
EC0-350 Practice Questions
Ethical Hacking and Countermeasures V8
Last Update 9 hours ago
Total Questions : 878
Dive into our fully updated and stable EC0-350 practice test platform, featuring all the latest Certified Ethical Hacker exam questions added this week. Our preparation tool is more than just a ECCouncil study aid; it's a strategic advantage.
Our free Certified Ethical Hacker practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about EC0-350. Use this test to pinpoint which areas you need to focus your study on.
SNMP is a protocol used to query hosts, servers, and devices about performance or health status data. This protocol has long been used by hackers to gather great amount of information about remote hosts.
Which of the following features makes this possible? (Choose two)
You are conducting a port scan on a subnet that has ICMP blocked. You have discovered 23 live systems and after scanning each of them you notice that they all show port 21 in closed state.
What should be the next logical step that should be performed?
While footprinting a network, what port/service should you look for to attempt a zone transfer?
Exhibit
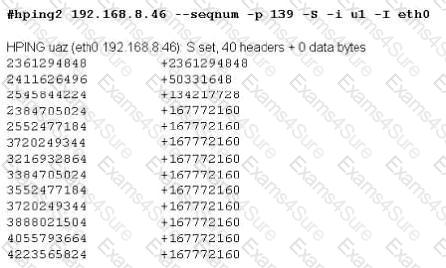
Joe Hacker runs the hping2 hacking tool to predict the target host’s sequence numbers in one of the hacking session.
What does the first and second column mean? Select two.
NSLookup is a good tool to use to gain additional information about a target network. What does the following command accomplish?
nslookup
> server
> set type =any
> ls -d
You are having problems while retrieving results after performing port scanning during internal testing. You verify that there are no security devices between you and the target system. When both stealth and connect scanning do not work, you decide to perform a NULL scan with NMAP. The first few systems scanned shows all ports open.
Which one of the following statements is probably true?
Which type of security document is written with specific step-by-step details?
When creating a security program, which approach would be used if senior management is supporting and enforcing the security policy?



