
FCSS_LED_AR-7.6 Practice Questions
Fortinet NSE 6 - LAN Edge 7.6 Architect
Last Update 3 days ago
Total Questions : 47
Dive into our fully updated and stable FCSS_LED_AR-7.6 practice test platform, featuring all the latest Fortinet Certified Solution Specialist exam questions added this week. Our preparation tool is more than just a Fortinet study aid; it's a strategic advantage.
Our free Fortinet Certified Solution Specialist practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about FCSS_LED_AR-7.6. Use this test to pinpoint which areas you need to focus your study on.
Which FortiGuard licenses are required for FortiLink device detection to enable device identification and vulnerability detection?
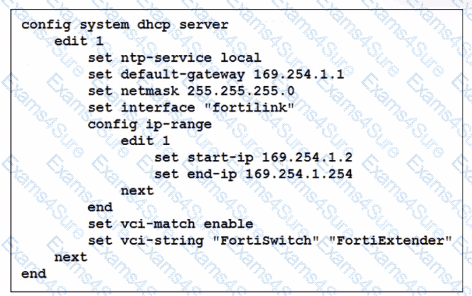
You ' ve configured the FortiLink interface, and the DHCP server is enabled by default. The resulting DHCP server settings are shown in the exhibit. What is the role of the vci-string setting in this configuration?
Which VLAN is used by FortiGate to place devices that fail to match any configured NAC policies? CRSPAN
Refer to the exhibits.
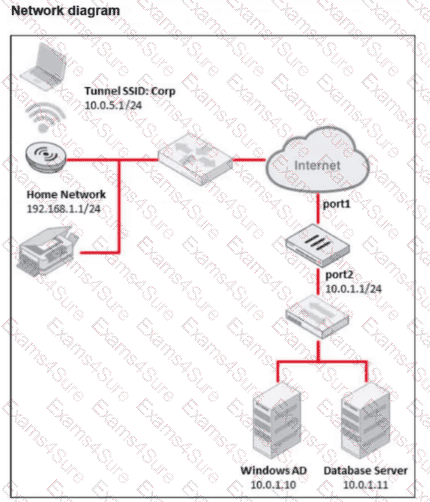
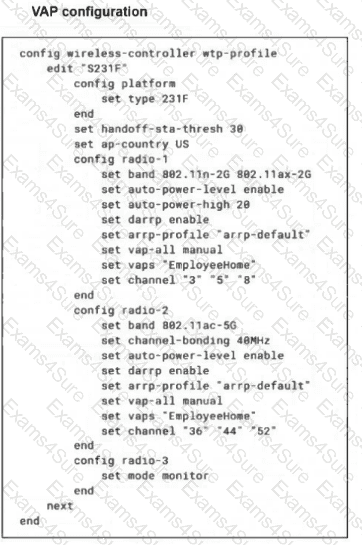
The exhibits show the WTP profile and VAP CLI configurations on FortiGate managing a remote AP. The AP is designed to grant a remote employee access to company network resources, including the database and AD servers. The employee can reach company resources but is unable to access a local printer at home. What two solutions are required to fix this issue? (Choose two answers)
In addition to requiring a FortiAnalyzer device to configure the Security Fabric, which license must be added to FortiAnalyzer to use Indicators of Compromise (IOC) rules?
Why is it critical to maintain NTP synchronization between FortiGate and FortiSwitch when FortiLink is configured?
A conference center wireless network provides guest access through a captive portal, allowing unregistered users to self-register and connect to the network. The IT team has been tasked with updating the existing configuration to enforce captive portal authentication over a secure HTTPS connection. Which two steps should the administrator take to implement this change? (Choose two.)
A network administrator connects a new FortiGate to the network, allowing it to automatically discover andI register with FortiManager.
What occurs after FortiGate retrieves the FortiManager address?
You are configuring FortiAuthenticator to integrate with FSSO for user identification. To enable FortiAuthenticator to extract user information from syslog messages and inject it into FSSO, you have configured syslog matching rules.
What is the role of syslog matching rules in the process of injecting user information into FSSO?
APs have been manually configured to connect to FortiGate over an IPsec network, and FortiGate successfully detects and authorizes them. However, the APs remain unmanaged because FortiGate is unable to establish a CAPWAP tunnel with them.
What configuration change can resolve this issue and enable FortiGate to establish the CAPWAP tunnel over the IPsec connection?



