
H12-722 Practice Questions
Huawei Certified ICT Professional - Constructing Service Security Network (HCIP-Security-CSSN V3.0)
Last Update 4 days ago
Total Questions : 177
Dive into our fully updated and stable H12-722 practice test platform, featuring all the latest HCIP-Security exam questions added this week. Our preparation tool is more than just a Huawei study aid; it's a strategic advantage.
Our free HCIP-Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about H12-722. Use this test to pinpoint which areas you need to focus your study on.
In the penetration stage of an APT attack, which of the following attack behaviors will the attacker generally have?
The results of the RBL black and white list query on the firewall are as follows:
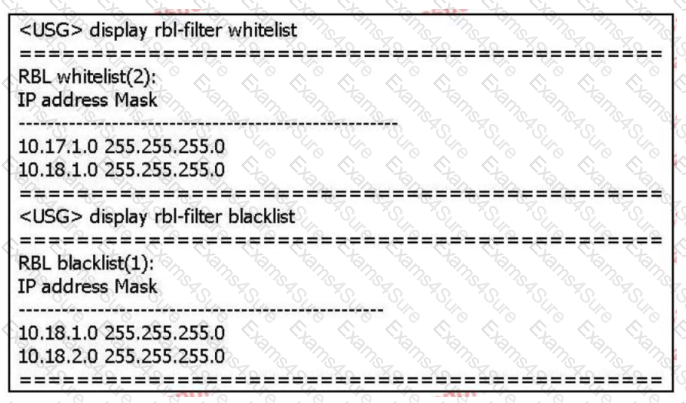
Based on the above information only, which of the following statements is correct? (multiple choice)
The processing flow of IPS has the following steps;
1. Reorganize application data
2. Match the signature
3. Message processing
4. Protocol identification
Which of the following is the correct order of the processing flow?
Which of the following attacks are attacks against web servers? (multiple choices)
Huawei's USG000 product can identify the true type of common files and over-check the content. Even if the file is hidden in a compressed file, or change the extension
The name of the exhibition can't escape the fiery eyes of the firewall.
In the following options, which of the two attacks use similar attack methods, they will generate a large number of useless response packets, occupying network bandwidth,
Consume equipment resources?
Intrusion detection is a network security technology used to detect any damage or attempt to damage the confidentiality, integrity or availability of the system. Which of the following
What is the content of the intrusion detection knowledge base?
In the big data intelligent security analysis platform, it is necessary to collect data from data sources, and then complete a series of actions such as data processing, detection and analysis, etc.
do. Which of the following options does not belong to the action that needs to be completed in the data processing part?
155955cc-666171a2-20fac832-0c042c0422



