
H12-722_V3.0 Practice Questions
HCIP-Security-CSSN V3.0
Last Update 4 days ago
Total Questions : 196
Dive into our fully updated and stable H12-722_V3.0 practice test platform, featuring all the latest HCIP-Security exam questions added this week. Our preparation tool is more than just a Huawei study aid; it's a strategic advantage.
Our free HCIP-Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about H12-722_V3.0. Use this test to pinpoint which areas you need to focus your study on.
Which of the following technology, administrators can according to business requirements, to scale to achieve load sharing of business flow?
If the processing strategy for SMTP virus files is set to alert, which of the following options is correct?
Which of the following protocols can be used to construct attack messages for special control message attacks? (multiple choice)
A ICMP protocol
B.
UDP protocolC.
CIP protocolD.
FTP protocolMisuse detection is through the detection of similar intrusions in user behavior, or those that use system flaws to indirectly violate system security rules
To detect intrusions in the system. Which of the following is not a feature of misuse detection 2
When using the misuse check technology, if the normal user behavior is successfully matched with the intrusion feature knowledge base, it will be falsely reported.
The results of the RBL black and white list query on the firewall are as follows:
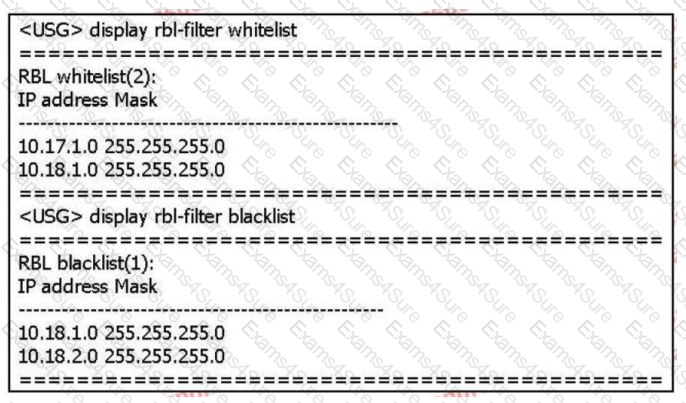
Based on the above information only, which of the following statements is correct? (multiple choice)
The IPS function of Huawei USG6000 supports two response methods: blocking and alarming.
Which of the following options will not pose a security threat to the network?



