
ECSAv10 Practice Questions
EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing
Last Update 7 hours ago
Total Questions : 201
Dive into our fully updated and stable ECSAv10 practice test platform, featuring all the latest ECSA exam questions added this week. Our preparation tool is more than just a ECCouncil study aid; it's a strategic advantage.
Our free ECSA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about ECSAv10. Use this test to pinpoint which areas you need to focus your study on.
Harold is a web designer who has completed a website for ghttech.net. As part of the maintenance agreement he signed with the client, Harold is performing research online and seeing how much exposure the site has received so far. Harold navigates to google.com and types in the following search.
link:www.ghttech.net
What will this search produce?
Which of the following attacks does a hacker perform in order to obtain UDDI information such as businessEntity, businesService, bindingTemplate, and tModel?
When setting up a wireless network with multiple access points, why is it important to set each access point on a different channel?
Which of the following acts related to information security in the US establish that the management of an organization is responsible for establishing and maintaining an adequate internal control structure and procedures for financial reporting?
Which of the following has an offset field that specifies the length of the header and data?
Which of the following contents of a pen testing project plan addresses the strengths, weaknesses, opportunities, and threats involved in the project?
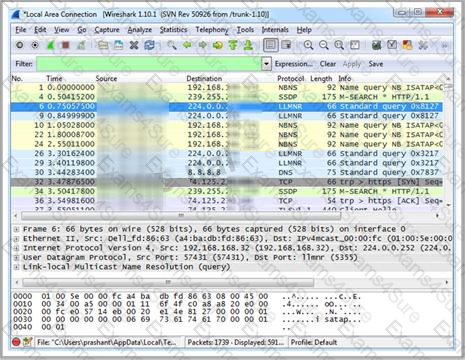
Which Wireshark filter displays all the packets where the IP address of the source host is 10.0.0.7?
Besides the policy implications of chat rooms, Internet Relay Chat (IRC) is frequented by attackers and used as a command and control mechanism. IRC normally uses which one of the following TCP ports?
A firewall’s decision to forward or reject traffic in network filtering is dependent upon which of the following?




