
SY0-701 Practice Questions
CompTIA Security+ Exam 2026
Last Update 3 days ago
Total Questions : 814
Dive into our fully updated and stable SY0-701 practice test platform, featuring all the latest CompTIA Security+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA Security+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about SY0-701. Use this test to pinpoint which areas you need to focus your study on.
A manufacturing organization receives the results from a penetration test. According to the results, legacy devices that are critical to continued business function display vulnerabilities. The devices have minimal vendor support and should be segmented and monitored closely. Which of the following devices were most likely identified?
Which of the following uses proprietary controls and is designed to function in harsh environments over many years with limited remote access management?
An administrator was notified that a user logged in remotely after hours and copied large amounts of data to a personal device.
Which of the following best describes the user’s activity?
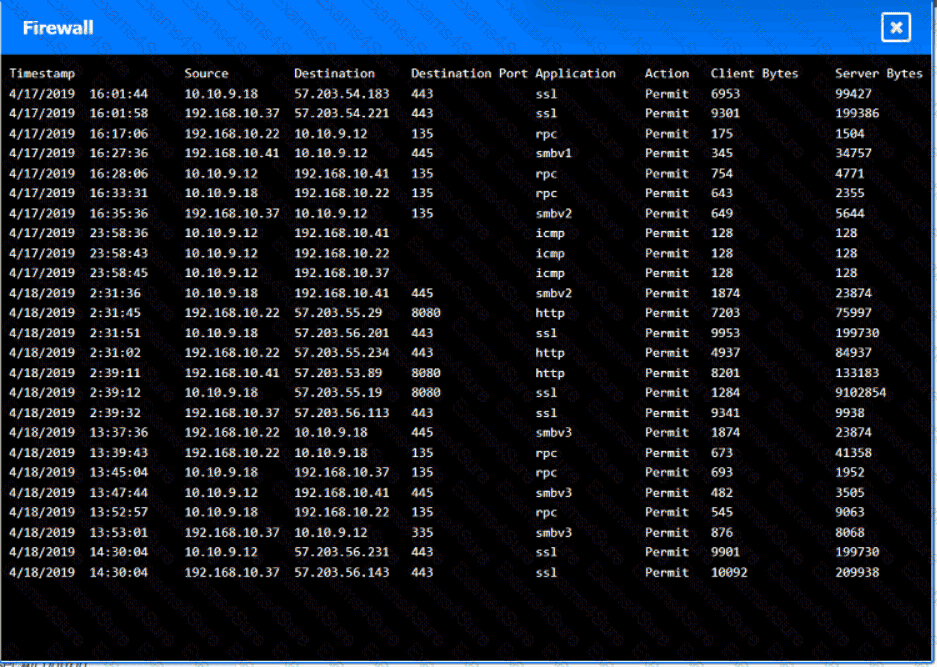
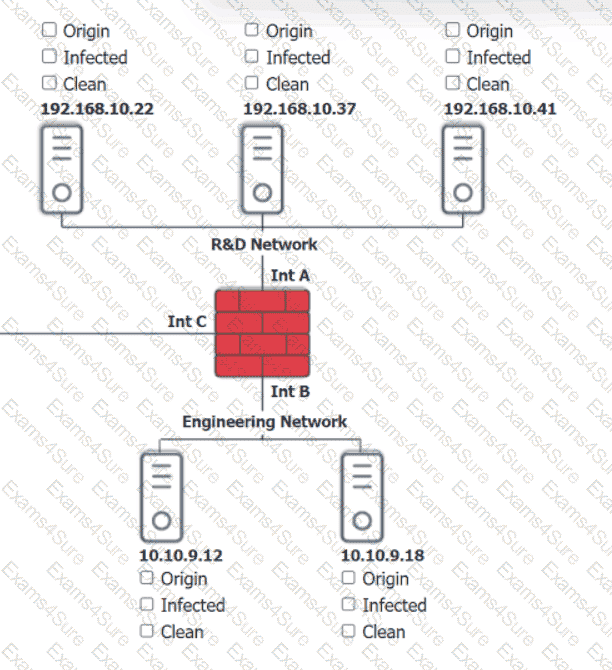
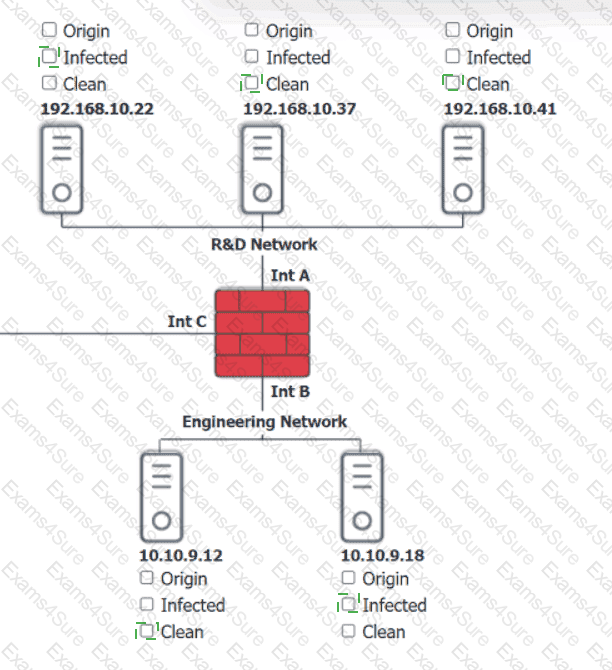
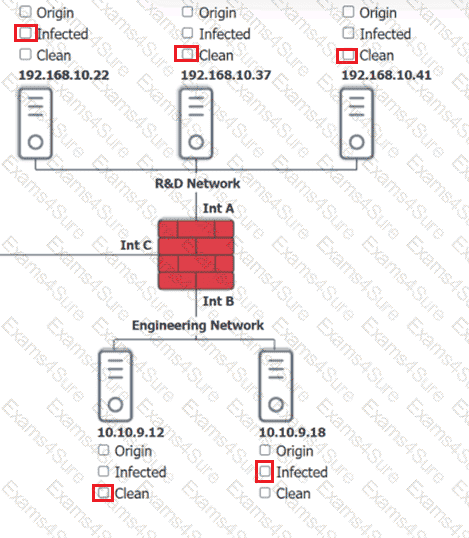
You are security administrator investigating a potential infection on a network.
Click on each host and firewall. Review all logs to determine which host originated the Infecton and then deny each remaining hosts clean or infected.
A systems administrator needs to encrypt all data on employee laptops. Which of the following encryption levels should be implemented?
A company performs risk analysis on its equipment and estimates it will experience about ten incidents over a five-year period. Which of the following is the correct ARO for the equipment?
A security architect wants to prevent employees from receiving malicious attachments by email. Which of the following functions should the chosen solution do?
An attacker used XSS to compromise a web server. Which of the following solutions could have been used to prevent this attack?
The Chief Information Officer (CIO) asked a vendor to provide documentation detailing the specific objectives within the compliance framework that the vendor ' s services meet. The vendor provided a report and a signed letter stating that the services meet 17 of the 21 objectives. Which of the following did the vendor provide to the CIO?
Cadets speaking a foreign language are using company phone numbers to make unsolicited phone calls lo a partner organization. A security analyst validates through phone system logs that the calls are occurring and the numbers are not being spoofed. Which of the following is the most likely explanation?
An employee asks a security analyst to scan a suspicious email that contains a link to a file on a file-sharing site. The analyst determines that the file is safe after downloading and scanning the file with antivirus software. When the employee opens the file, their device is infected with ransomware. Which of the following steps should the analyst have taken?
A company is concerned with supply chain compromise of new servers and wants to limit this risk. Which of the following should the company review first?
A U.S.-based cloud-hosting provider wants to expand its data centers to new international locations. Which of the following should the hosting provider consider first?
Which of the following security threats aims to compromise a website that multiple employees frequently visit?
A company wants to improve the availability of its application with a solution that requires minimal effort in the event a server needs to be replaced or added. Which of the following would be the best solution to meet these objectives?


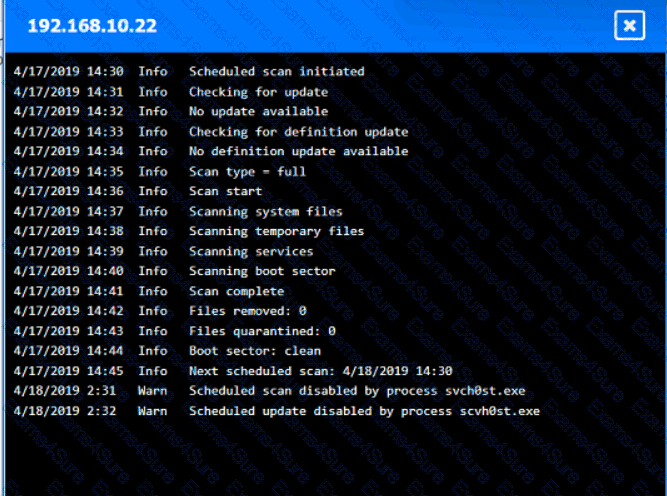
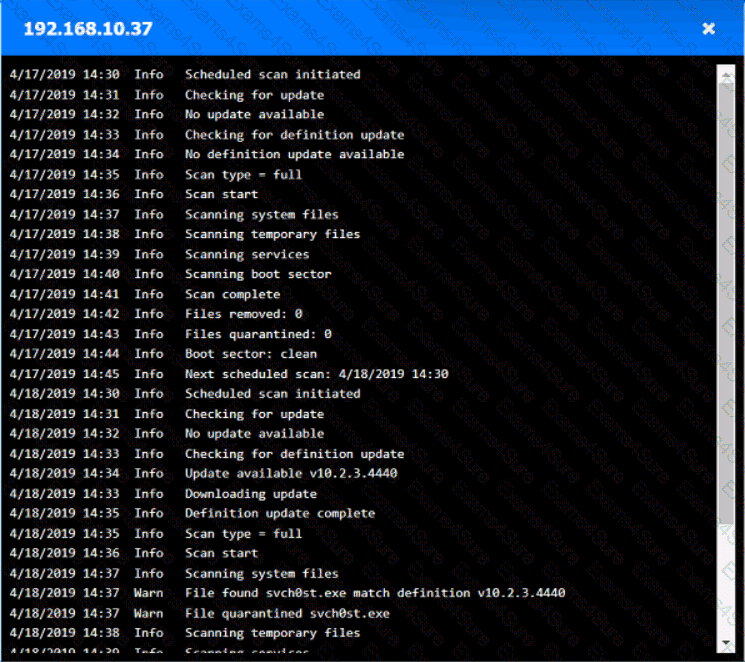
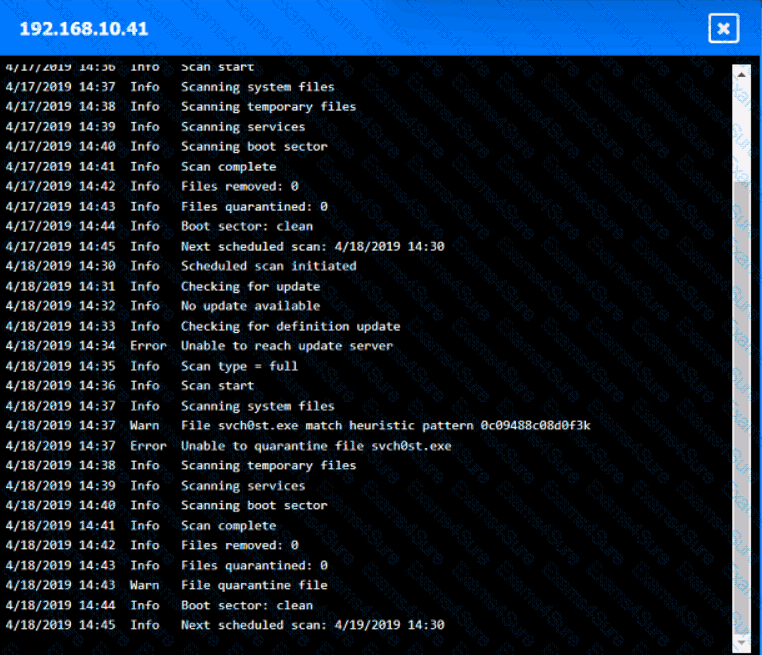
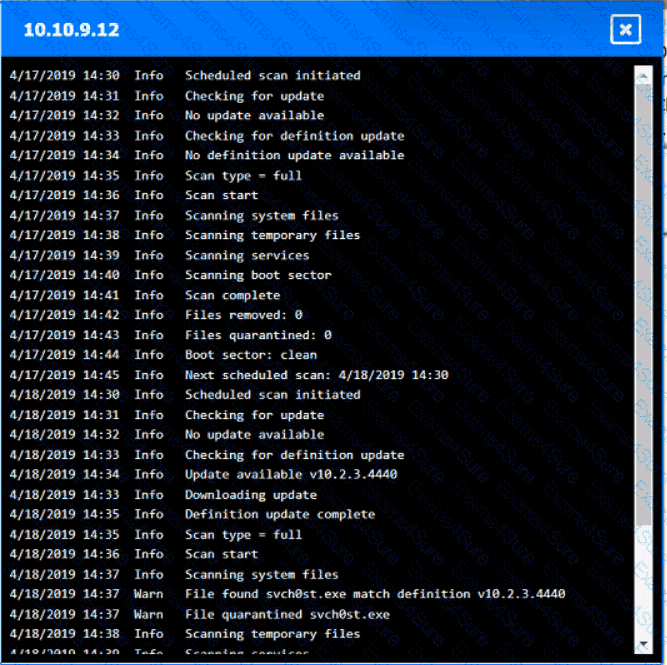
 A screenshot of a computer AI-generated content may be incorrect.
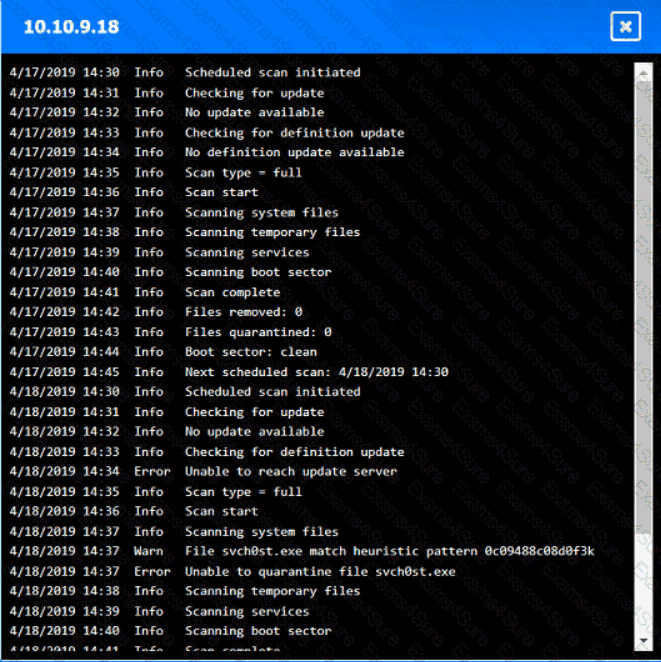
A screenshot of a computer AI-generated content may be incorrect.
