
312-50 Practice Questions
Certified Ethical Hacker Exam
Last Update 1 day ago
Total Questions : 614
Dive into our fully updated and stable 312-50 practice test platform, featuring all the latest Certified Ethical Hacker exam questions added this week. Our preparation tool is more than just a ECCouncil study aid; it's a strategic advantage.
Our free Certified Ethical Hacker practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 312-50. Use this test to pinpoint which areas you need to focus your study on.
The following is part of a log file taken from the machine on the network with the IP address of 192.168.1.106:
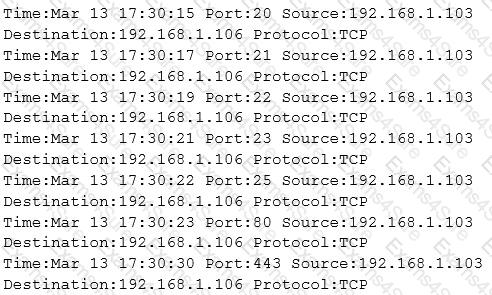
What type of activity has been logged?
A penetration tester is hired to do a risk assessment of a company's DMZ. The rules of engagement states that the penetration test be done from an external IP address with no prior knowledge of the internal IT systems. What kind of test is being performed?
A consultant has been hired by the V.P. of a large financial organization to assess the company's security posture. During the security testing, the consultant comes across child pornography on the V.P.'s computer. What is the consultant's obligation to the financial organization?
Which initial procedure should an ethical hacker perform after being brought into an organization?
A computer technician is using a new version of a word processing software package when it is discovered that a special sequence of characters causes the entire computer to crash. The technician researches the bug and discovers that no one else experienced the problem. What is the appropriate next step?
A certified ethical hacker (CEH) completed a penetration test of the main headquarters of a company almost two months ago, but has yet to get paid. The customer is suffering from financial problems, and the CEH is worried that the company will go out of business and end up not paying. What actions should the CEH take?
A certified ethical hacker (CEH) is approached by a friend who believes her husband is cheating. She offers to pay to break into her husband's email account in order to find proof so she can take him to court. What is the ethical response?
An ethical hacker for a large security research firm performs penetration tests, vulnerability tests, and risk assessments. A friend recently started a company and asks the hacker to perform a penetration test and vulnerability assessment of the new company as a favor. What should the hacker's next step be before starting work on this job?
A hacker is attempting to see which IP addresses are currently active on a network. Which NMAP switch would the hacker use?
How does an operating system protect the passwords used for account logins?



