
Deep-Security-Professional Practice Questions
Trend Micro Certified Professional for Deep Security Exam
Last Update 1 day ago
Total Questions : 73
Dive into our fully updated and stable Deep-Security-Professional practice test platform, featuring all the latest Deep Security exam questions added this week. Our preparation tool is more than just a Trend Micro study aid; it's a strategic advantage.
Our free Deep Security practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about Deep-Security-Professional. Use this test to pinpoint which areas you need to focus your study on.
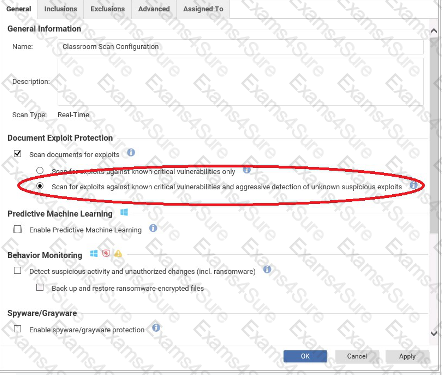
Based on the configuration setting highlighted in the exhibit, what behavior can be expected during a malware scan?
Which of the following statements correctly identifies the purpose of the Integrity Monitoring Protection Module?



