
NSE6_EDR_AD-7.0 Practice Questions
Fortinet NSE 6 - FortiEDR 7.0 Administrator
Last Update 1 hour ago
Total Questions : 33
Dive into our fully updated and stable NSE6_EDR_AD-7.0 practice test platform, featuring all the latest NSE 6 Network Security Specialist exam questions added this week. Our preparation tool is more than just a Fortinet study aid; it's a strategic advantage.
Our free NSE 6 Network Security Specialist practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about NSE6_EDR_AD-7.0. Use this test to pinpoint which areas you need to focus your study on.
Refer to the exhibits.
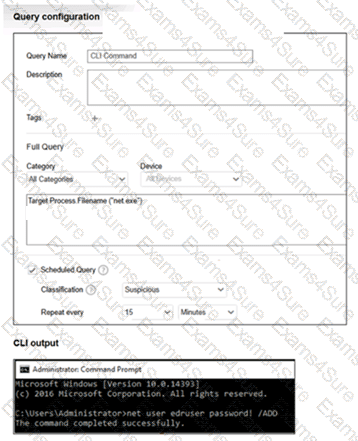
What happens when the net user command runs on an endpoint? (Choose one answer)
A playbook is configured with two actions: terminate process and isolate device. The terminate process action fails because the process is protected by Windows. What is the expected behavior for the second action, isolate device? (Choose one answer)
Which two Python commands are supported when using FortiEDR Connect to directly access a protected device shell? (Choose two answers)
Refer to the exhibits.
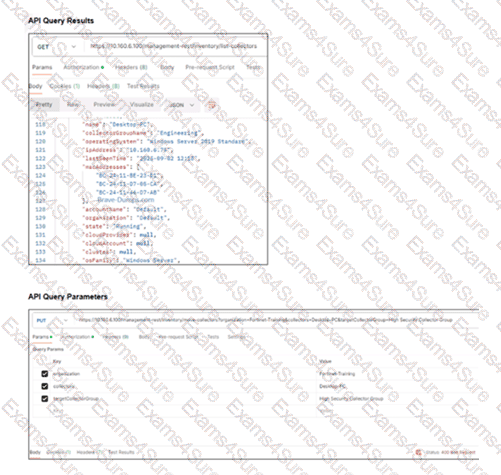
You are attempting to move a collector into the High Security Collector Group for isolation but encounter an error in the API request as shown in the exhibit. To successfully isolate the collector, which API parameter must you correct? (Choose one answer)
You discovered that a newly installed collector does not display on the Inventory tab in the central manager. Which two troubleshooting steps must you perform? (Choose two answers)
Refer to the exhibit:

You configured an execution prevention exclusion with both File Name = app.exe and Path = C:\Tools. What will FortiEDR do? (Choose one answer)
Refer to the exhibit.

Based on the event shown in the exhibit, which two statements about the event are true? (Choose two answers)
Within the FortiEDR architecture, which component needs JumpBox capabilities to enable authenticated and controlled communication with FortiAnalyzer? (Choose one answer)
Refer to the exhibit:
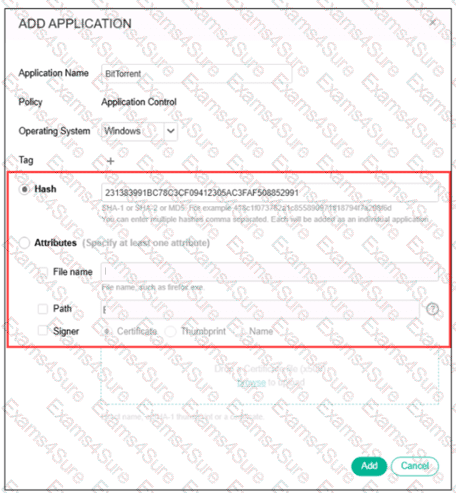
You are asked to block applications based on hash attributes. Which two factors must you consider when applying the hash value? (Choose two answers)



