
H12-721 Practice Questions
Huawei Certified ICT Professional - Constructing Infrastructure of Security Network
Last Update 2 days ago
Total Questions : 217
Dive into our fully updated and stable H12-721 practice test platform, featuring all the latest Huawei Certified Network Professional HCNP exam questions added this week. Our preparation tool is more than just a Huawei study aid; it's a strategic advantage.
Our free Huawei Certified Network Professional HCNP practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about H12-721. Use this test to pinpoint which areas you need to focus your study on.
The network of an enterprise is as follows. At this time, server A cannot access the web service of server
B.
The administrator performs troubleshooting and finds that there is no problem in the routing mode of firewallA.
The corresponding routing table has been established, but the firewall mode of firewall A is set. error. What is the method used by the administrator to troubleshoot the problem?
The topology diagram of the BFD-bound static route is as follows: The administrator has configured the following on firewall A: [USG9000_A] bfd [USG9000_A-bfd] quit [USG9000_A] bfd aa bind peer-ip 1.1.1.2 [USG9000_A- Bfd session-aa] discriminator local 10 [USG9000_A-bfd session-aa] discriminator remote 20 [USG9000_A-bfd session-aa] commit [USG9000_A-bfd session-aa] quit What are the correct statements about this segment?

In the application scenario of IPSec traversal by NAT, the active initiator of the firewall must configure NAT traversal, and the firewall at the other end can be configured without NAT traversal.
On the following virtual firewall network, the USG unified security gateway provides leased services to the enterprise. The VPN instance vfw1 is leased to enterprise
A.
The networking diagram is as follows. The PC C of the enterprise A external network user needs to access the intranet DMZ area server B through NAT. To achieve this requirement, what are the following key configurations?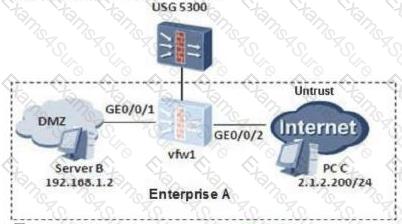
An enterprise network is as follows. Firewall A and firewall B establish an IPSec VPN. After the IPSec configuration is complete, the administrator needs to test the connectivity of the IPSec VPN. Generally, the firewall needs to simulate the traffic of the server A to access the intranet server
B.
The administrator can use which of the following ping commands.
The SSL VPN authentication login is unsuccessful and the message "Bad username or password" is displayed. Which one is wrong?
The classification of cyber-attacks includes traffic-based attacks, scanning and snooping attacks, malformed packet attacks, and special packet attacks.
Networking as shown in the figure: PC1--USG--Router--PC2. If PC1 sends a packet to PC2, what are the three modes for the USG to process fragmented packets?



