
300-745 Practice Questions
Designing Cisco Security Infrastructure (300-745 SDSI) v1.0
Last Update 3 days ago
Total Questions : 57
Dive into our fully updated and stable 300-745 practice test platform, featuring all the latest CCNP Security exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNP Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 300-745. Use this test to pinpoint which areas you need to focus your study on.
An employee of a pharmaceutical company accidentally checked in code that contains AWS secret keys to a public GitHub repository, which exposes production resources to attackers. Which mitigation strategy must a security engineer recommend to prevent future reoccurrence?
Employees in a healthcare organization could not access their devices when they returned to work after the weekend. The security team discovered that a threat actor had encrypted the devices. Which security solution would mitigate the risk in future?
After a recent security breach, a financial company is reassessing their overall security posture and strategy to better protect sensitive data and resources. The company already deployed on-premises next-generation firewalls at the network edge for each branch location. Security measures must be enhanced at the endpoint level. The goal is to implement a solution that provides additional traffic filtering directly on endpoint devices, thereby offering another layer of defense against potential threats. Which technology must be implemented to meet the requirement?
Refer to the exhibit.
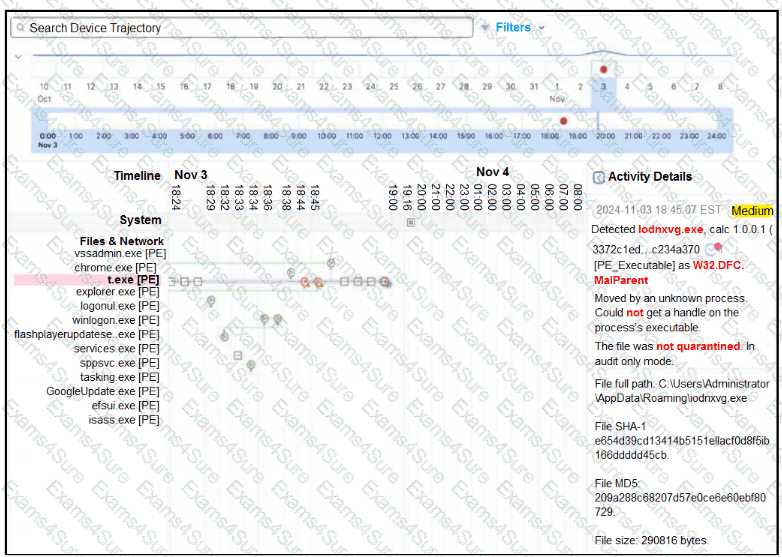
A retail company recently deployed a file inspection feature using secure endpoint. The file inspection must detect and prevent the execution of malicious files on machines. During testing, logs showed that certain malicious files are still being executed despite the presence of the security measure. To understand why the threats are not being blocked, it is essential to investigate the configuration of secure endpoint policies. Which configuration is allowing the files to execute?
A furniture company recently discovered that the endpoint detection and response configuration flagged several malicious files on company-managed laptops. The company must enhance security to prevent known malicious files from being delivered to the network and endpoints. The new solution must enhance the company’s ability to inspect and filter incoming traffic effectively. Which security product must be used to accomplish this goal?
The network security team of a private university is conducting a comprehensive audit to evaluate the security posture across the network infrastructure. During the review, the security team found that a trusted vendor disclosed serious vulnerabilities identified in a product that plays a crucial role in the university’s CI/CD pipeline. The security team must act promptly to mitigate the potential risks posed by these vulnerabilities. Which action must the security team take first in response to the disclosure?
A financial company uses a remote access solution that directs all traffic over a secure tunnel. The company recently received some large ISP bills from the headquarter location. According to traffic analysis during the investigation, most of the network traffic was due to employees spending a lot of time on video conferences provided by a SaaS collaboration company. What must the company modify to reduce the cost without negatively impacting security or employee experience?
A restaurant distribution center recently suffered a password spray attack targeting the Cisco Secure Firepower Threat Defense VPN headend. The attack attempts to gain unauthorized access by trying common passwords across many accounts. The attack poses a significant security threat to the organization’s remote access infrastructure. To enhance the security of the VPN setup and minimize the risk of similar attacks in the future, the IT security team must implement effective mitigation measures. Which technique effectively reduces the risk of this type of attack?
Network administrators at a medical facility cannot log in to network devices because of excessive resource consumption and high CPU utilization. The situation has led to delays in routine maintenance and troubleshooting, which affects overall network performance. An engineer must optimize the handling of traffic to reduce the impact and maintain consistent access and operational efficiency. Which approach must be implemented to meet the requirement?



