
CPEH-001 Practice Questions
Certified Professional Ethical Hacker (CPEH)
Last Update 4 days ago
Total Questions : 736
Dive into our fully updated and stable CPEH-001 practice test platform, featuring all the latest Information Systems Security exam questions added this week. Our preparation tool is more than just a GAQM study aid; it's a strategic advantage.
Our free Information Systems Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CPEH-001. Use this test to pinpoint which areas you need to focus your study on.
In Wireshark, the packet bytes panes show the data of the current packet in which format?
In which of the following password protection technique, random strings of characters are added to the password before calculating their hashes?
A pen tester is configuring a Windows laptop for a test. In setting up Wireshark, what river and library
are required to allow the NIC to work in promiscuous mode?
You need a tool that can do network intrusion prevention and intrusion detection, function as a network sniffer, and record network activity, what tool would you most likely select?
What network security concept requires multiple layers of security controls to be placed throughout an IT infrastructure, which improves the security posture of an organization to defend against malicious attacks or potential vulnerabilities?
What kind of Web application vulnerability likely exists in their software?
Study the snort rule given below:
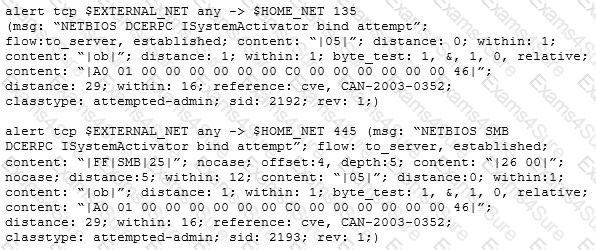
From the options below, choose the exploit against which this rule applies.
Which DNS resource record can indicate how long any "DNS poisoning" could last?
You went to great lengths to install all the necessary technologies to prevent hacking attacks, such as expensive firewalls, antivirus software, anti-spam systems and intrusion detection/prevention tools in your company's network. You have configured the most secure policies and tightened every device on your network. You are confident that hackers will never be able to gain access to your network with complex security system in place.
Your peer, Peter Smith who works at the same department disagrees with you.
He says even the best network security technologies cannot prevent hackers gaining access to the network because of presence of "weakest link" in the security chain.
What is Peter Smith talking about?



