ECSAv10 Practice Questions
EC-Council Certified Security Analyst (ECSA) v10 : Penetration Testing
Last Update 7 hours ago
Total Questions : 201
Dive into our fully updated and stable ECSAv10 practice test platform, featuring all the latest ECSA exam questions added this week. Our preparation tool is more than just a ECCouncil study aid; it's a strategic advantage.
Our free ECSA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about ECSAv10. Use this test to pinpoint which areas you need to focus your study on.
Which one of the following Snort logger mode commands is associated to run a binary log file through Snort in sniffer mode to dump the packets to the screen?
Logs are the record of the system and network activities. Syslog protocol is used for delivering log information across an IP network. Syslog messages can be sent via which one of the following?
: 11
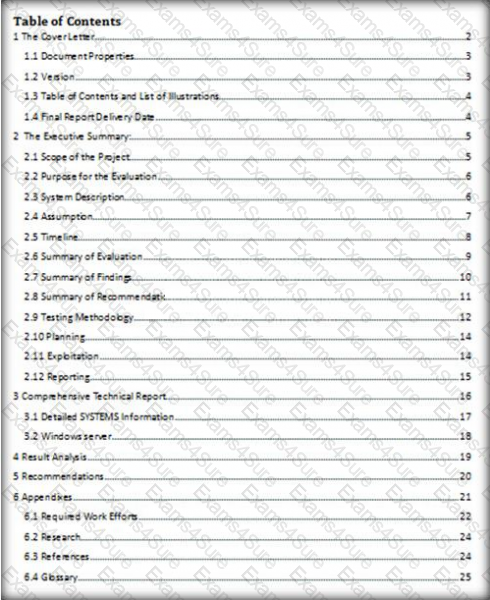
Which of the following pen testing reports provides detailed information about all the tasks performed during penetration testing?
George is the network administrator of a large Internet company on the west coast. Per corporate policy, none of the employees in the company are allowed to use FTP or SFTP programs without obtaining approval from the IT department. Few managers are using SFTP program on their computers.
Before talking to his boss, George wants to have some proof of their activity. George wants to use Ethereal to monitor network traffic, but only SFTP traffic to and from his network. What filter should George use in Ethereal?
John, a penetration tester from a pen test firm, was asked to collect information about the host file in a Windows system directory. Which of the following is the location of the host file in Window system directory?
Michael works for Kimball Construction Company as senior security analyst. As part of yearly security audit, Michael scans his network for vulnerabilities. Using Nmap, Michael conducts XMAS scan and most of the ports scanned do not give a response. In what state are these ports?
Which of the following statements is true about Multi-Layer Intrusion Detection Systems (mIDSs)?
What are the scanning techniques that are used to bypass firewall rules and logging mechanisms and disguise themselves as usual network traffic?