
IIA-CIA-Part3 Practice Questions
Internal Audit Function
Last Update 1 day ago
Total Questions : 514
Dive into our fully updated and stable IIA-CIA-Part3 practice test platform, featuring all the latest CIA exam questions added this week. Our preparation tool is more than just a IIA study aid; it's a strategic advantage.
Our free CIA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about IIA-CIA-Part3. Use this test to pinpoint which areas you need to focus your study on.
Which of the following statements is true regarding a bring-your-own-device (BYOD) environment?
Which of the following is on example of a smart device security control intended to prevent unauthorized users from gaining access to a device's data or applications?
At one organization, the specific terms of a contract require both the promisor and promisee to sign the contract in the presence of an independent witness. What is the primary role to the witness to these signatures?
An organization with global headquarters in the United States has subsidiaries in eight other nations. If the organization operates with an ethnocentric attitude, which of the following statements is true?
An internal auditor has finalized an engagement of the vendor master file. The results of the current engagement do not differ significantly from that of last year, in which several significant weaknesses in internal controls were reported. The internal auditor states in the final communication that the internal controls are as effective as that of the previous year. Which of the following elements of quality of communication could be improved?
According to IIA guidance, which of the following best describes an adequate management (audit) trail application control for the general ledger?
Which of the following statements best describes the current state of data privacy regulation?
Following an evaluation of an organization's IT controls, an internal auditor suggested improving the process where results are compared against the input. Which of the following IT controls would the Internal auditor recommend?
According to IIA guidance, which of the following statements is true regarding analytical procedures?
An organization prepares a statement of privacy to protect customers' personal information. Which of the following might violate the privacy principles?
Which of the following communication characteristics is achieved when the internal audit function avoids redundancies and excludes information that is unnecessary, insignificant, or unrelated to the engagement?
An internal auditor found the following information while reviewing the monthly financial siatements for a wholesaler of safety
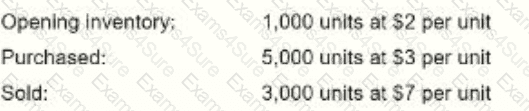
The cost of goods sold was reported at $8,500. Which of the following inventory methods was used to derive this value?
Which of the following best describes the type of control provided by a firewall?



