
JN0-232 Practice Questions
Security, Associate (JNCIA-SEC)
Last Update 1 day ago
Total Questions : 65
Dive into our fully updated and stable JN0-232 practice test platform, featuring all the latest Associate JNCIA-SEC exam questions added this week. Our preparation tool is more than just a Juniper study aid; it's a strategic advantage.
Our free Associate JNCIA-SEC practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about JN0-232. Use this test to pinpoint which areas you need to focus your study on.
Which two statements are correct about the processing of NAT rules within a rule set? (Choose two.)
Which two statements are true about the NextGen Web Filtering (NGWF) feature on an SRX Series device? (Choose two.)
Which two statements about the null zone on an SRX Series Firewall are correct? (Choose two.)
You are asked to create a security policy that controls traffic allowed to pass between the Internet and private security zones. You must ensure that this policy is evaluated before all other policy types on your SRX Series device.
In this scenario, which type of security policy should you create?
Click the Exhibit button.
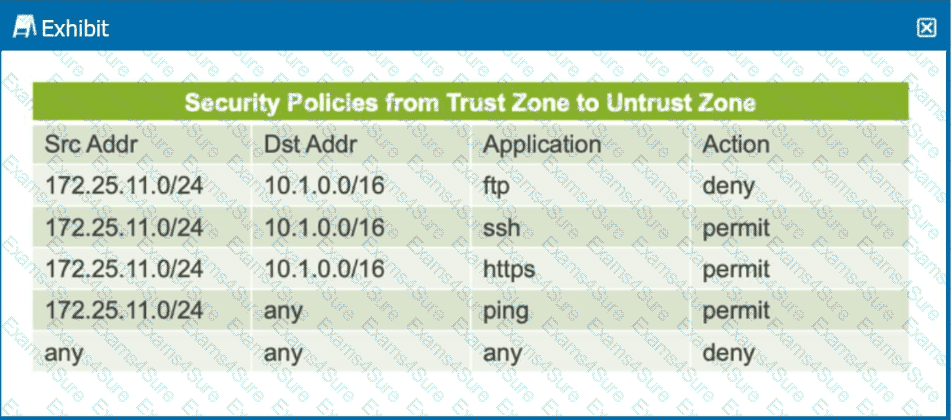
The exhibit shows a table representing security policies from the trust zone to the untrust zone.
In this scenario, which two statements are correct? (Choose two.)
You are troubleshooting traffic traversing the SRX Series Firewall and require detailed information showing how the flow module is handling the traffic.
How would you accomplish this task?



