NSE7_SOC_AR-7.6 Practice Questions
Fortinet NSE 7 - Security Operations 7.6 Architect
Last Update 1 day ago
Total Questions : 57
Dive into our fully updated and stable NSE7_SOC_AR-7.6 practice test platform, featuring all the latest Fortinet Certified Professional Security Operations exam questions added this week. Our preparation tool is more than just a Fortinet study aid; it's a strategic advantage.
Our free Fortinet Certified Professional Security Operations practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about NSE7_SOC_AR-7.6. Use this test to pinpoint which areas you need to focus your study on.
Refer to the exhibits.
What can you conclude from analyzing the data using the threat hunting module?
Refer to Exhibit:
You are tasked with reviewing a new FortiAnalyzer deployment in a network with multiple registered logging devices. There is only one FortiAnalyzer in the topology.
Which potential problem do you observe?
Refer to the exhibit,
which shows the partial output of the MITRE ATT&CK Enterprise matrix on FortiAnalyzer.
Which two statements are true? (Choose two.)
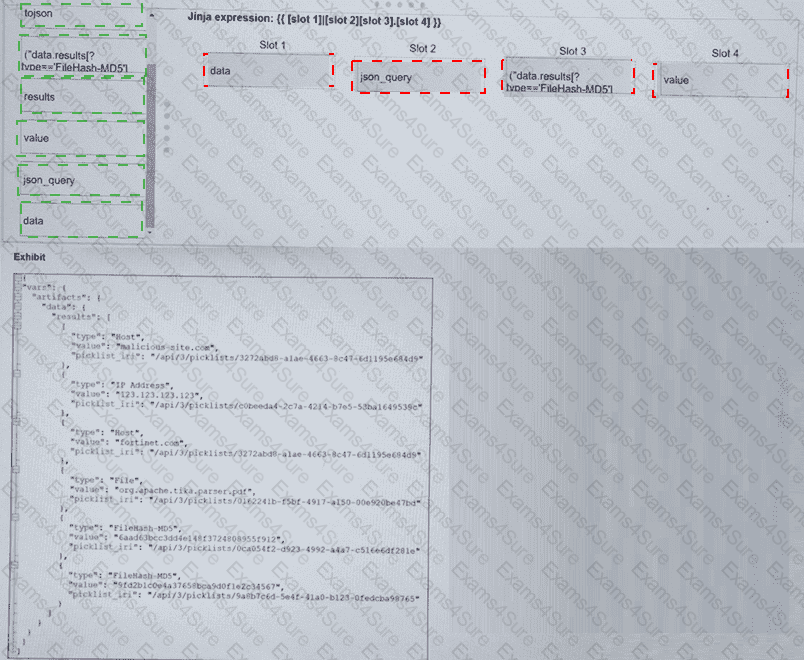
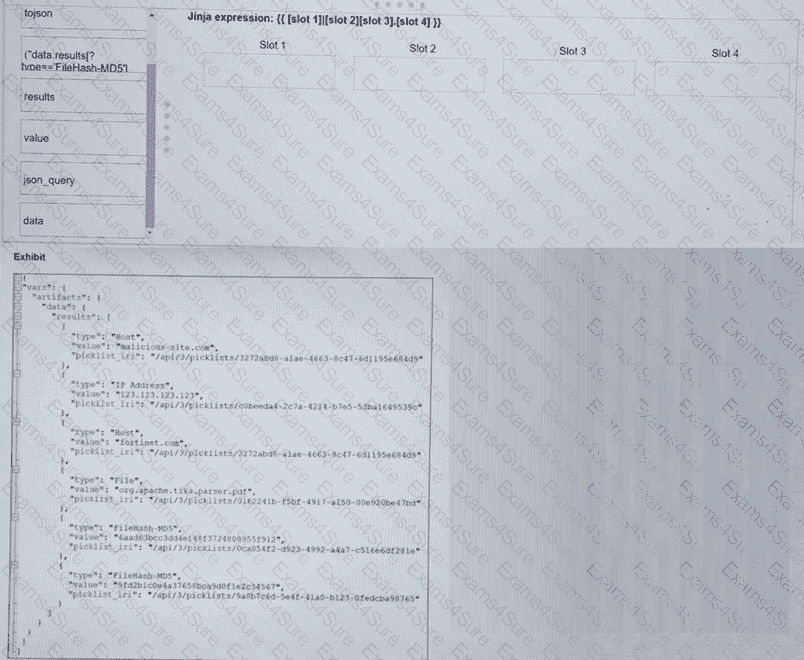
Refer to the exhibit. What is the correct Jinja expression to filter the results to show only the MD5 hash values?
{{ [slot 1] | [slot 2] [slot 3].[slot 4] }}
Select the Jinja expression in the left column, hold and drag it to a blank position on the right. Place the four correct steps in order, placing the first step in the first slot.
Based on the Pyramid of Pain model, which two statements accurately describe the value of an indicator and how difficult it is for an adversary to change? (Choose two answers)
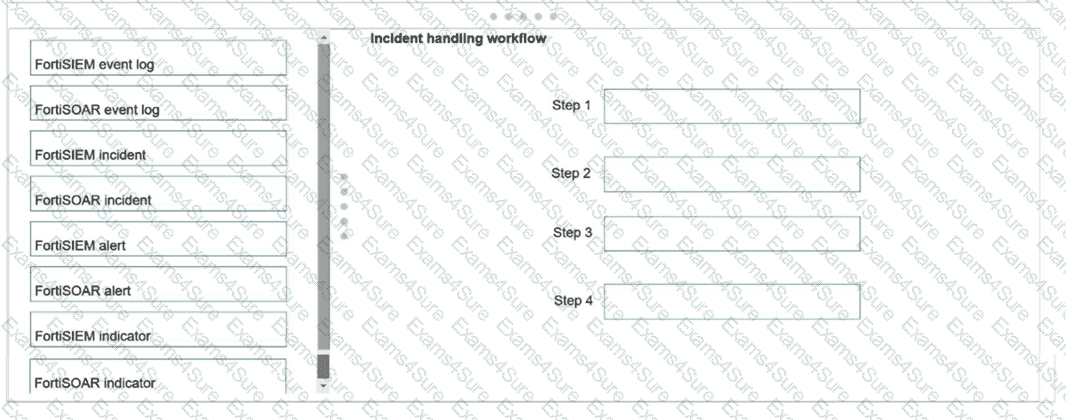
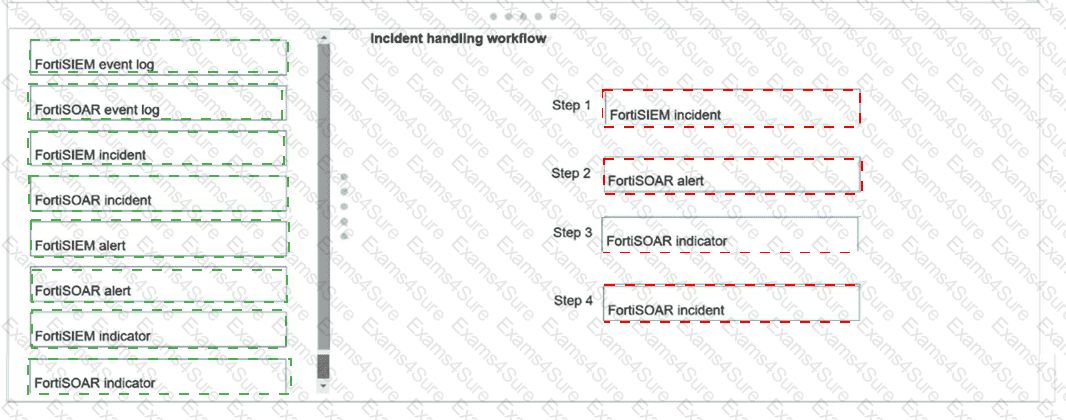
Using the default data ingestion wizard in FortiSOAR, place the incident handling workflow from FortiSIEM to FortiSOAR in the correct sequence. Select each workflow component in the left column, hold and drag it to a blank position in the column on the right. Place the four correct workflow components in order, placing the first step in the first position at the top of the column.