300-715 Practice Questions
Implementing and Configuring Cisco Identity Services Engine (SISE) v4.0 (300-715 SISE)
Last Update 8 hours ago
Total Questions : 299
Dive into our fully updated and stable 300-715 practice test platform, featuring all the latest CCNP Security exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNP Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 300-715. Use this test to pinpoint which areas you need to focus your study on.
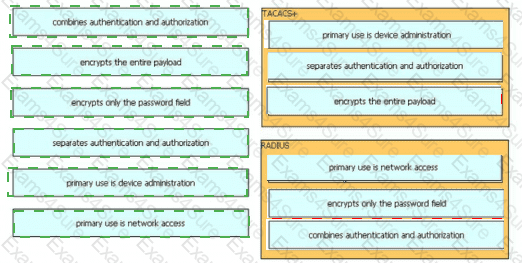
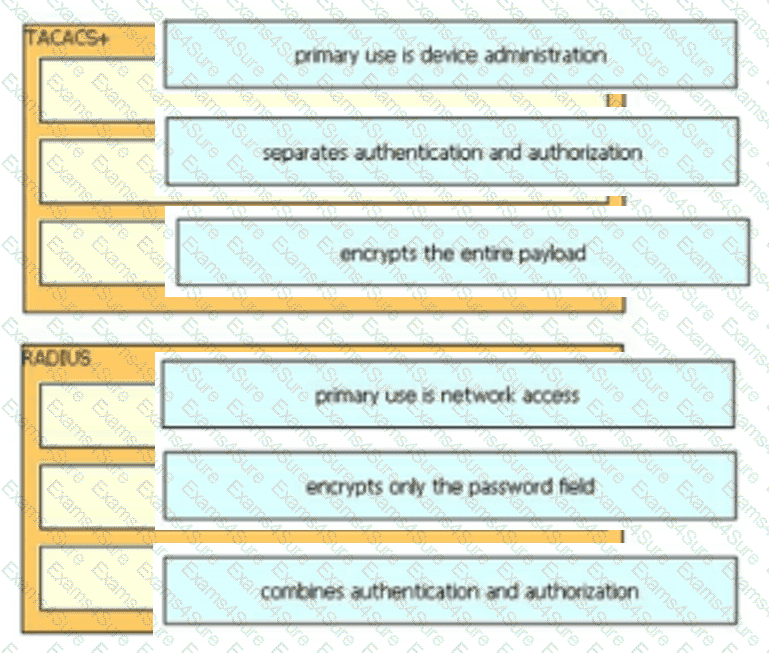
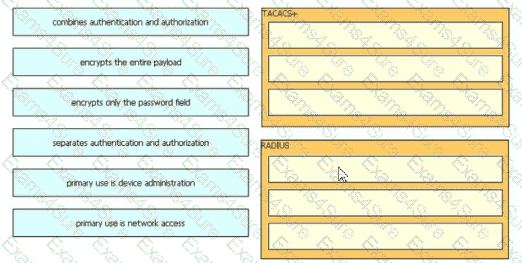
Drag and drop the description from the left onto the protocol on the right that is used to carry out system authentication, authentication, and accounting.
TION NO: 33
Which portal is used to customize the settings for a user to log in and download the compliance module?
An engineer is configuring Cisco ISE policies to support MAB for devices that do not have 802.1X capabilities. The engineer is configuring new endpoint identity groups as conditions to be used in the AuthZ policies, but noticed that the endpoints are not hitting the correct policies. What must be done in order to get the devices into the right policies?
Which two fields are available when creating an endpoint on the context visibility page of Cisco IS? (Choose two)
A network engineer needs to ensure that the access credentials are not exposed during the 802.1x authentication among components. Which two protocols should complete this task?
Refer to the exhibit.
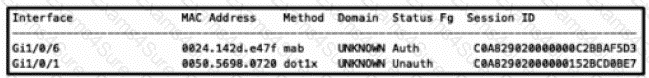
An engineer is configuring a client but cannot authenticate to Cisco ISE During troubleshooting, the show authentication sessions command was issued to display the authentication status of each port Which command gives additional information to help identify the problem with the authentication?
What is the maximum number of PSN nodes supported in a medium-sized deployment?
Which two default guest portals are available with Cisco ISE? (Choose two.)
An engineer is configuring web authentication and needs to allow specific protocols to permit DNS traffic. Which type of access list should be used for this configuration?
When configuring an authorization policy, an administrator cannot see specific Active Directory groups present in their domain to be used as a policy condition. However, other groups that are in the same domain are seen What is causing this issue?