
RH133 Practice Questions
Red Hat Linux System Administration
Last Update 3 hours ago
Total Questions : 336
Dive into our fully updated and stable RH133 practice test platform, featuring all the latest RHCT exam questions added this week. Our preparation tool is more than just a RedHat study aid; it's a strategic advantage.
Our free RHCT practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about RH133. Use this test to pinpoint which areas you need to focus your study on.
Which of the following Linux commands can be used to set an expiration date for a user's password?
Which of the following commands is used to start or stop a standalone service immediately?
Which of the following files contain messages and errors from security-related system?
Which of the following command is used to list the current routing table in Linux?
You work as a Network Administrator for Perfect World Inc. The company has a Linux-based network. You have configured a Linux server to connect to the Internet. Before connecting it to the Internet, you want to check all the files on which SUID has been set. Which of the following commands will you choose to list all such programs?
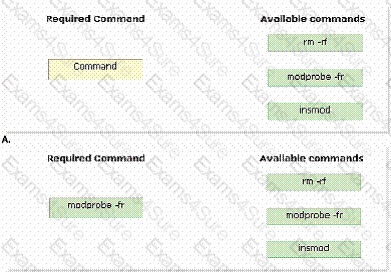
John works as a Network Administrator for Perfect Solutions Inc. The company has a Linux-based network. John is working as a root user on the Linux operating system. John wants to remove some installed kernel modules. Which of the following commands will John use to accomplish his task?
You work as a Network Administrator for Net Perfect Inc. The company has a Linux-based network. You have created a folder named Report. You have made David the owner of the folder.
The members of a group named JAdmin can access the folder and have Read, Write, and Execute permissions. No other user can access the folder. You want to ensure that the members of the JAdmin group do not have Write permission on the folder. Also, you want other users to have Read permission on the Report folder.
Which of the following commands will you use to accomplish the task?
John works as a Network Administrator for Perfect Solutions Inc. The company has a Linux-based network. John is working as a root user on the Linux operating system. He wants to change the quota setting of the user named Mari
A.
Which of the following commands will he use to accomplish the task?John works as a Network Administrator for Perfect Solutions Inc. The company has a Linux-based network. John is working as a root user on the Linux operating system. The company is using the host-based access control to avoid unwanted access of the malicious users. John wants to add a new user, which can use X applications from the remote computer. Which of the following commands will John use to accomplish his task?
Each correct answer represents a complete solution. Choose all that apply.



