
CS0-003 Practice Questions
CompTIA CyberSecurity Analyst CySA+ Certification Exam
Last Update 3 days ago
Total Questions : 486
Dive into our fully updated and stable CS0-003 practice test platform, featuring all the latest CompTIA CySA+ exam questions added this week. Our preparation tool is more than just a CompTIA study aid; it's a strategic advantage.
Our free CompTIA CySA+ practice questions crafted to reflect the domains and difficulty of the actual exam. The detailed rationales explain the 'why' behind each answer, reinforcing key concepts about CS0-003. Use this test to pinpoint which areas you need to focus your study on.
Which of the following best describes the goal of a disaster recovery exercise as preparation for possible incidents?
A vulnerability management team is unable to patch all vulnerabilities found during their weekly scans. Using the third-party scoring system described below, the team patches the most urgent vulnerabilities:
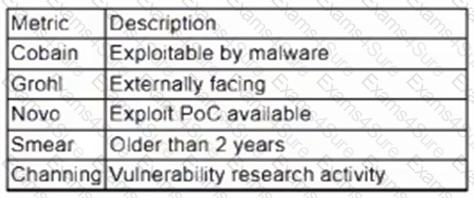
Additionally, the vulnerability management team feels that the metrics Smear and Channing are less important than the others, so these will be lower in priority. Which of the following vulnerabilities should be patched first, given the above third-party scoring system?
During a security incident at a healthcare facility, an unauthorized user downloads multiple patients’ PHI records. Which of the following is the best reason for the healthcare facility to communicate with the affected patients regarding the incident?
An analyst discovers unusual outbound connections to an IP that was previously blocked at the web proxy and firewall. Upon further investigation, it appears that the proxy and firewall rules that were in place were removed by a service account that is not recognized. Which of the following parts of the Cyber Kill Chain does this describe?
New employees in an organization have been consistently plugging in personal webcams despite the company policy prohibiting use of personal devices. The SOC manager discovers that new employees are not aware of the company policy. Which of the following will the SOC manager most likely recommend to help ensure new employees are accountable for following the company policy?
A company has the following security requirements:
. No public IPs
· All data secured at rest
. No insecure ports/protocols
After a cloud scan is completed, a security analyst receives reports that several misconfigurations are putting the company at risk. Given the following cloud scanner output:
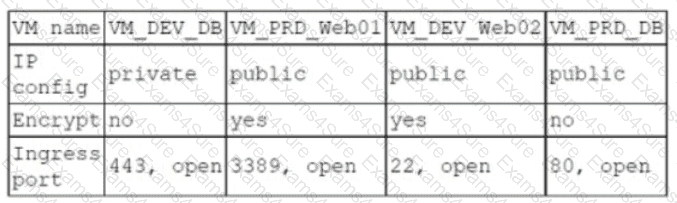
Which of the following should the analyst recommend be updated first to meet the security requirements and reduce risks?
A security analyst receives an alert for suspicious activity on a company laptop An excerpt of the log is shown below:
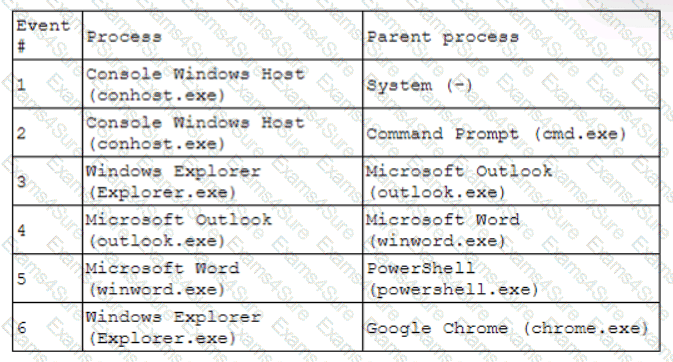
Which of the following has most likely occurred?
Which of the following is best suited for determining the methods of an adversary?
Which of the following is a nation-state actor least likely to be concerned with?
Which of the following best describes the reporting metric that should be utilized when measuring the degree to which a system, application, or user base is affected by an uptime availability outage?



