
NCP-NS-7.5 Practice Questions
Nutanix Certified Professional - Network and Security (NCP-NS) 7.5
Last Update 3 days ago
Total Questions : 106
Dive into our fully updated and stable NCP-NS-7.5 practice test platform, featuring all the latest NCP-NS exam questions added this week. Our preparation tool is more than just a Nutanix study aid; it's a strategic advantage.
Our free NCP-NS practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about NCP-NS-7.5. Use this test to pinpoint which areas you need to focus your study on.
An administrator is designing a new Transit VPC to service multiple Tenant VPCs. While adding subnets, the administrator must choose the correct network type supported by Flow Virtual Networking for this VP
C.
Which network type is supported for subnets inside a Transit VPC in Flow Virtual Networking?Which policy is used to isolate a compromised VM in the most efficient way possible?
Which statement accurately describes the behavior of a Flow Network Security policy operating in Monitor mode?
Refer to Exhibit:
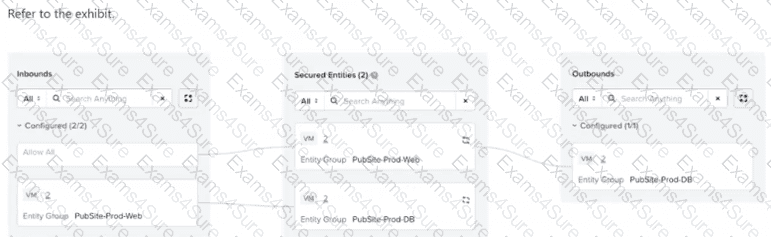
An administrator is tasked with configuring an application policy for a two-tier public website with Web and DB components. The database servers need to communicate with each other for replication, but the web servers should not be able to communicate with each other. The administrator configures the policy... and sets it to Enforce mode. Later testing reveals that the web servers are able to communicate with each other. What should the administrator do to resolve this?
An administrator has a requirement to capture application flow data for a policy in Monitor mode and export those events to an external SIEM for correlation with other logs. Which two actions are required to achieve this? (Choose two.)
An administrator observes a Network Controller Unreachable alert in Prism Central for a specific AHV cluster. All other management tasks for the cluster from Prism Central are succeeding and the cluster itself reports a healthy status. Which step is the most appropriate to investigate the cause of this specific alert?
An administrator needs to isolate communication between VMs in Production and Development environments. Each VM is categorized by Environment and Site category values. The administrator wants this isolation to apply only to VMs located at Site: Branch-001. Which configuration best meets the requirement?
When cloning a Flow Network Security policy, what should be verified before enabling Enforce mode?
Which two options are supported as a Secured Entity in Flow Network Security Application Policies? (Choose two.)
An administrator needs to delegate the management of security policies to a dedicated SecOps team. To enforce the principle of least privilege, the administrator assigns the predefined Flow Policy Author role to a user on the team. The user confirms they can create, monitor, and enforce security policies. However, when attempting to build a new application security policy for a set of newly deployed VMs, the user reports they are unable to create a new category to group these VMs. The option is not available in the Prism Central UI. Which statement explains this behavior?



