
H12-721 Practice Questions
Huawei Certified ICT Professional - Constructing Infrastructure of Security Network
Last Update 2 days ago
Total Questions : 217
Dive into our fully updated and stable H12-721 practice test platform, featuring all the latest Huawei Certified Network Professional HCNP exam questions added this week. Our preparation tool is more than just a Huawei study aid; it's a strategic advantage.
Our free Huawei Certified Network Professional HCNP practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about H12-721. Use this test to pinpoint which areas you need to focus your study on.
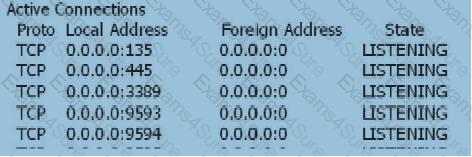
When the user's SSL VPN has been successfully authenticated, the user cannot access the Web-link resource. On the Web server, view the information as follows: netstat -anp tcp With the following information, which of the following statements is correct?
What are the scenarios in which the USG series firewall service port sends gratuitous ARPs when the following configurations are performed?
About load balancing, the following configuration is available: [USG] slb enable [USG]slb [USG-slb] rserver 1 rip 10.1.1.3 weight 32 [USG-slb] rserver 2 rip 10.1.1.4 weight 16 [USG-slb] rserver 3 rip 10.1.1.5 weight 32 [USG-slb] group test [USG-slb-group-test]metric srchash [USG-slb-group-test] add rserver 1 [USG-slb-group-test] add rserver 2 [ USG-slb-group-test] add rserver 3 Which of the following statements is correct?
When the user logs in to the virtual gateway web page and prompts “Cannot display web page”, what is the possible cause of the failure?
For IP-MAC address binding, packets with matching IP and MAC address will enter the next processing flow of the firewall. Packets that do not match IP and MAC address will be discarded.
The first packet discarding technology of Huawei Anti-DDoS devices can defend against attack packets that continuously change the source IP address or source port number. The following is incorrect about the first packet discarding technology?
The DHCP snooping function needs to maintain the binding table. What are the contents of the binding table?
Using the virtual firewall technology, users on the two VPNs can log in to their private VPNs through the Root VFW on the public network to directly access private network resources. What are the following statements about the characteristics of the VPN multi-instance service provided by the firewall?



