250-587 Practice Questions
Symantec Data Loss Prevention 16.x Administration Technical Specialist
Last Update 3 days ago
Total Questions : 100
Dive into our fully updated and stable 250-587 practice test platform, featuring all the latest Data Loss Prevention exam questions added this week. Our preparation tool is more than just a Symantec study aid; it's a strategic advantage.
Our free Data Loss Prevention practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 250-587. Use this test to pinpoint which areas you need to focus your study on.
A divisional executive requests a report of all incidents generated by a particular region, summarized by department.
What does the DLP administrator need to configure to generate this report?
A company needs to implement Data Owner Exception so that incidents when employees send or receive their own personal information.
What detection method should the company use?
A DLP administrator has enabled and successfully tested custom attribute lookups for incident data based on the Active Directory LDAP plugin. The Chief Information Security Officer (CISO) has attempted to generate a User Risk Summary report, but the report is empty. The DLP administrator confirms the Cisco’s role has the “User Reporting” privilege enabled, but User Risk reporting is still not working.
What is the probable reason that the User Risk Summary report is blank?
A DLP administrator is preparing to install Symantec DLP and has been asked to use an Oracle database provided by the Database Administration team.
Which SQL *Plus command should the administrator utilize to determine if the database is using a supported version of Oracle?
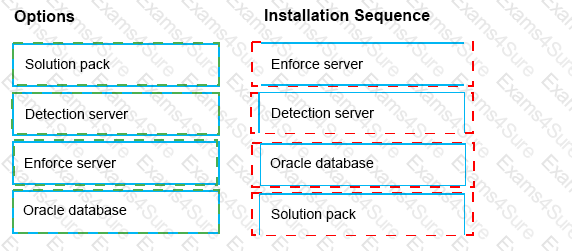
What is the correct installation sequence for the components shown here, according to the Symantec Installation Guide?
Place the options in the correct installation sequence.
What are two reasons an administrator should utilize a manual configuration to determine the endpoint location? (Choose two.)
How should a DLP administrator exclude a custom endpoint application named “custom_app.exe” from being monitoring by Application File Access Control?
Where do you configure the list of Endpoint Servers (or load balancers) to which a DLP Agent can report?
A software company wants to protect its source code, including new source code created between scheduled indexing runs.
Which detection method should the company use to meet this requirement?