
ISA-IEC-62443 Practice Questions
ISA/IEC 62443 Cybersecurity Fundamentals Specialist
Last Update 3 days ago
Total Questions : 227
Dive into our fully updated and stable ISA-IEC-62443 practice test platform, featuring all the latest Cybersecurity exam questions added this week. Our preparation tool is more than just a ISA study aid; it's a strategic advantage.
Our free Cybersecurity practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about ISA-IEC-62443. Use this test to pinpoint which areas you need to focus your study on.
An industrial facility wants to ensure that only authorized systems reach its PLCs while minimizing disruption to time-sensitive control processes. Which type of firewall would BEST suit this need?
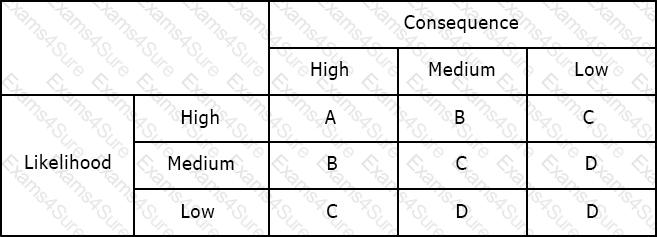
Using the risk matrix below, what is the risk of a medium likelihood event with high consequence?
What are the two sublayers of Layer 2?
Available Choices (select all choices that are correct)
A company needs to create a standardized interface for exchanging real-time plant data between heterogeneous control devices while maintaining a structured organization of data elements such as folders, classes, and methods. Which feature of OPC supports this requirement?
Which U.S. Department is responsible for the Chemical Facility Anti-Terrorism Standards (CFATS)?
What is the PRIMARY goal of the IACS Security Program (SP) requirements according to ISA/IEC 62443-2-1?
In what step of the development process of the CSMS is “Establish purpose, organizational support, resources, and scope” taken care of?
Which of the following staff is NOT mentioned as a stakeholder in the CSMS Program?



