SC-401 Practice Questions
Administering Information Security in Microsoft 365
Last Update 2 days ago
Total Questions : 203
Dive into our fully updated and stable SC-401 practice test platform, featuring all the latest Microsoft Certified: Information Security Administrator Associate exam questions added this week. Our preparation tool is more than just a Microsoft study aid; it's a strategic advantage.
Our free Microsoft Certified: Information Security Administrator Associate practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about SC-401. Use this test to pinpoint which areas you need to focus your study on.
You have a Microsoft 565 subscription that contains 100 users and a Microsoft 365 group named Group1. All users have Windows 11 devices and use Microsoft SharePoint Online and Exchange Online. A sensitivity label named Label! is published as the default label for Group1. You add two sublabels named Sublabel1 and Sublabel2 lo Label1. You need to ensure that the settings in Sublabel 1 are applied by default to Group 1. What should you do?
You have a Microsoft 365 subscription.
Users have devices that run Windows 11.
You plan to create a Microsoft Purview insider risk management policy that will detect when a user performs the following actions:
● Deletes files that contain a sensitive information type (SIT) from their device
● Copies files that contain a SIT to a USB drive
● Prints files that contain a SIT
You need to prepare the environment to support the policy.
What should you do?
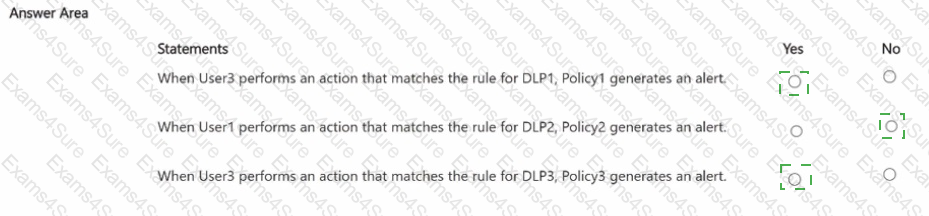
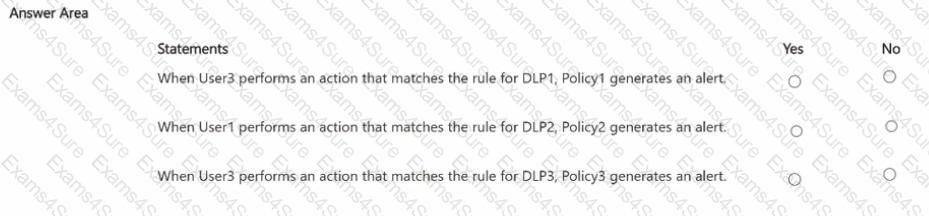
You have a Microsoft 365 E5 subscription that contains the users shown in the following table.

You have the data loss prevention (DLP) policies shown in the following table.
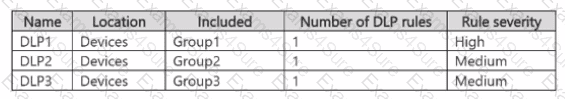
From Insider risk management, you configure a priority user group named PriGroup1 that contains User3 as a member. You have the insider risk policies shown in the following table.
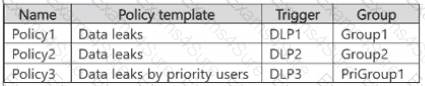
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
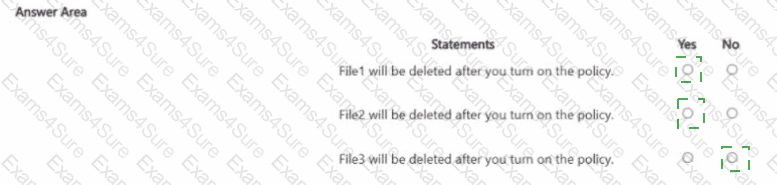
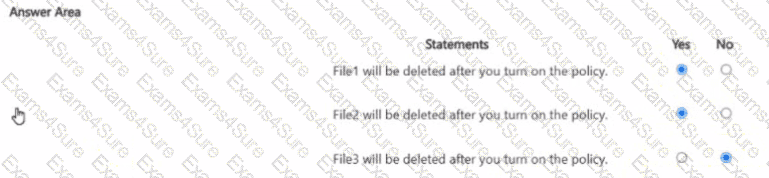
You have the files shown in the following table.
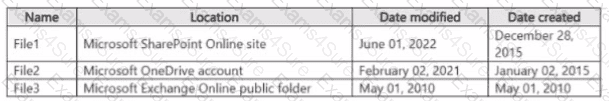
You configure a retention policy as shown > n the exhibit. (Click the Exhibit lab.)
The start of the retention period is based on when items are created. The current date is January 01. 207S.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
You are creating a custom trainable classifier to Identify organizational product codes referenced in Microsoft 36S content. You identify 300 files to use as seed content When? should you store the seed content?
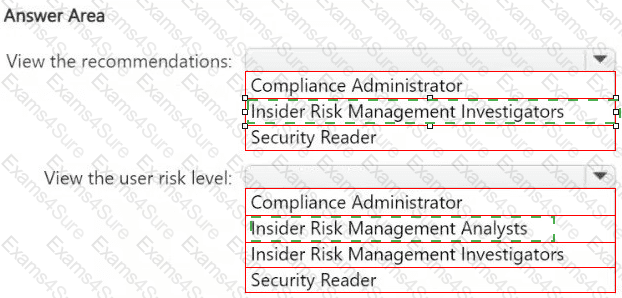
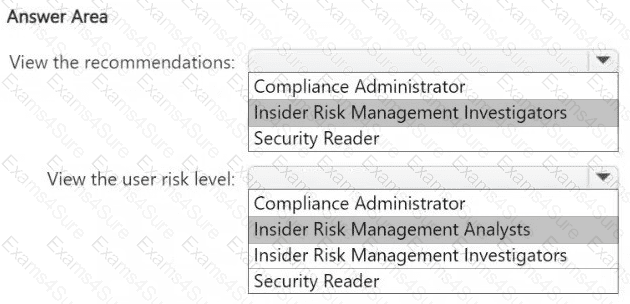
HOTSPOT
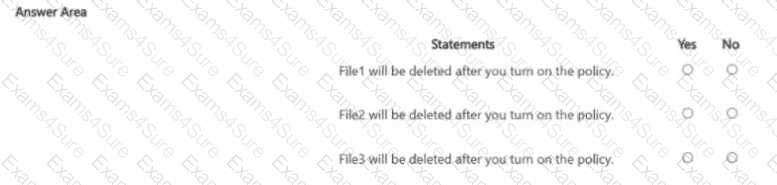
You have a Microsoft 365 E5 subscription that contains a user named User1.
You deploy Microsoft Purview Data Security Posture Management for AI (DSPM for AI).
You need to ensure that User1 can perform the following actions:
● View recommendations from the Recommendations page.
● View the user risk level for all events by using Activity explorer.
The solution must follow the principle of least privilege.
To which role group should you add User1 for each action? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 tenant that is opt-in for trainable classifiers.
You need to ensure that a user named User1 can create custom trainable classifiers. The solution must use the principle of least privilege.
Which role should you assign to User1?
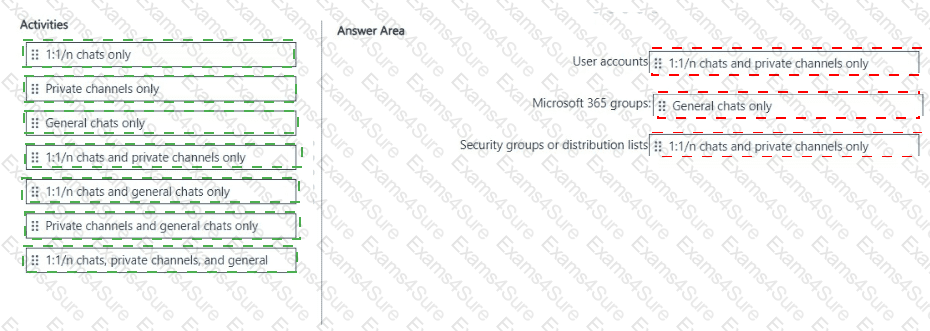
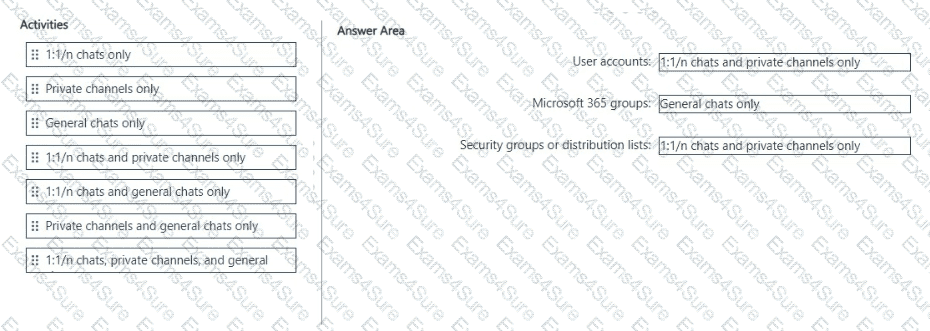
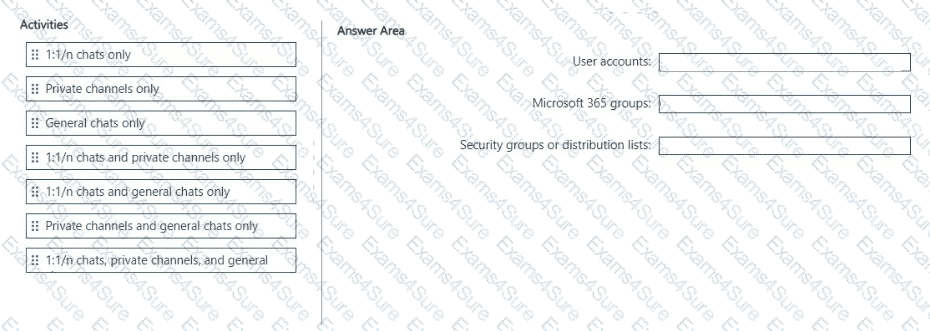
You have a Microsoft 365 £5 subscription.
You need to prevent the sharing of sensitive information in Microsoft Teams.
Which entities can you protect by applying a data loss prevention (DLP) policy to each resource? To answer, drag the appropriate activities to the correct entity. Each activity may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE; Each correct selection is worth one point.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 tenant and 500 computers that run Windows 11. The computers are onboarded to Microsoft Purview.
You discover that a third-party application named Tailspin_scanner.exe accessed protected sensitive information on multiple computers. Tailspin_scanner.exe is installed locally on the computers.
You need to block Tailspin_scanner.exe from accessing sensitive documents without preventing the application from accessing other documents.
Solution: From Microsoft Defender for Cloud Apps, you create an app discovery policy.
Does this meet the goal?
You have a Microsoft 36S ES subscription.
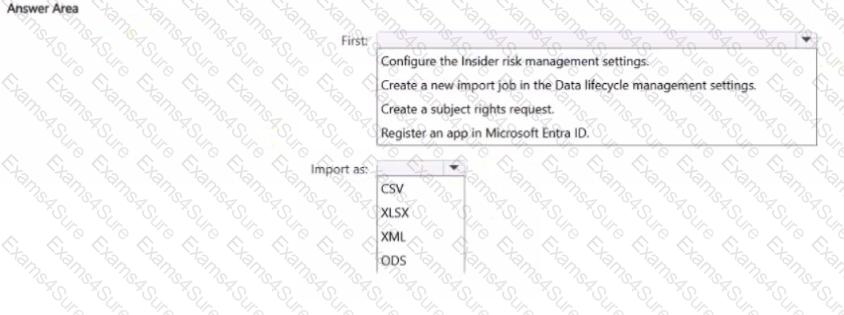
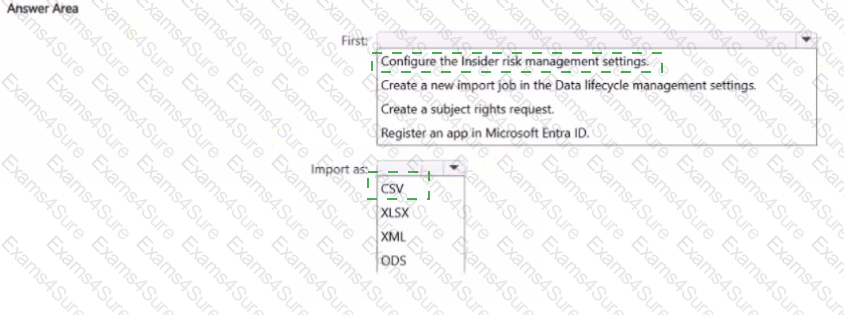
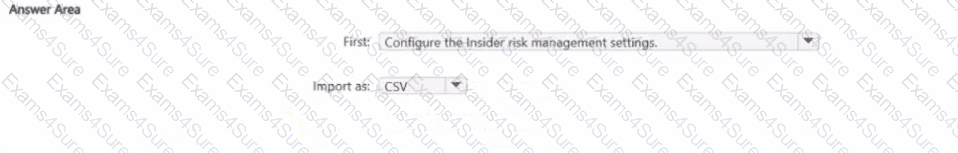
You plan to use the Microsoft Purview portal to map human resources (HR) data for use with insider risk management policies.
You need to add a data connector to import the HR data.
What should you do first and in which format should you import the data? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.