
CPEH-001 Practice Questions
Certified Professional Ethical Hacker (CPEH)
Last Update 4 days ago
Total Questions : 736
Dive into our fully updated and stable CPEH-001 practice test platform, featuring all the latest Information Systems Security exam questions added this week. Our preparation tool is more than just a GAQM study aid; it's a strategic advantage.
Our free Information Systems Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CPEH-001. Use this test to pinpoint which areas you need to focus your study on.
This is an attack that takes advantage of a web site vulnerability in which the site displays content that includes un-sanitized user-provided data.
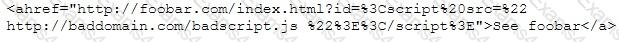
What is this attack?
Which of the following techniques does a vulnerability scanner use in order to detect a vulnerability on a target service?
Fingerprinting VPN firewalls is possible with which of the following tools?
What results will the following command yield: 'NMAP -sS -O -p 123-153 192.168.100.3'?
When utilizing technical assessment methods to assess the security posture of a network, which of the following techniques would be most effective in determining whether end-user security training would be beneficial?
During a penetration test, a tester finds a target that is running MS SQL 2000 with default credentials. The tester assumes that the service is running with Local System account. How can this weakness be exploited to access the system?
Which of the following examples best represents a logical or technical control?
A developer for a company is tasked with creating a program that will allow customers to update their billing and shipping information. The billing address field used is limited to 50 characters. What pseudo code would the developer use to avoid a buffer overflow attack on the billing address field?



