SC-401 Practice Questions
Administering Information Security in Microsoft 365
Last Update 2 days ago
Total Questions : 203
Dive into our fully updated and stable SC-401 practice test platform, featuring all the latest Microsoft Certified: Information Security Administrator Associate exam questions added this week. Our preparation tool is more than just a Microsoft study aid; it's a strategic advantage.
Our free Microsoft Certified: Information Security Administrator Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about SC-401. Use this test to pinpoint which areas you need to focus your study on.
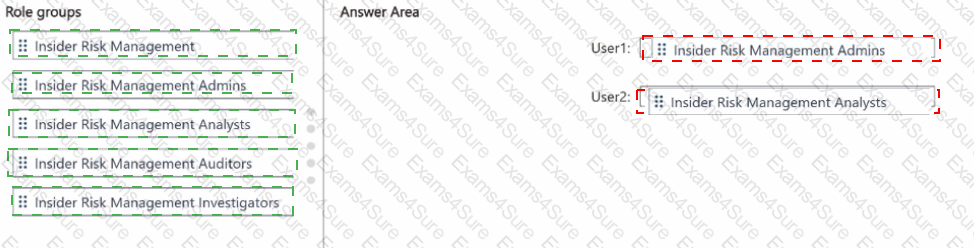
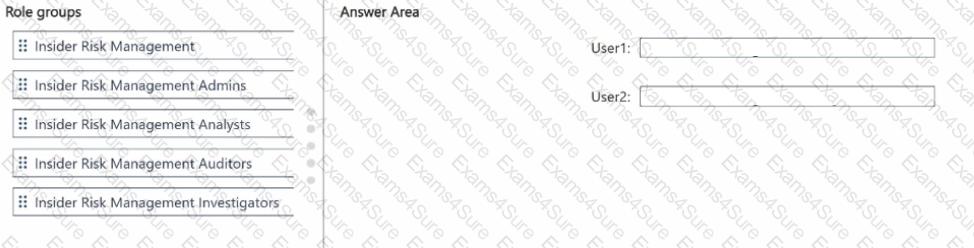
You have a Microsoft 365 E5 subscription that contains two users named User! and User2.
You need to implement insider risk management. The solution must meet the following requirements:
• Ensure that User1 can create insider risk management policies.
• Ensure that User2 can use content captured by using insider risk management policies
• Follow the principle of least privilege.
To which role group should you add each user? To answer, drag the appropriate role groups to the correct users. Each role group may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
You have Microsoft 365 E5 subscription.
You create two alert policies named Policy1 and Policy2 that will be triggered at the times shown in the following table.
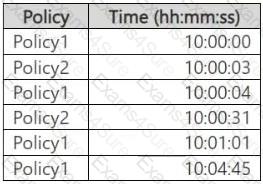
How many alerts will be added to the Microsoft Purview portal?
You have a Microsoft 365 E5 tenant that contains a user named User1. User1 is assigned the Compliance Administrator role. User1 cannot view the regular expression in the IP Address sensitive info type. You need to ensure that User! can view the regular expression. What should you do?
You have a Microsoft 365 E5 subscription.
You plan to deploy Microsoft Purview Data Security Posture Management for Al (DSPM for Al) to protect company data that contains Personally Identifiable Information (Pll) from being shared with third-party generative Al tools.
You need to complete the prerequisites for the planned deployment.
Which two Microsoft Purview solutions should you use? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
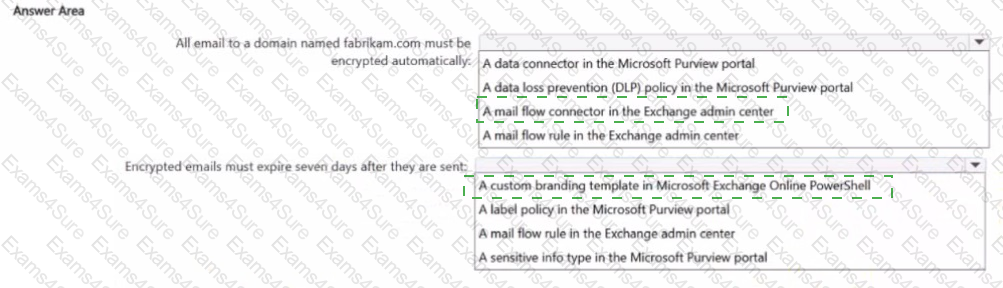
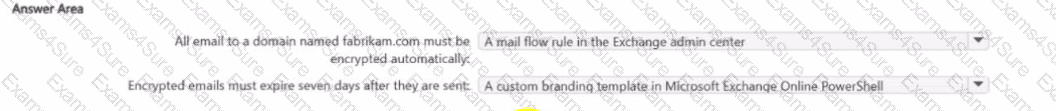
You are implementing Microsoft Purview Advanced Message Encryption for a Microsoft 365 tenant named contoso.com You need to meet the following requirements:
• All email to a domain named (abrikam.com must be encrypted automatically.
• Encrypted emails must expire seven days after they are sent
What should you configure for each requirement? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
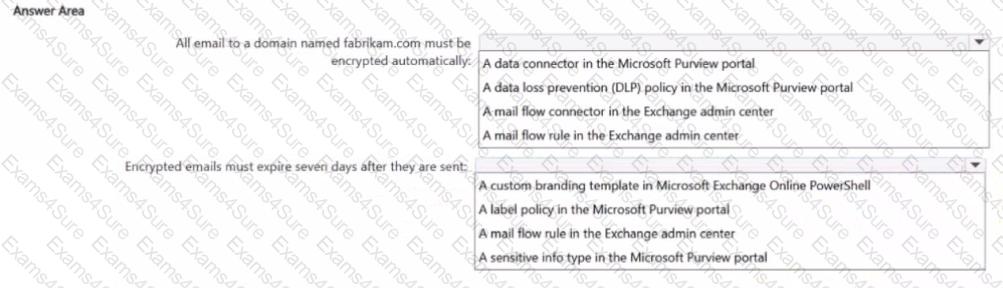
HOTSPOT
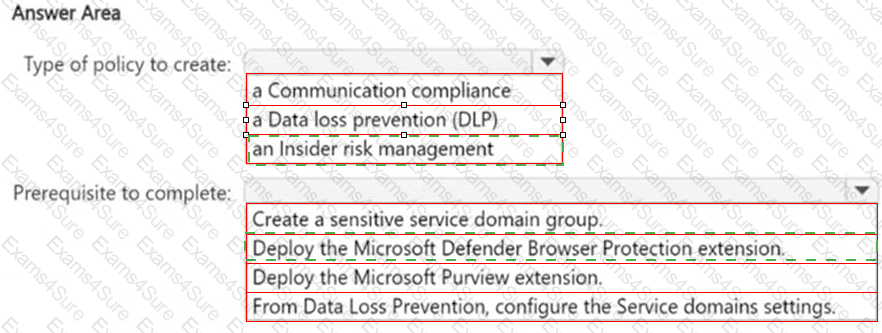
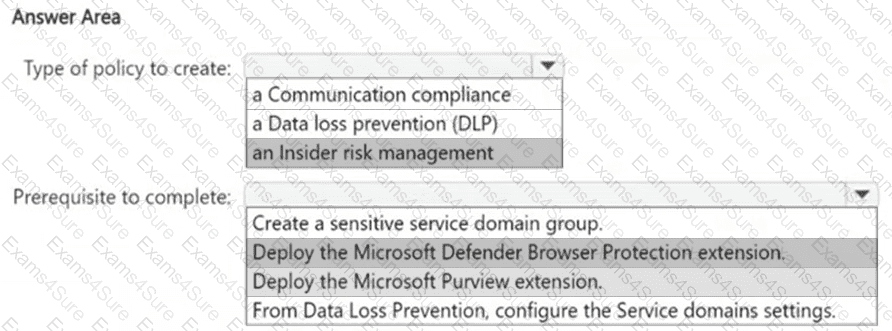
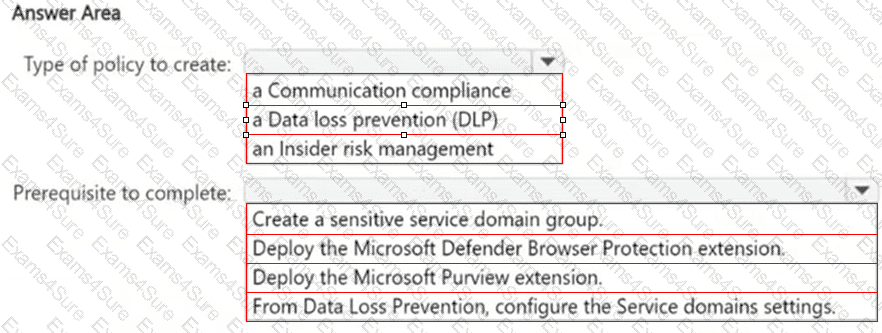
You have a Microsoft 365 E5 subscription that uses Microsoft Purview.
You need ensure that an incident will be generated when a user visits a phishing website.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 subscription.
You have a user named User1. Several users have full access to the mailbox of User1.
Some email messages sent to User1 appear to have been read and deleted before the user viewed them.
When you search the audit log in the Microsoft Purview portal to identify who signed in to the mailbox of User1, the results are blank.
You need to ensure that you can view future sign-ins to the mailbox of User1.
Solution: You run the Set-MailboxFolderPermission -Identity " User1 " -User User1@contoso.com -AccessRights Owner command.
Does that meet the goal?
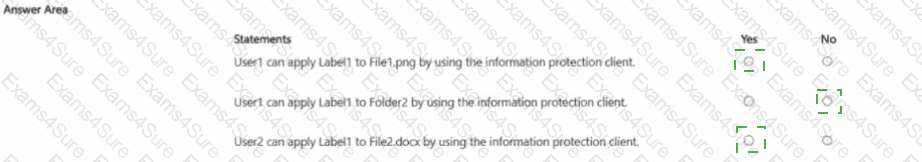
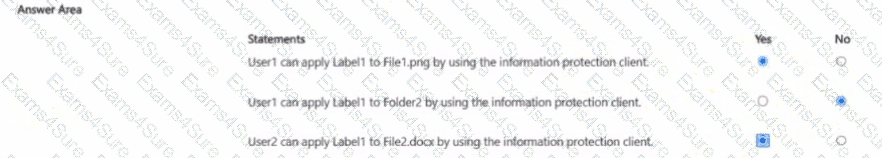
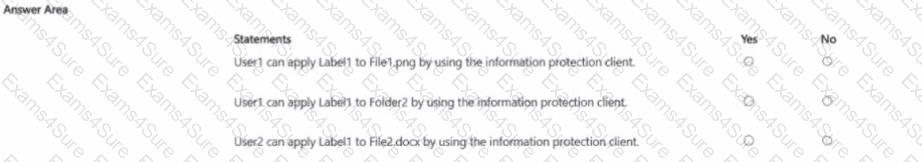
You have a Microsoft 365 IS subscription that contains the resources shown in the following table.
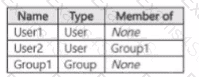
The subscription contains a Windows 11 device named Device 1 and has the Microsoft Purview Information Protection client installed. Device i contains the resources shown in the following table.
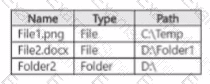
You publish a sensitivity label named Label1 to User1 and Group1.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
You have a Microsoft 365 E5 subscription.
You need to create static retention policies for the following locations:
● Teams chats
● Exchange email
● SharePoint sites
● Microsoft 365 Groups
● Teams channel messages
What is the minimum number of retention policies required?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You recently discovered that the developers at your company emailed Azure Storage Account keys in plain text to third parties.
You need to ensure that when Azure Storage Account keys are emailed, the emails are encrypted.
Solution: You configure a mail flow rule that matches a sensitive info type.
Does this meet the goal?