.png)
CRISC Practice Questions
Certified in Risk and Information Systems Control
Last Update 3 days ago
Total Questions : 1938
Dive into our fully updated and stable CRISC practice test platform, featuring all the latest Isaca Certification exam questions added this week. Our preparation tool is more than just a Isaca study aid; it's a strategic advantage.
Our free Isaca Certification practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CRISC. Use this test to pinpoint which areas you need to focus your study on.
Which of the following is MOST helpful in providing an overview of an organization's risk management program?
Which of the following would be the BEST way to help ensure the effectiveness of a data loss prevention (DLP) control that has been implemented to prevent the loss of credit card data?
Which of the following is the PRIMARY purpose of periodically reviewing an organization's risk profile?
When reviewing the business continuity plan (BCP) of an online sales order system, a risk practitioner notices that the recovery time objective (RTO) has a shorter lime than what is defined in the disaster recovery plan (DRP). Which of the following is the BEST way for the risk practitioner to address this concern?
A risk practitioner has been asked to assess the risk associated with a new critical application used by a financial process team that the risk practitioner was a member of two years ago. Which of the following is the GREATEST concern with this request?
Which of the following should be the FIRST consideration when establishing a new risk governance program?
Which of the following tools is MOST effective in identifying trends in the IT risk profile?
Due to a change in business processes, an identified risk scenario no longer requires mitigation. Which of the following is the MOST important reason the risk should remain in the risk register?
Several network user accounts were recently created without the required management approvals. Which of the following would be the risk practitioner's BEST recommendation to address this situation?
Which of the following is the GREATEST risk associated with the misclassification of data?
Which of the following is MOST important to include in a risk assessment of an emerging technology?
An organization is conducting a review of emerging risk. Which of the following is the BEST input for this exercise?
Which of the following would cause the GREATEST concern for a risk practitioner reviewing the IT risk scenarios recorded in an organization’s IT risk register?
Which of the following is the BEST way to prevent the loss of highly sensitive data when disposing of storage media?
Legal and regulatory risk associated with business conducted over the Internet is driven by:
An organization is measuring the effectiveness of its change management program to reduce the number of unplanned production changes. Which of the following would be the BEST metric to determine if the program is performing as expected?
A risk manager has determined there is excessive risk with a particular technology. Who is the BEST person to own the unmitigated risk of the technology?
What should a risk practitioner do FIRST when vulnerability assessment results identify a weakness in an application?
Which of the following is the PRIMARY objective for automating controls?
Which of the following is the BEST indicator of the effectiveness of a control?
The BEST way to validate that a risk treatment plan has been implemented effectively is by reviewing:
Which of the following will BEST help to improve an organization's risk culture?
Which of the following is the GREATEST benefit of using IT risk scenarios?
Which of the following is the MOST effective way lo ensure professional ethics are maintained as a core organizational value and adhered to by employees?
A business unit is implementing a data analytics platform to enhance its customer relationship management (CRM) system primarily to process data that has been provided by its customers. Which of the following presents the GREATEST risk to the organization's reputation?
An organization has been notified that a disgruntled, terminated IT administrator has tried to break into the corporate network. Which of the following discoveries should be of GREATEST concern to the organization?
Which of the following is MOST helpful in identifying loss magnitude during risk analysis of a new system?
The PRIMARY reason for establishing various Threshold levels for a set of key risk indicators (KRIs) is to:
During a data loss incident, which role in the RACI chart would be aligned to the risk practitioner?
Improvements in the design and implementation of a control will MOST likely result in an update to:
Which of the following is a responsibility of the second line in the three lines model?
In an organization with a mature risk management program, which of the following would provide the BEST evidence that the IT risk profile is up to date?
What is a risk practitioner's BEST approach to monitor and measure how quickly an exposure to a specific risk can affect the organization?
Which of the following is the BEST way to determine the potential organizational impact of emerging privacy regulations?
Which of the following is MOST helpful in defining an early-warning threshold associated with insufficient network bandwidth’’?
An organization is concerned that a change in its market situation may impact the current level of acceptable risk for senior management. As a result, which of the following is MOST important to reevaluate?
In which of the following scenarios would a risk practitioner be required to provide the MOST justification for a risk assessment?
The following is the snapshot of a recently approved IT risk register maintained by an organization's information security department.
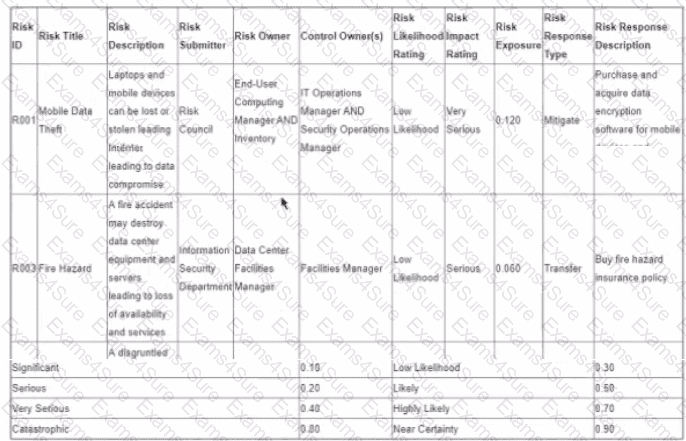
After implementing countermeasures listed in ‘’Risk Response Descriptions’’ for each of the Risk IDs, which of the following component of the register MUST change?
Which of the following controls would BEST reduce the likelihood of a successful network attack through social engineering?
An organization is considering outsourcing user administration controls tor a critical system. The potential vendor has offered to perform quarterly sett-audits of its controls instead of having annual independent audits. Which of the following should be of GREATEST concern to me risk practitioner?
An organization's financial analysis department uses an in-house forecasting application for business projections. Who is responsible for defining access roles to protect the sensitive data within this application?
Which of the following is the MOST relevant information to include in a risk management strategy?
Which of the following is MOST likely to result in a major change to the overall risk profile of the organization?



