
EC0-350 Practice Questions
Ethical Hacking and Countermeasures V8
Last Update 10 hours ago
Total Questions : 878
Dive into our fully updated and stable EC0-350 practice test platform, featuring all the latest Certified Ethical Hacker exam questions added this week. Our preparation tool is more than just a ECCouncil study aid; it's a strategic advantage.
Our free Certified Ethical Hacker practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about EC0-350. Use this test to pinpoint which areas you need to focus your study on.
The following is a sample of output from a penetration tester's machine targeting a machine with the IP address of 192.168.1.106:
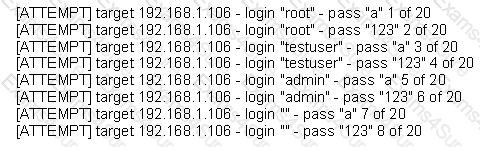
What is most likely taking place?
An attacker uses a communication channel within an operating system that is neither designed nor intended to transfer information. What is the name of the communications channel?
Which technical characteristic do Ethereal/Wireshark, TCPDump, and Snort have in common?
Which of the following business challenges could be solved by using a vulnerability scanner?
A tester is attempting to capture and analyze the traffic on a given network and realizes that the network has several switches. What could be used to successfully sniff the traffic on this switched network? (Choose three.)
Which of the following is used to indicate a single-line comment in structured query language (SQL)?
What results will the following command yiel
D.
'NMAP -sS -O -p 123-153 192.168.100.3'?Which of the following open source tools would be the best choice to scan a network for potential targets?
WPA2 uses AES for wireless data encryption at which of the following encryption levels?



