
350-101 Practice Questions
Implementing and Operating Cisco Wireless Core Technologies (350-101 WLCOR)v1.0
Last Update 2 days ago
Total Questions : 102
Dive into our fully updated and stable 350-101 practice test platform, featuring all the latest CCIE Wireless exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCIE Wireless practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 350-101. Use this test to pinpoint which areas you need to focus your study on.
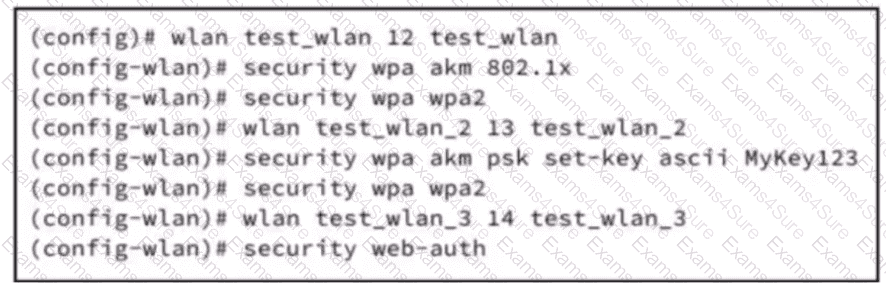
A wireless controller is deployed at a branch location to facilitate secure client connectivity. A network engineer configures one WLAN using WPA2 Personal authentication and activates the preshared key method to align with company security policies. Which action must be taken to enable the client to connect to the WLAN?
Refer to the exhibit.
import requests
import json
API_ENDPOINT = "https://your-api-server.com/api/v1/devices/wireless"
AUTH_TOKEN = "YOUR_SECRET_API_TOKEN"
headers = {
"Accept": "application/json",
"Authorization": f"Bearer {AUTH_TOKEN}"
}
print("Fetching wireless inventory from the API...")
try:
response = requests.get(API_ENDPOINT, headers=headers, timeout=10)
response.raise_for_status()
wireless_inventory_list = response.json()
print("Successfully retrieved and parsed device data.\n")
print("--- Wireless Device Summary ---")
if isinstance(wireless_inventory_list, list) and wireless_inventory_list:
for device in wireless_inventory_list:
mac = device.get("macAddress", "N/A")
ip = device.get("ipAddress", "N/A")
print(f"Device Found - > MAC: {mac}, IP: {ip}")
else:
print("No wireless devices were found in the inventory.")
except requests.exceptions.RequestException as e:
print(f"Error during API request: {e}")
except json.JSONDecodeError:
print("Error: Failed to parse the response from the API. It is not valid JSON.")
A Cisco engineer is analyzing how a dictionary interacts with key-value pairs in a Python script that processes device records collected from a wireless controller. The engineer reviews the construction of the script to interpret the sequence used for data extraction. Which element performs the interaction within the script?
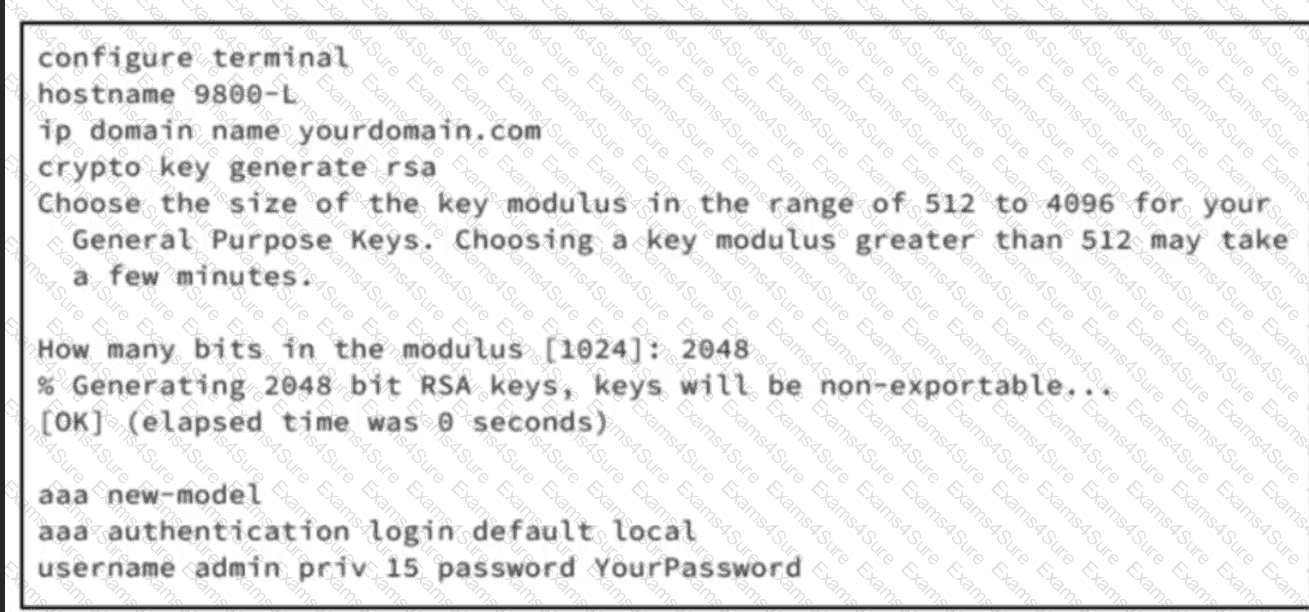
Refer to the exhibit. An engineer is preparing a Cisco 9800-L WLC for deployment in a sensitive area. Only encrypted remote management via SSH is allowed, and all other VTY access methods must be disabled. The 9800-L WLC will be part of a larger deployment, and an external audit will check for any unencrypted management protocols. According to the requirements, only SSH is allowed for remote CLI sessions. Which set of commands must be executed to complete the Cisco IOS XE CLI configuration on the WLC?
Exhibit:
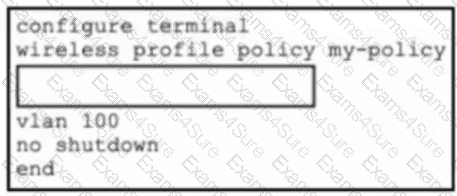
Refer to the exhibit. An enterprise is deploying Cisco Catalyst 9800 WLCs and is using Catalyst Center as the management platform to oversee wireless access policies. To meet the organization's compliance requirements, all wireless endpoints must be evaluated with security posture validation before gaining access. Which set of CLI commands must be added to the box in the code to complete the configuration?
Which result is produced using a power ratio of 10:1 in standard decibel calculations?
Which process allows continuous IP address retention in a wireless network during roaming?
Refer to the exhibit.
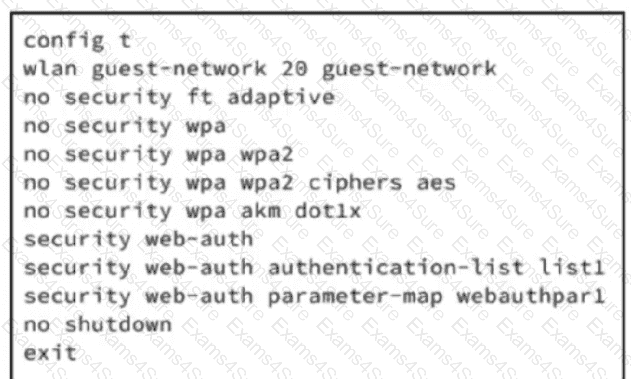
An engineer must configure wireless guest networking for a deployment at site A, which requires support for guest VLAN assignment and assignment for wlan guest-network 20. The controller will provide network segregation and restrict access to internal resources. Based on the configuration commands, which action meets the requirements?
A network engineer is integrating Cisco ISE with a wireless controller for 802.1X authentication. The controller is registered with Cisco ISE as a network device. To secure communication, the engineer must configure a shared secret for RADIUS authentication. Which CLI command on the WLC accomplishes this task?
How does U-NII-1 operate with regards to the common frequency bands supported in enterprise wireless networks?



