PPAN01 Practice Questions
Certified Threat Protection Analyst Exam
Last Update 2 days ago
Total Questions : 52
Dive into our fully updated and stable PPAN01 practice test platform, featuring all the latest Threat Protection Analyst exam questions added this week. Our preparation tool is more than just a Proofpoint study aid; it's a strategic advantage.
Our free Threat Protection Analyst practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about PPAN01. Use this test to pinpoint which areas you need to focus your study on.
Refer to Exhibit:
X-Proofpoint-Banner-Trigger: inbound
MIM-version: 1.0
Content-Type: multipart/mixed; boundary="boundary-1698346305"
X-CLX-Shades: MLX
X-Proofpoint-Virus-Version: vendor=baseguard
engine=ICAP:2.0.272,Aquarius:18.0.987,Hydra:6.0.619,FMLib:17.11.176.26 definitions=2023-10-26_22,2023-10-26_01,2023-05-22_02
X-Proofpoint-Spam-Details: rule=spam policy=default score=89 bulkscore=0 phishscore=0 mlxlogscore=-91 suspectscore=0 malwarescore=0 adultscore=0 spamscore=89 classifier=spam adjust=0 reason=mlx scancount=l engine=8.12.0-2310240000 definitions=main-2310260209
In the process of reviewing a false positive, you see the following email header. What was the reason the message was quarantined by the Proofpoint Protection Server?
Which TAP condemnation results from an analysis of emails submitted via Proofpoint ZenGuide Report Suspicious (formerly PhishAlarm)?
What are two unique benefits of submitting false positives via the support portal? (Select two.)
Which of the following is an item that should be included in an incident report as part of the post-incident debrief?
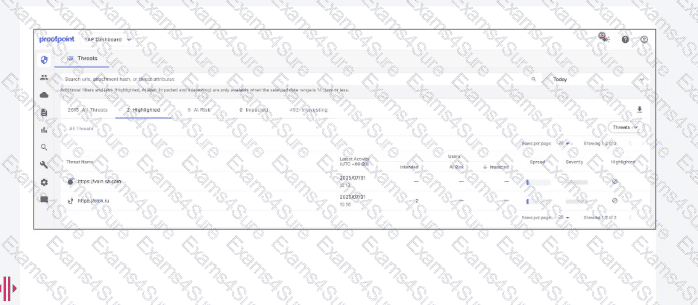
What is the first action a security analyst should take when beginning to review and prioritize alerts from Targeted Attack Protection (TAP)?
Which two threat protection capabilities are available as part of Proofpoint’s Targeted Attack Protection (TAP)? (Select two.)
An analyst has been tasked with providing a report that can be used to prioritise investigations based on a user's Attack Index score. Which report would be most suitable for this purpose?