Practitioner Practice Questions
Palo Alto Networks Cybersecurity Practitioner (PCCP)
Last Update 2 days ago
Total Questions : 227
Dive into our fully updated and stable Practitioner practice test platform, featuring all the latest Certified Cybersecurity Associate exam questions added this week. Our preparation tool is more than just a Paloalto Networks study aid; it's a strategic advantage.
Our free Certified Cybersecurity Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about Practitioner. Use this test to pinpoint which areas you need to focus your study on.
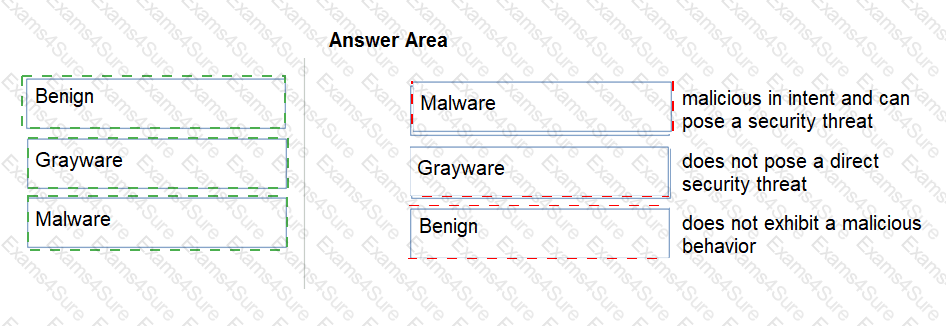
Match the Palo Alto Networks WildFire analysis verdict with its definition.
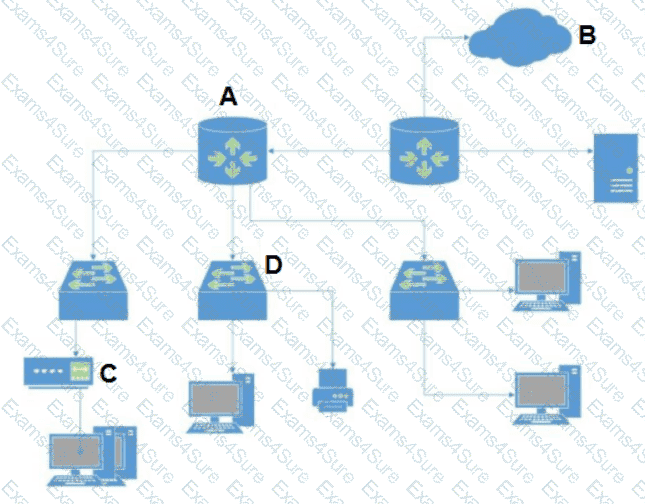
In which situation would a dynamic routing protocol be the quickest way to configure routes on a router?
On an endpoint, which method is used to protect proprietary data stored on a laptop that has been stolen?
What is the recommended method for collecting security logs from multiple endpoints?
Layer 4 of the TCP/IP Model corresponds to which three Layer(s) of the OSI Model? (Choose three.)