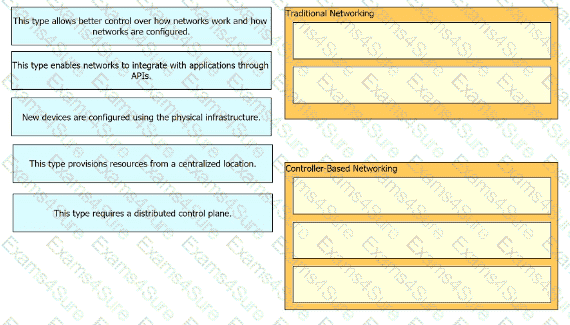
Drag and drop the statements about networking from the left onto the corresponding networking types on the right.
Refer to the exhibit.
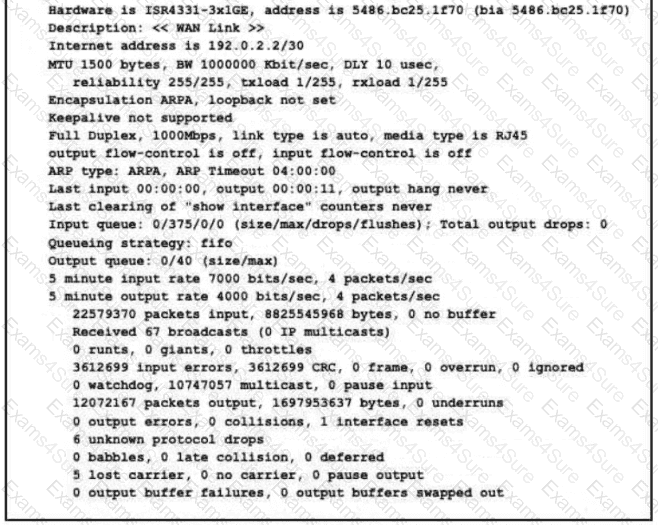
What is a reason for poor performance on the network interface?
Refer to the exhibit.
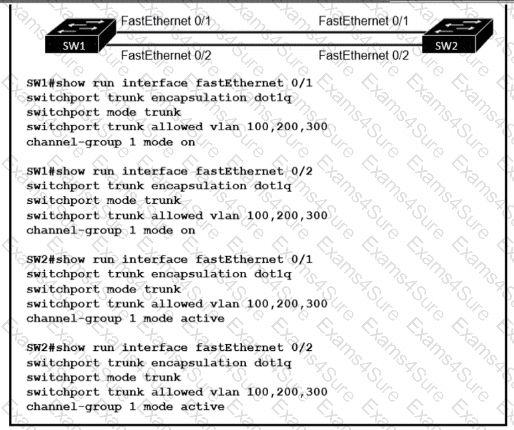
An engineer built a new Layer 2 LACP EtherChannel between SW1 and SW2 and executed these show commands to verify the work. Which additional task allows the two switches to establish an LACP port channel?
What are two reasons that cause late collisions to increment on an Ethernet interface? (Choose two)
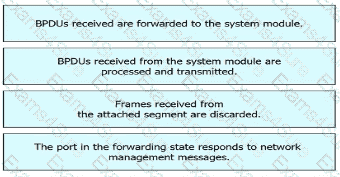
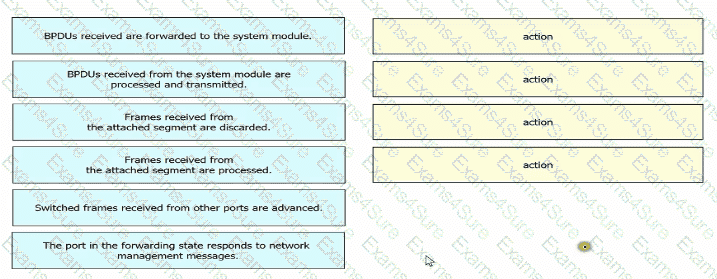
Drag and drop the Rapid PVST+ forwarding state actions from the loft to the right. Not all actions are used.
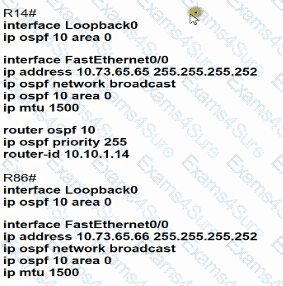
Refer to the exhibit.
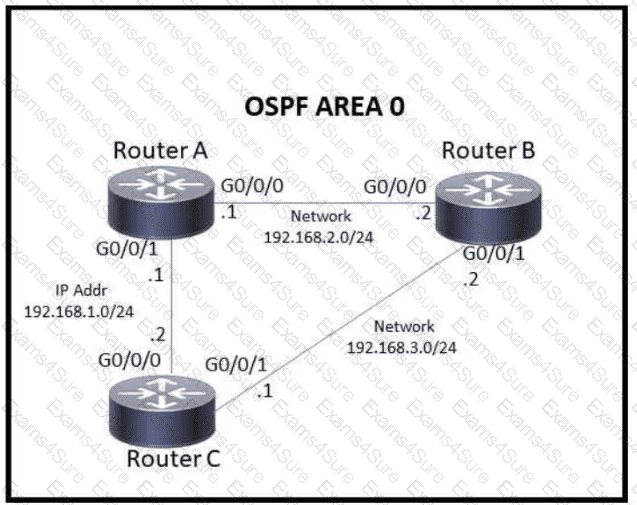
Which action must be taken to ensure that router A is elected as the DR for OSPF area 0?
Refer to the exhibit.
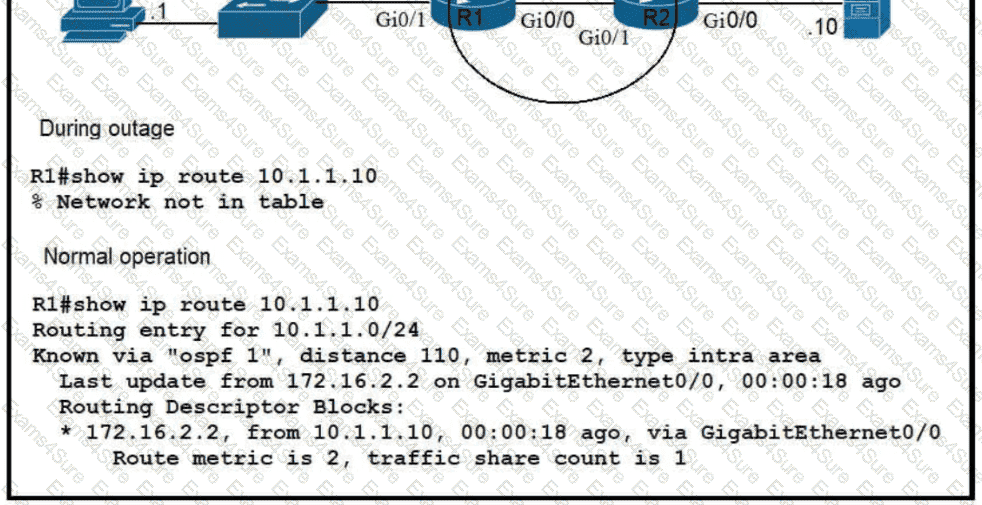
Which route must be configured on R1 so that OSPF routing is used when OSPF is up. but the server is still reachable when OSPF goes down?
Refer to the exhibit.
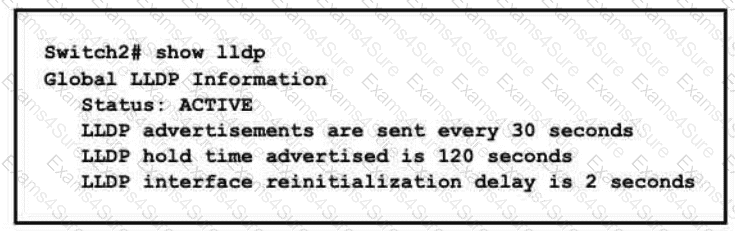
A network engineer must update the configuration on Switch2 so that it sends LLDP packets every minute and the information sent via LLDP is refreshed every 3 minutes Which configuration must the engineer apply?
A)
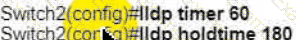
B)
C)
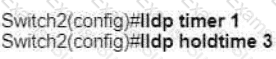
D)
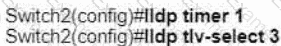
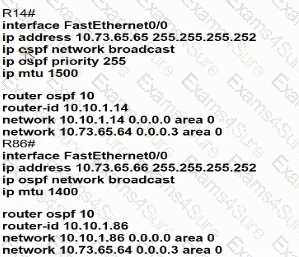
Refer to the exhibit.
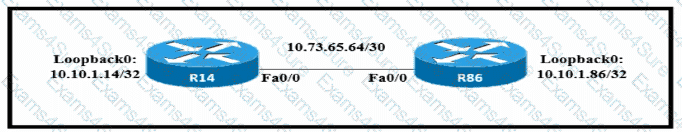
Which configuration allows routers R14 and R86 to form an OSPFv2 adjacency while acting as a central point for exchanging OSPF information between routers?
A)
B)
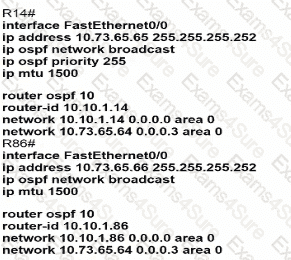
C)
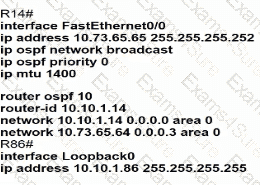
D)
What is a function of Cisco Advanced Malware Protection for a Next-Generation IPS?
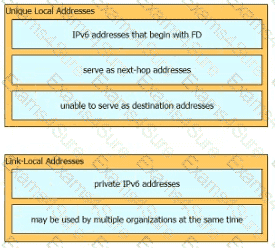
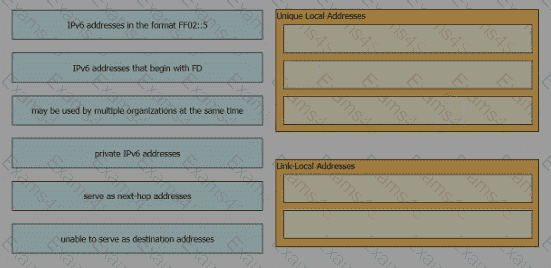
Drag and drop the IPv6 address description from the left onto the IPv6 address types on the right. Not all options are used.
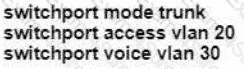
A Cisco engineer must configure a single switch interface to meet these requirements
• accept untagged frames and place them in VLAN 20
• accept tagged frames in VLAN 30 when CDP detects a Cisco IP phone
Which command set must the engineer apply?
A)
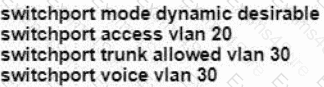
B)
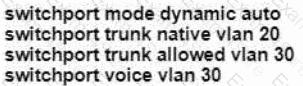
C)

D)
Refer to the exhibit.
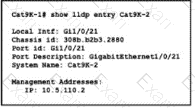
The network administrator must prevent the switch Cat9K-2 IP address from being visible in LLDP without disabling the protocol. Which action must be taken must be taken to complete the task?
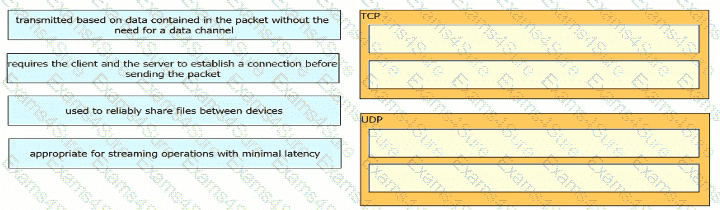
Drag and drop the TCP or UDP details from the left onto their corresponding protocols on the right.