
SY0-701 Practice Questions
CompTIA Security+ Exam 2026
Last Update 2 days ago
Total Questions : 814
Dive into our fully updated and stable SY0-701 practice test platform, featuring all the latest CompTIA Security+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA Security+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about SY0-701. Use this test to pinpoint which areas you need to focus your study on.
Which of the following is most likely to be used as a just-in-time reference document within a security operations center?
A remote employee navigates to a shopping website on their company-owned computer. The employee clicks a link that contains a malicious file. Which of the following would prevent this file from downloading?
A security analyst reviews domain activity logs and notices the following:
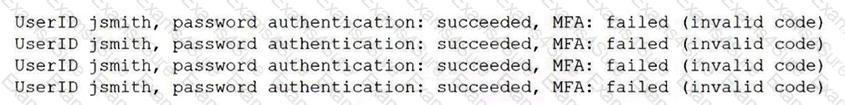
Which of the following is the best explanation for what the security analyst has discovered?
A malicious update was distributed to a common software platform and disabled services at many organizations. Which of the following best describes this type of vulnerability?
A company prevented direct access from the database administrators’ workstations to the network segment that contains database servers. Which of the following should a database administrator use to access the database servers?
A growing organization, which hosts an externally accessible application, adds multiple virtual servers to improve application performance and decrease the resource usage on individual servers Which of the following solutions is the organization most likely to employ to further increase performance and availability?
Which of the following threat actors is the most likely to be hired by a foreign government to attack critical systems located in other countries?
Which of the following should be used to ensure an attacker is unable to read the contents of a mobile device ' s drive if the device is lost?
A company requires hard drives to be securely wiped before sending decommissioned systems to recycling. Which of the following best describes this policy?
Which of the following receives logs from various devices and services, and then presents alerts?
Which of the following can be used to identify potential attacker activities without affecting production servers?
A company wants to track modifications to the code that is used to build new virtual servers. Which of the following will the company most likely deploy?
Which of the following is used to protect a computer from viruses, malware, and Trojans being installed and moving laterally across the network?
Which of the following exercises should an organization use to improve its incident response process?



