
PT0-003 Practice Questions
CompTIA PenTest+ Exam
Last Update 3 days ago
Total Questions : 330
Dive into our fully updated and stable PT0-003 practice test platform, featuring all the latest PenTest+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free PenTest+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about PT0-003. Use this test to pinpoint which areas you need to focus your study on.
Which of the following is within the scope of proper handling and is most crucial when working on a penetration testing report?
A penetration tester exports the following CSV data from a scanner. The tester wants to parse the data using Bash and input it into another tool.
CSV data before parsing:
cat data.csv
Host, IP, Username, Password
WINS212, 10.111.41.74, admin, Spring11
HRDB, 10.13.9.212, hradmin, HRForTheWin
WAS01, 192.168.23.13, admin, Snowfall97
Intended output:
admin Spring11
hradmin HRForTheWin
admin Snowfall97
Which of the following will provide the intended output?
A penetration tester finds that an application responds with the contents of the /etc/passwd file when the following payload is sent:
< ?xml version= " 1.0 " ? >
< !DOCTYPE data [ < !ENTITY foo SYSTEM " file:///etc/passwd " > ] >
< test > & foo; < /test >
Which of the following should the tester recommend in the report to best prevent this type of vulnerability?
During an assessment, a penetration tester obtains a low-privilege shell and then runs the following command:
findstr /SIM /C: " pass " *.txt *.cfg *.xml
Which of the following is the penetration tester trying to enumerate?
During an assessment, a penetration tester obtains access to an internal server and would like to perform further reconnaissance by capturing LLMNR traffic. Which of the following tools should the tester use?
During a preengagement activity with a new customer, a penetration tester looks for assets to test. Which of the following is an example of a target that can be used for testing?
A tester gains initial access to a server and needs to enumerate all corporate domain DNS records. Which of the following commands should the tester use?
During an engagement, a penetration tester receives a list of target systems and wants to enumerate them for possible vulnerabilities. The tester finds the following script on the internet:
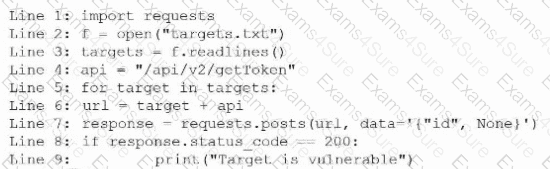
After running the script, the tester runs the following command:
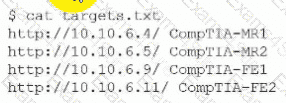
Which of the following should the tester do next?
After obtaining a reverse shell, a penetration tester identifies a locally cloned Git repository that contains thousands of files and directories on a Windows machine. The tester suspects there could be sensitive information related to “ProjectX.” Which of the following commands should the tester use in a script to identify potential files to produce the best results?
During an assessment, a penetration tester gains access to one of the internal hosts. Given the following command:
schtasks /create /sc onlogon /tn " Windows Update " /tr " cmd.exe /c reverse_shell.exe "
Which of the following is the penetration tester trying to do with this code?



