
300-720 Practice Questions
Securing Email with Cisco Email Security Appliance (300-720 SESA)
Last Update 7 hours ago
Total Questions : 190
Dive into our fully updated and stable 300-720 practice test platform, featuring all the latest CCNP Security exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNP Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 300-720. Use this test to pinpoint which areas you need to focus your study on.
An engineer is configuring a Cisco Secure Email Gateway and needs to reject email messages to a recipient with email address user0516585210@acme.com . Which list contains the allowed recipient addresses?
When the spam quarantine is configured on the Cisco Secure Email Gateway, which type of query is used to validate non administrative user access to the end-user quarantine via LDAP?
What is the function of authenticating SMTP sessions using client certificates?
An organization wants to designate help desk personnel to assist with tickets that request the release of messages from the spam quarantine because company policy does not permit direct end-user access to the quarantine. Which two roles must be used to allow help desk personnel to release messages while restricting their access to make configuration changes in the Cisco Secure Email Gateway? (Choose two.)
An administrator manipulated the subnet mask but was still unable to access the user interface. How must the administrator access the Cisco Secure Email Gateway appliance to perform the initial configuration?
What is the default method of remotely accessing a newly deployed Cisco Secure Email Virtual Gateway when a DHCP server is not available?
An engineer must implement policies in Cisco Secure Email Gateway to prevent suspicious spam messages from being delivered to executives group. Messages that arrive from public email addresses from the yahoo.com or gmail.com domains must be redirected to the IT department. Which two configuration actions must be taken to meet the requirement? (Choose two.)
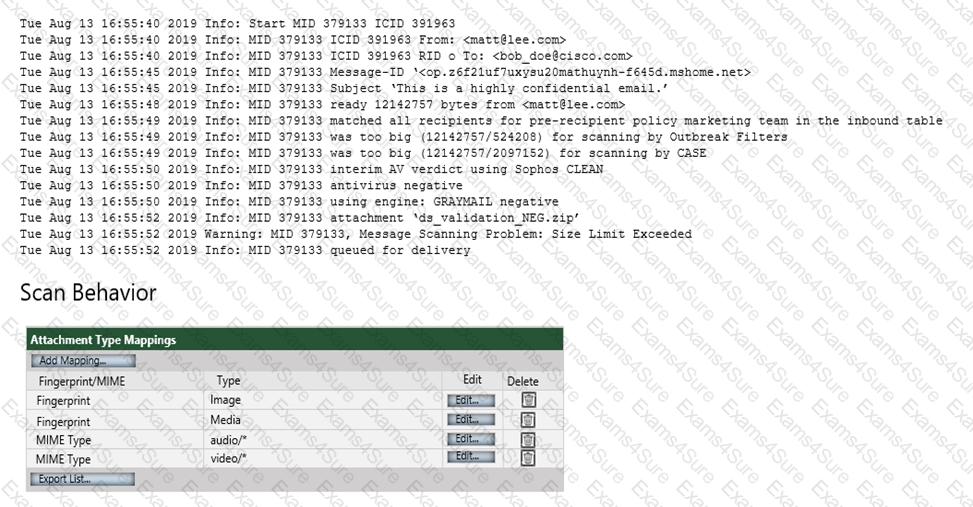
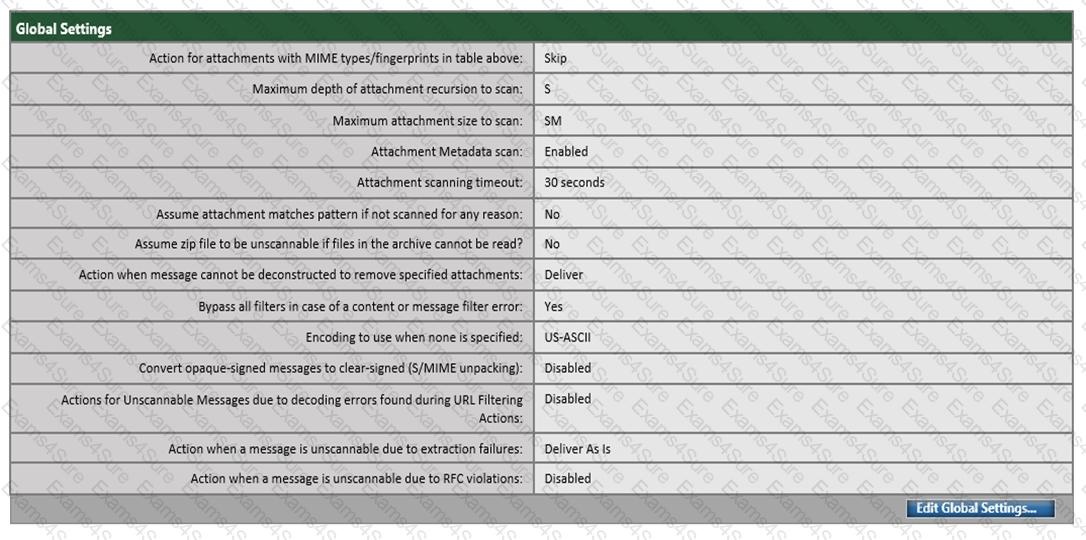
Refer to the exhibit. Which configuration on the scan behavior must be updated to allow the attachment to be scanned on the Cisco ESA?
Spammers routinely try to send emails with the recipient field filled with a list of all possible combinations of letters and numbers. These combinations, appended with a company domain name are malicious attempts at learning all possible valid email addresses. Which action must be taken on a Cisco Secure Email Gateway to prevent this from occurring?



