
312-39 Practice Questions
Certified SOC Analyst (CSA v2)
Last Update 3 days ago
Total Questions : 200
Dive into our fully updated and stable 312-39 practice test platform, featuring all the latest CSA exam questions added this week. Our preparation tool is more than just a ECCouncil study aid; it's a strategic advantage.
Our free CSA practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 312-39. Use this test to pinpoint which areas you need to focus your study on.
A financial services company implements a SIEM solution to enhance cybersecurity. Despite deployment, it fails to detect known attacks or suspicious activities. Although reports are generated, the team struggles to interpret them. Investigation shows that critical logs from firewalls, IDS, and endpoint devices are not reaching the SIEM. What is the reason the SIEM is not functioning as expected?
According to the Risk Matrix table, what will be the risk level when the probability of an attack is very high, and the impact of that attack is major?
NOTE: It is mandatory to answer the question before proceeding to the next one.
A manufacturing company is deploying a SIEM system and wants to improve both security monitoring and regulatory compliance. During planning, the team uses an output-driven approach, starting with use cases that address unauthorized access to production control systems. They configure data sources and alerts specific to this use case, ensuring actionable alerts without excessive false positives. After validating success, they move on to use cases related to supply chain disruptions and malware detection. What is the primary advantage of using an output-driven approach in SIEM deployment?
Sarah Chen is a Level 1 SOC analyst at Centex Healthcare. The SOC detected a potential data breach involving unauthorized access to patient records. Multiple departments need constant updates: Legal needs HIPAA compliance implications, HR needs to coordinate staff training responses, and the MSSP requires technical details to assist containment. Which role serves as the central point of communication between these stakeholders?
Jony, a security analyst, while monitoring IIS logs, identified events shown in the figure below.
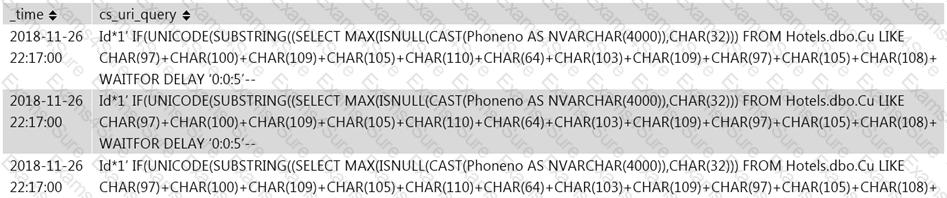
What does this event log indicate?
During a routine security audit, analysts discover several web servers still use a vulnerable third-party library flagged for a zero-day exploit. The vulnerability was identified previously and patches were deployed, but the application team rolled back patches due to instability and compatibility issues. The vulnerability remains unaddressed, and no alternative mitigations are in place. How should the security team classify this risk in the context of web application security?
A type of threatintelligent that find out the information about the attacker by misleading them is known as
.
Which of the following is a default directory in a Mac OS X that stores security-related logs?
A SOC team at a major financial institution detects unauthorized access attempts on its web application. Logs indicate the web application is compromised. To determine the exact attack technique and implement mitigation, forensic investigators assess cookie attributes (such as HttpOnly, Secure, and SameSite) for security weaknesses and track anomalous request patterns that deviate from normal user behavior. Which attack vector is the forensic team investigating?
Which of the following service provides phishing protection and content filtering to manage the Internet experience on and off your network with the acceptable use or compliance policies?



