352-011 Practice Questions
Cisco Certified Design Expert Practical Exam
Last Update 2 hours ago
Total Questions : 249
Dive into our fully updated and stable 352-011 practice test platform, featuring all the latest CCDE exam questions added this week. Our preparation tool is more than just a Cisco study aid; it's a strategic advantage.
Our free CCDE practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about 352-011. Use this test to pinpoint which areas you need to focus your study on.
An ISP provides VoIP and internet services to its customers. For security reasons, these services must be transported in different MPLS Layer 3 VPNs over the ISP core network. The customer CEs do not have the ability to segment the services using different VLANs and have only one uplink interface that does not support VLAN tagging. How should you design the network to ensure that VoIP traffic that is received from the CE goes in the VoIP VPN, and that Internet traffic goes into the Internet VPN on the ISP PE devices?
Refer to the exhibit.
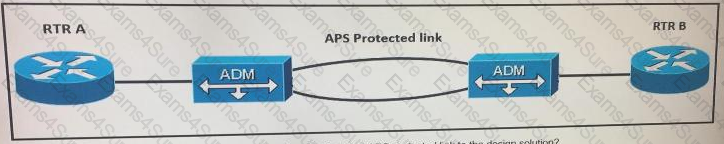
In a link failure scenario, what is a benefit of adding APS protected link to the design solution?
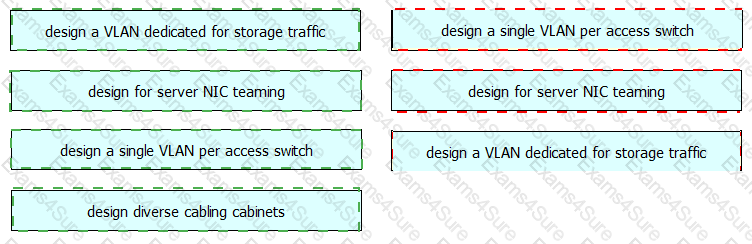
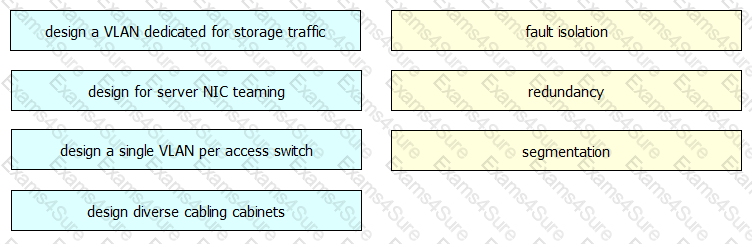
You are designing a new data center network. Drag and drop new data center requirements on the left into the appropriate design principle on the right.
You must measure the amount of traffic that a mobile packet gateway produces when mobile phones access rather than the Internet. Which action do you take to allow this visibility?
Which load balancing option for IP-only traffic is the least efficient in terms of EtherChannel physical links utilization?
You are solving a design failure on a massive Hadoop cluster network that has an application with TCP incast behavior (also known as TCP Throughput collapse) affecting its many-to-one communications with packet loss at the last-hop network device. Which metric must be measured to ensure that the network provides the best performance for this application?
Which two impacts of adding the Ip events dampening feature to a network design are true? (Choose two.)
In which two ways is a network design improved by including IP Event Dampening? (Choose two)
Which two application requirements are mandatory for traffic to receive proper treatment when placed in the priority queue? (Choose two)