
NSE7_SSE_AD-25 Practice Questions
Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator
Last Update 1 day ago
Total Questions : 81
Dive into our fully updated and stable NSE7_SSE_AD-25 practice test platform, featuring all the latest Fortinet Network Security Expert exam questions added this week. Our preparation tool is more than just a Fortinet study aid; it's a strategic advantage.
Our free Fortinet Network Security Expert practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about NSE7_SSE_AD-25. Use this test to pinpoint which areas you need to focus your study on.
You have configured FortiSASE Secure Private Access (SPA) deployment. Which statement is true about traffic flows? (Choose two answers)
A FortiSASE administrator is configuring a Secure Private Access (SPA) solution to share endpoint information with a corporate FortiGate.
Which three configuration actions will achieve this solution? (Choose three.)
One user has reported connectivity issues; no other users have reported problems. Which tool can the administrator use to identify the problem? (Choose one answer)
Refer to the exhibits.
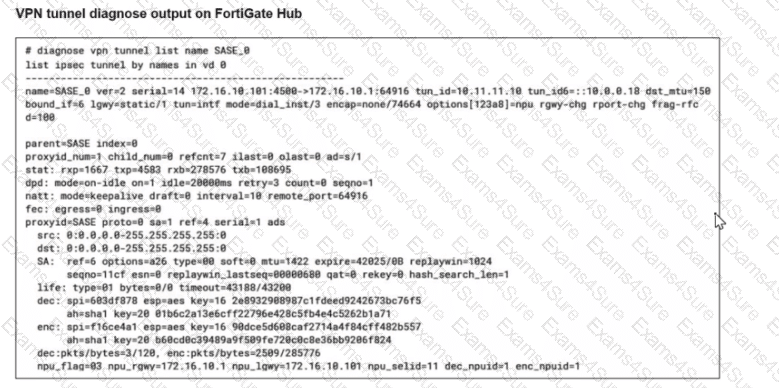
A FortiSASE administrator is trying to configure FortiSASE as a spoke to a FortiGate hub. The tunnel is up to the FortiGale hub. However, the administrator is not able to ping the webserver hosted behind the FortiGate hub.
Based on the output, what is the reason for the ping failures?
What are the key differences between the FortiSASE BGP per overlay and BGP on loopback routing design methods? (Choose one answer)
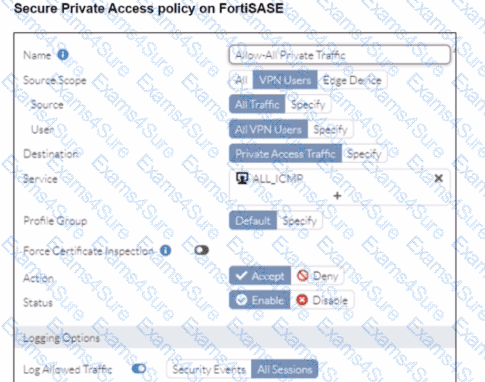
Refer to the exhibit.
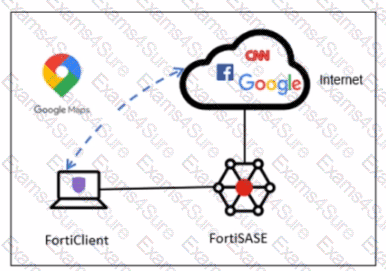
A company has a requirement to inspect all the endpoint internet traffic on FortiSASE, and exclude Google Maps traffic from the FortiSASE VPN tunnel and redirect it to the endpoint physical Interface.
Which configuration must you apply to achieve this requirement?
A FortiSASE customer has been enforcing always-on VPN for their remote users running FortiClient. What option can be enabled under the customer’s Endpoint Profile to allow them access different resources located in the same L2 network? (Choose one answer)
When viewing the daily summary report generated by FortiSAS
E.
the administrator notices that the report contains very little data. What is a possible explanation for this almost empty report?


