
CS0-003 Practice Questions
CompTIA CyberSecurity Analyst CySA+ Certification Exam
Last Update 3 days ago
Total Questions : 486
Dive into our fully updated and stable CS0-003 practice test platform, featuring all the latest CompTIA CySA+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA CySA+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CS0-003. Use this test to pinpoint which areas you need to focus your study on.
An analyst reviews a recent government alert on new zero-day threats and finds the following CVE metrics for the most critical of the vulnerabilities:
CVSS: 3.1/AV:N/AC: L/PR:N/UI:N/S:C/C:H/I:H/A:H/E:U/RL:W/RC:R
Which of the following represents the exploit code maturity of this critical vulnerability?
The analyst reviews the following endpoint log entry:
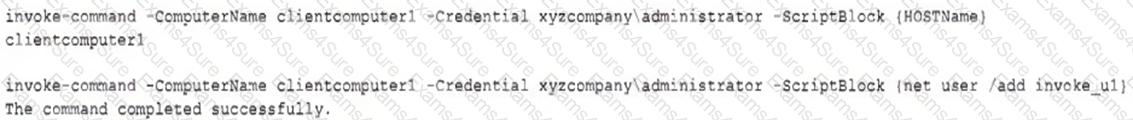
Which of the following has occurred?
An analyst is suddenly unable to enrich data from the firewall. However, the other open intelligence feeds continue to work. Which of the following is the most likely reason the firewall feed stopped working?
An analyst wants to detect outdated software packages on a server. Which of the following methodologies will achieve this objective?
An analyst is evaluating the following vulnerability report:
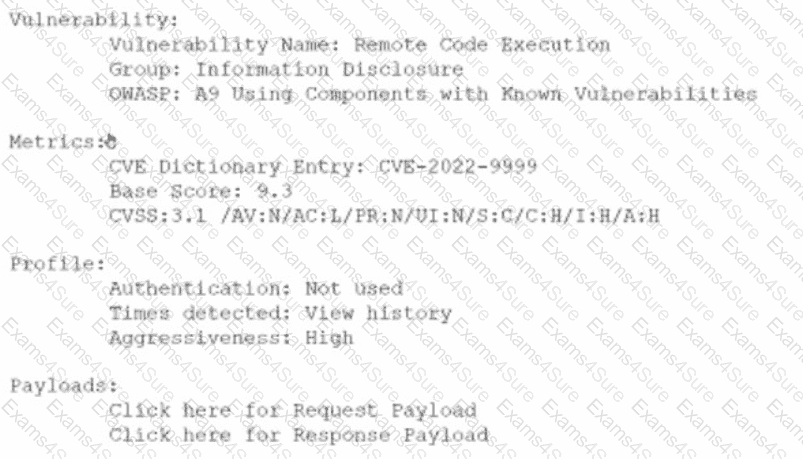
Which of the following vulnerability report sections provides information about the level of impact on data confidentiality if a successful exploitation occurs?
An analyst is remediating items associated with a recent incident. The analyst has isolated the vulnerability and is actively removing it from the system. Which of the following steps of the process does this describe?
A security analyst has identified outgoing network traffic leaving the enterprise at odd times. The traffic appears to pivot across network segments and target domain servers. The traffic is then routed to a geographic location to which the company has no association. Which of the following best describes this type of threat?
While reviewing web server logs, a security analyst found the following line:
< IMG SRC=’vbscript:msgbox( " test " )’ >
Which of the following malicious activities was attempted?
A SOC analyst identifies the following content while examining the output of a debugger command over a client-server application:
getconnection (database01, " alpha " , " AXTV. 127GdCx94GTd " ) ;
Which of the following is the most likely vulnerability in this system?
A vulnerability scan shows the following issues:
Asset Type
CVSS Score
Exploit Vector
Workstations
6.5
RDP vulnerability
Storage Server
9.0
Unauthorized access due to server application vulnerability
Firewall
8.9
Default password vulnerability
Web Server
10.0
Zero-day vulnerability (vendor working on patch)
Which of the following actions should the security analyst take first?



