250-428 Practice Questions
Administration of Symantec Endpoint Protection 14
Last Update 3 days ago
Total Questions : 135
Dive into our fully updated and stable 250-428 practice test platform, featuring all the latest Endpoint Protection 14 exam questions added this week. Our preparation tool is more than just a Symantec study aid; it's a strategic advantage.
Our free Endpoint Protection 14 practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 250-428. Use this test to pinpoint which areas you need to focus your study on.
A Symantec Endpoint Protection (SEP) administrator is remotely deploying SEP clients, but the clients are failing to install on Windows XP.
What are two possible reasons for preventing installation? (Select two.)
An administrator plans to implement a multi-site Symantec Endpoint Protection (SEP) deployment. The administrator needs to determine whether replication is viable without needing to make network firewall changes or change defaults in SEP.
Which port should the administrator verify is open on the path of communication between the two proposed sites?
An administrator is recovering from a Symantec Endpoint Manager (SEPM) site failure.
Which file should the administrator use during an install of SEPM to recover the lost environment according to Symantec Disaster Recovery Best Practice documentation?
An administrator selects the Backup files before attempting to repair the Remediations option in the Auto-Protect policies.
Which two actions occur when a virus is detected? (Select two.)
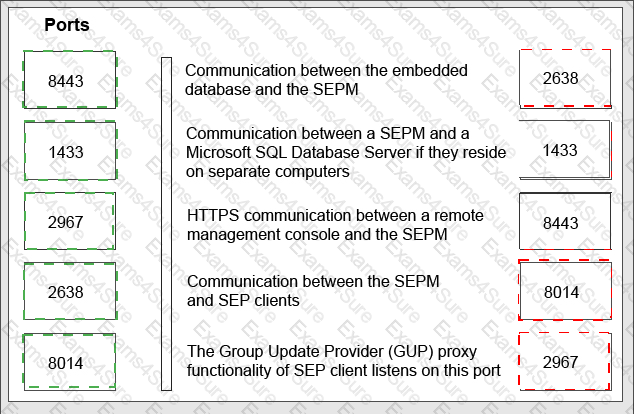
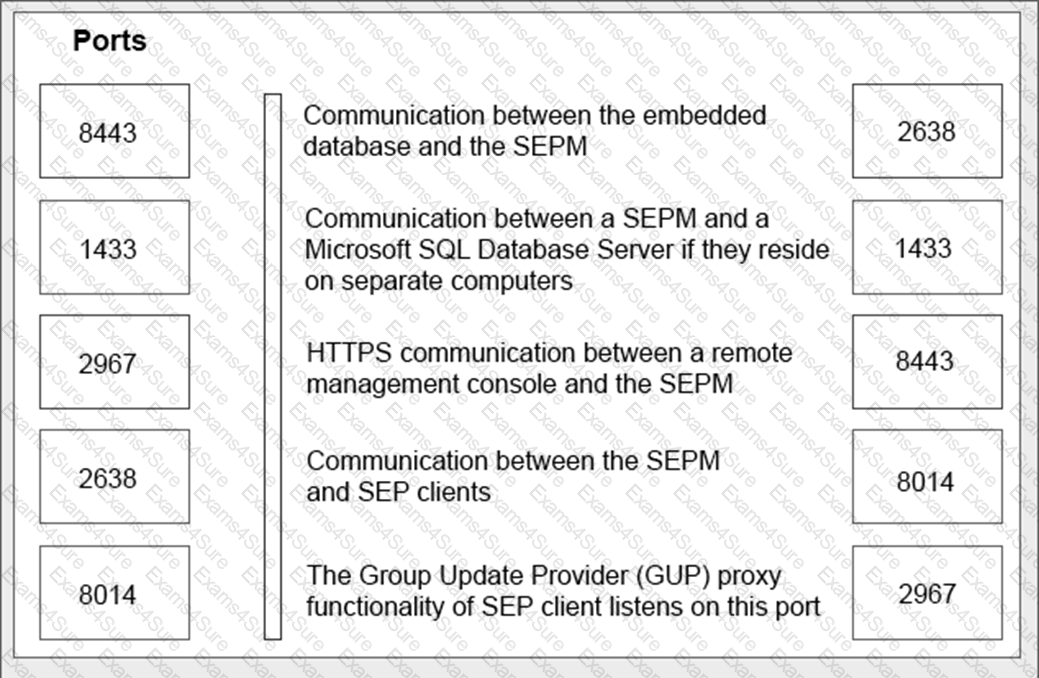
Match the following list of ports used by Symantec Endpoint Protection (SEP) to the defining characteristics by clicking and dragging the port on the left to the corresponding description on the right.
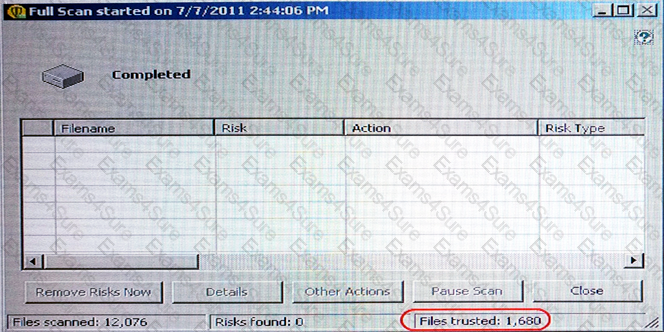
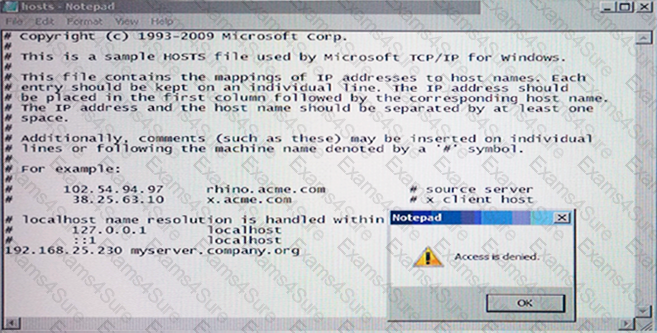
Why is Notepad unable to save the changes to the file in the image below?
Which protection engine should an administrator enable in order to drop malicious vulnerability scans against a client system?
Which protection technology can detect botnet command and control traffic generated on the Symantec Endpoint Protection client machine?
A user is unknowingly about to connect to a malicious website and download a known threat within a .rar file. All Symantec Endpoint Protection technologies are installed on the client's system.
In which feature set order must the threat pass through to successfully infect the system?