
NCP-NS-7.5 Practice Questions
Nutanix Certified Professional - Network and Security (NCP-NS) 7.5
Last Update 2 days ago
Total Questions : 106
Dive into our fully updated and stable NCP-NS-7.5 practice test platform, featuring all the latest NCP-NS exam questions added this week. Our preparation tool is more than just a Nutanix study aid; it's a strategic advantage.
Our free NCP-NS practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about NCP-NS-7.5. Use this test to pinpoint which areas you need to focus your study on.
An administrator has observed the following message: Which two statements most accurately describe the security hitlog captured above? (Choose two.)
A VDI policy in Flow Network Security allows access to specific resources only when users from the Admins Active Directory group log into a VM. Some administrators report that when they log in to certain VMs, access is blocked (default deny applies), while the same user accounts work correctly when logged on to other VMs. When checking the VM details in Prism Central, operations observes that the expected dynamic category based on the logged-in AD user is not assigned on the affected VMs. What is the most likely reason for this behavior?
Before creating a new Application Security Policy in Prism Central, what prerequisite must exist?
An administrator has a VPC with multiple overlay subnets and a VPN gateway configured for site-to-site connectivity. During testing, the administrator noticed fragmented packets and poor performance. Which configuration change resolves this issue without disabling VPN?
An administrator plans to upgrade the Network Controller in a Flow Virtual Networking deployment. The environment includes multiple AHV clusters managed by Prism Central. Which prerequisite must be verified before upgrading the Network Controller?
When configuring an Application policy, an administrator defines a VM Category Application:MySQL as a Secured Entity. The administrator wants to ensure that traffic between VMs in the Secured Entity is kept to only required replication traffic on the default mysql service port. How should the administrator best accomplish this?
Refer to Exhibit:
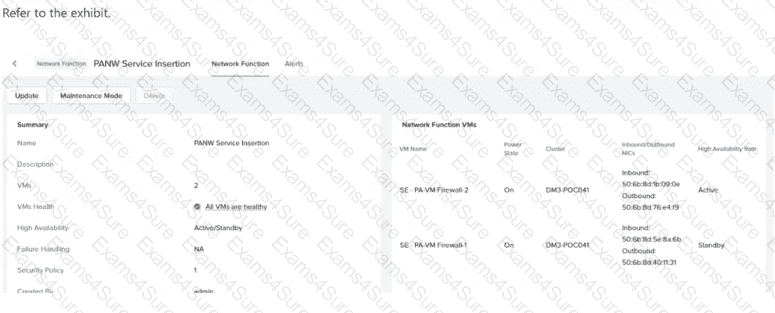
An organization uses an FNS-NG Service Chain to steer application traffic through a pair of third-party firewall Network Function VMs operating in Active/Standby mode. Users suddenly report that all application access is blocked. The administrator reviews Prism Central - > Network & Security - > Network Functions, where the summary shown in the exhibit is displayed. Additional information: Alert: "Network Function 'PANW Service Insertion' virtual NIC pair(s) are unhealthy." Both firewall VMs are powered on and reachable. The security policy using the service chain has not been changed. Based on the exhibit and findings, what is the most likely cause of the traffic outage?
An administrator has created a VPC with the following subnets: 10.1.1.0/24 10.1.2.0/24 10.1.3.0/24 What action must be taken for these networks to be externally routable?
In Nutanix Flow, which action transitions a security policy from observing traffic to actively enforcing the rules?



