
EC0-350 Practice Questions
Ethical Hacking and Countermeasures V8
Last Update 9 hours ago
Total Questions : 878
Dive into our fully updated and stable EC0-350 practice test platform, featuring all the latest Certified Ethical Hacker exam questions added this week. Our preparation tool is more than just a ECCouncil study aid; it's a strategic advantage.
Our free Certified Ethical Hacker practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about EC0-350. Use this test to pinpoint which areas you need to focus your study on.
Which of the following types of firewall inspects only header information in network traffic?
In order to show improvement of security over time, what must be developed?
Which of the following conditions must be given to allow a tester to exploit a Cross-Site Request Forgery (CSRF) vulnerable web application?
How can you determine if an LM hash you extracted contains a password that is less than 8 characters long?
Bob wants to prevent attackers from sniffing his passwords on the wired network. Which of the following lists the best options?
Under what conditions does a secondary name server request a zone transfer from a primary name server?
Exhibit:
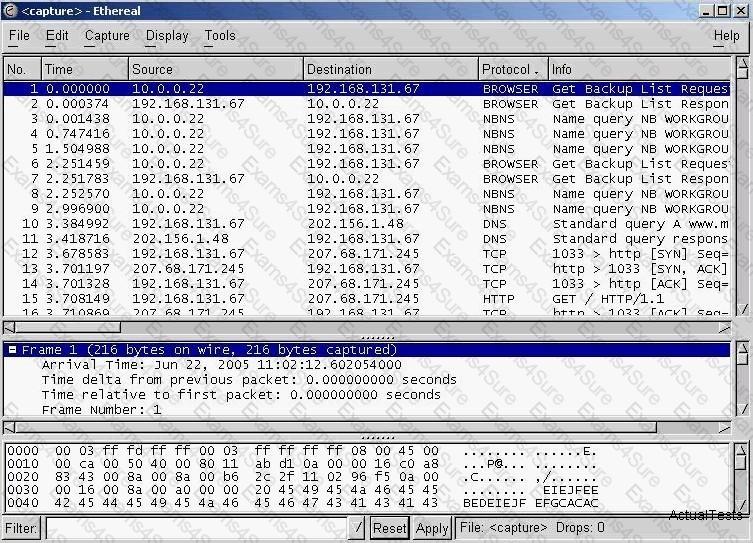
You have captured some packets in Ethereal. You want to view only packets sent from 10.0.0.22. What filter will you apply?
LM authentication is not as strong as Windows NT authentication so you may want to disable its use, because an attacker eavesdropping on network traffic will attack the weaker protocol. A successful attack can compromise the user's password. How do you disable LM authentication in Windows XP?



