
300-730 Practice Questions
Implementing Secure Solutions with Virtual Private Networks (SVPN)
Last Update 2 days ago
Total Questions : 175
Dive into our fully updated and stable 300-730 practice test platform, featuring all the latest CCNP Security exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCNP Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 300-730. Use this test to pinpoint which areas you need to focus your study on.
Which redundancy protocol must be implemented for IPsec stateless failover to work?
Cisco AnyConnect clients need to transfer large files over the VPN sessions. Which protocol provides the best throughput?
Which Cisco AnyConnect component ensures that devices in a specific internal subnet are only accessible using port 443?
Refer to the exhibit.
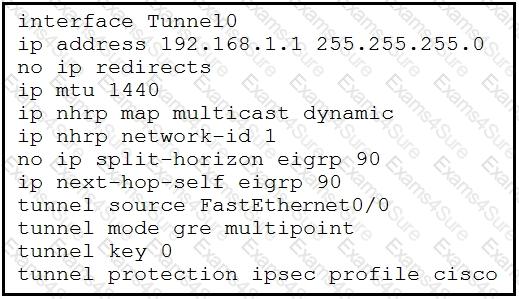
DMVPN spoke-to-spoke traffic works, but it passes through the hub, and never sends direct spoke-to-spoke traffic. Based on the tunnel interface configuration shown, what must be configured on the hub to solve the issue?
A network engineer must design a clientless VPN solution for a company. VPN users must be able to access several internal web servers. When reachability to those web servers was tested, it was found that one website is not being rewritten correctly by the AS
A.
What is a potential solution for this issue while still allowing it to be a clientless VPN setup?While troubleshooting, an engineer finds that the show crypto isakmp sa command indicates that the last state of the tunnel is MM_KEY_EXCH. What is the next step that should be taken to resolve this issue?
On a FlexVPN hub-and-spoke topology where spoke-to-spoke tunnels are not allowed, which command is needed for the hub to be able to terminate FlexVPN tunnels?
Refer to the exhibit.
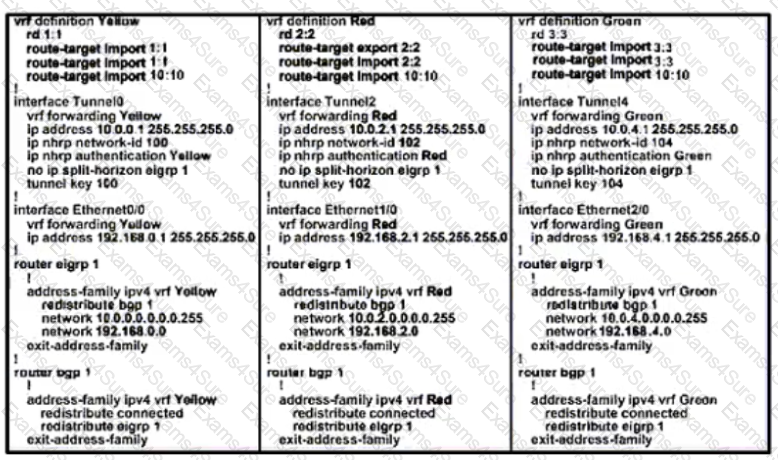
Based on the configuration output, what is the VPN technology?



